Search Results for 'Asymmetric Encryption'
Asymmetric Encryption published presentations and documents on DocSlides.
The RSA Algorithm
Rocky K. C. . Chang, . March 2014. 1. Outline. 2....
Odds and ends
Tweakable. encryption. Online Cryptography Cours...
Numbers Stations and OTP
Uncrackable Plain Text Over Short Wave Radio. Wha...
ENABLING A COST/ BENEFIT ANALYSIS
OF IMPLEMENTING . ENCRYPTION-. AT-REST USING FAIR...
Authenticated Encryption
Constructions from ciphers and MACs. Online Crypt...
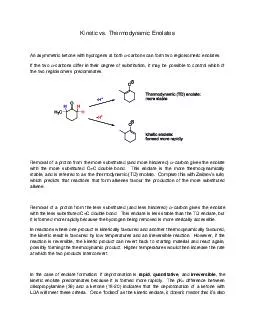
Kinetic vs. Thermodynamic Enolates
An asymmetric ketone with hydrogens at both ð...
Maggie
Wettergreen. . &. Scott Crooks. Encryption, ...
Security for Operating Systems: Cryptography, Authenticatio
CS. . 111. Operating . Systems . Peter Reiher. ...
Security in Operating Systems
CS. . 111. Operating . System Principles . Peter...
Information Security Principles course
“Cryptology” . Based of: “Cryptography and ...
Social Network Analysis
For Dummies. Yanne. . Broux. DH Summer School. L...
Relations & Their Properties:
Selected Exercises. Copyright © Peter Cappello ...
All Your Queries Are Belong to Us:
The Power of File-Injection Attacks . on Searchab...
Cryptowars
Sharon Goldberg. CS558 Network Security . Boston ...
eDOC Innovations
Revision 7 Changes and . DMCrawler. Training. Pr...
Build on GSM security
Correct problems with GSM security. Add new secur...
CRYPT
OGRAPHY. Dr. Andy Wu. BCIS . 4630 Fundamentals of...
1 CIS 5371 Cryptography
3. Private-Key . Encryption and. . Pseudorand...
Confidentiality and Privacy Controls
Chapter . 9. 9. -. 1. Learning Objectives. Identi...
Security in Computing
Chapter 2, Elementary Cryptography. Summary creat...
CRYPT
OGRAPHY. Dr. Andy Wu. BCIS . 4630 Fundamentals of...
Cryptographic Security
Presented by:. Josh Baker. October 9. th. , 2012....
Cryptographic Systems
A network LAN can be secured through:. Device har...
Cryptology
Kylie Brown. Outline. Introduction. What is Crypt...
Fully Homomorphic Encryption (FHE)
By: Matthew Eilertson. Overview. FHE, origins, wh...
Information and Computer Security
CPIS 312 . Lab 1 . 1. Classical Encryption. TRIG...
Utility Software
Describe the purpose and use of common utility so...
Legal Issues and Ethics
Chapter 24. Objectives. Explain the laws and . ru...
Deniable Functional Encryption
PKC 2016. Academia . Sinica. , Taipei, TAIWAN Mar...
DEUCE: Write-Efficient Encryption for
PCM. March 16. th. 2015. ASPLOS-XX Istanbul, Tur...
Practical and Secure Dynamic Searchable Encryption
via . Oblivious Access on Distributed Data Struct...
Overcoming SSIS Deployment and Configuration Challenges
Erik Veerman. Mentor, Solid Quality Mentors. SQL ...
Document Confidentiality
Milan Petkovic, Ray Krasinski. Structured Documen...
CryptDB
: Protecting Confidentiality with Encrypted Query...
BlindBox
: Deep . Packet Inspection . over . Encrypted . T...
Web services
security I. Uyen. Dang & Michel . Foé. Agen...
Anonymity-preserving Public-Key Encryption
Markulf Kohlweiss. Ueli. Maurer, . Cristina . On...
1/31/2014
Sandeep - Master's project proposal. 1. Secure . ...
Lattice-Based Cryptography
Vadim . Lyubashevsky. Cryptography. Allows for se...
Prof. Peter
Swire. Georgia Tech. Senior Counsel, Alston &...