Search Results for 'Windows User'
Windows User published presentations and documents on DocSlides.
Innovation is at hand.Continual improvement throughinnovation. The ful
The user-friendly design of 3Mstaples which allow ...
Security Management SystemNEXSENTRY STARGAZE WITH WINDOWS NTOPERATOR
2 ENTRYTAR uses the most comprehensiveSecurity Man...
User’s Guide
Localization system StarGazer TM for Intelligent ...
SWIFT & TARGET2
Event Name. Name. Date. Presentation title – d...
Web Browsers
And Mobile Web Browsers. Guiding Questions. What ...
© Microsoft Corporation. All rights reserved.
Course objectives. Get. started. Introducing. Int...
CC3100SimpleLink
GettingStartedGuide User'sGuide LiteratureNumber:S...
Security
and . Privacy-preserving . Applicatio...
try as well as the half-rounds crown-ing two large multipaned windows.
PLAN 30-667First Floor 2240 sq.ft.Second Floor 616...
Simple Buffer
Overflow Example. Dan Fleck. CS469 Security Engin...
Buffalo Data Storage Expansion
June 2015. 1. As organizations grow the amount of...
Software Security
Chapter. 15 : . Attacking. . Compiled. Applica...
July 2013 Microsoft Security Bulletins
Jonathan Ness. Security Development Manager. Dust...
October 2013 Microsoft Security Bulletins
Jonathan Ness. Security Development Manager . Dus...
Building a
Bulletproof . Windows BitLocker. Sami Laiho - . S...
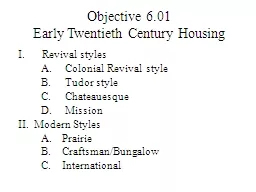
Objective 6.01
Early Twentieth Century Housing. Revival styles. ...
911 Burglary Prevention
& . Property crimes. Investigations. MECC/911...
e.g .
Click & Collect penetration variation. Some c...
Drug User Peace InitiativeStigmatising People who Use DrugsIntroductio
1 ‘Drug use’ should be taken to refer t...
Peter Kleissner
Stoned Bootkit 1. Introduction 1. About 2. Technic...
Smart Cane – P14043
Systems Design Review. Lauren Bell, Jessica Davil...
Smart Cane – P14043
Sub-Systems . Design Review. Lauren Bell, Jessica...
Smart Cane – P14043
Lauren Bell, Jessica Davila, Jake Luckman, Willia...
After the Canvass
ePledge. A . tutorial. for canvassers: . Assisti...
By Toby Reed
. E-Mail. What is E-Mail?. Email stands for ‘e...
Ryan hickling. What is an email. An email message...
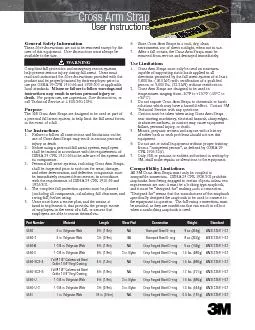
Cross Arm Strap
User Instructions Part NumberMaterialLengthWear Pa...
Design your
o. wn Room. Paper-modelling techniques to build a...
Information Security
4. Identify the . five . factors that contribute ...
7 Information Security
Introduction to Information Security. Unintention...
Microsoft Vista and Windows 7 configuration instructions:
1) On the task bar, locate the speaker icon and ri...
Shape of Caring Event
22. nd. July 2014. Kathy Branson. Director – S...
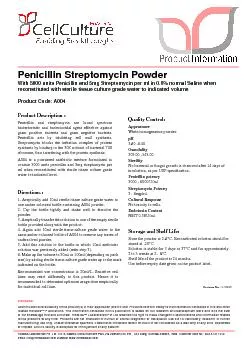
User must ensure suitability of the product(s) in their application pr
Penicillin and streptomycin are broad spectrumbact...
L-Glutamine-Penicillin-StreptomycinSolutionWith 200mM L-Glutamine, 100
Disclaimer :User must ensure suitability of the pr...
Need a lift? Want to carpool?
Characteristics of different target groups of rid...
User Manual Model:Y8POLAR STRIDE SENSOR
ENGLISHCongratulations!PolarStrideSensorBluetooth
Uni -Caster
is an Information Broadcasting Application . for ...
Catch A Ride
Ashwini, Keith, and Jarret. Overall problem and s...
Parex USA Stucco Detailsthe assembly. The designer and the user shall
PAG Non Insulated General Details PAG Insulated (H...
Linear
Submodular. Bandits . and their Application to D...