Search Results for 'Asymmetric Encryption'
Asymmetric Encryption published presentations and documents on DocSlides.
CEG 2400 FALL 2012
. Chapter . 11. Network Security. 1. Security As...
Ch9QQ
T F 1.. Hacking is an example of unauthori...
AUGMENTED
AUTHENTICATION. FACE + A.I. + CONTEXT. the new cr...
Transactions Costs, Asymmetric
Information, and the Structure. of the Financial ...
Judgemental Bias and Housing Choice
Peter Scott. University of Cambridge. June 2010. ...
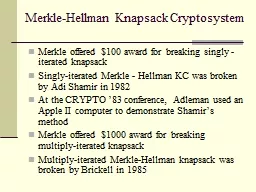
Merkle-Hellman Knapsack Cryptosystem
Merkle offered $100 award for breaking singly - i...
Mobile Device Encryption
Chris Edwards. IT Services. “All . confidential...
All Your Queries are Belong to Us:
The Power of File-Injection Attacks . on Searchab...
iO with Exponential Efficiency
Huijia. Lin (USB), . Rafael Pass . (Cornell). Ka...
Craig Gentry and
Shai Halevi. Obfuscation. China Summer School on ...
Why Cryptosystems Fail
Ross Anderson. Presented by. Su Zhang. 1. Main Id...
Discrete Methods
in . Mathematical Informatics. Lecture 3. : . Oth...
Oracle12c
Redaction . and . Advanced . Data Encryption . fo...
SSL/TLS Trends, Practices, and Futures
Brian A. McHenry, Security Solutions Architect. b...
Security and Authorization
Chapter 21. Introduction to DB Security. Secrecy:...
Encryption Methods and algorithms
David Froot. Protecting data By encryption . How ...
Design and Implementation of Privacy‑Preserving
Surveillance. Aaron . Segal. Yale University. May...
Sensitive Data
Agenda. Howard Noble – Research Support ACIT (I...
IoT -enabled Product-Service Design in
Manufacturing. the . PSYMBIOSYS 5 tussles. Domeni...
1-way String Encryption
Rainbows (a.k.a. Spectrums). Public Private Key E...
Security Awareness Training
CJIS Security Policy v5.5. Policy area 5.2. What....
CS 4740
/ CS . 6740. Network . Security. Lecture 11: . An...
CS 3700
Networks and Distributed Systems. Anonymous . Com...
Confidentiality and Privacy Controls
Chapter 9. 9-. 1. Learning Objectives. Identify a...
Intro to cryptography:
Symmetric Encryption. Cryptography. Cryptography ...
8/27/2013 4:40:35 PM
week01-crypto.ppt. 1. Introduction to Basic Crypt...
John Spaid, CTO
October 2015. What’s New in PKI and SSL?. The S...
Security & Privacy
DSC340. . Mike . Pangburn. Agenda. Security....
1 Rekeying for
Encrypted . Deduplication. Storage. Jingwei. Li...
1/31/2014
Sandeep - Master's project proposal. 1. Secure . ...
Strong Authentication using Asymmetric Keys on
Devices Controlled by You . Dr. Michael B. Jones....
Putting it all together: using multiple primitives together
Exercise 1. Say you have a signature scheme. SSch...
Don’t let backups be the
backdoor. to your security policy. . . Ryan...
Summary of Recent Pervasive Monitoring Threats
Dave Thaler. November 6, 2013. Perpass BoF - IETF...
Development of the Authentication Reliability and Security
Professor, Dr. sc. . ing. . . Viktors. . Gopejen...
Wireless Hacking
Lesson . 13. Reminder. As a reminder, remember th...
1-way String Encryption
Rainbows (a.k.a. Spectrums). Public Private Key E...
Assignment #8 – Solutions
Problem 1. Each participant . selects a random p...
Verifiable
Election. Technologies. How Elections . Should . ...
Comparative Cheap Talk
L6. Comparative cheap talk (JET 2007). Persuasion...