Search Results for 'Windows Security'
Windows Security published presentations and documents on DocSlides.
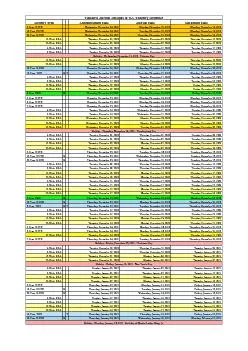
Tentative Auction Schedule of U.S. Treasury Securities
Security Type Announcement Date Auction Date Settl...
Lecture 20
Trusted Computing and Multilevel Security. modifi...
Peoplesoft
: . Building and Consuming Web Services . Program...
Module
14:. WCF Send Adapters. Overview. Lesson 1: Intro...
Developing and Consuming Services
for SharePoint. Zlatan. . Dzinic. Principal Cons...
Evolution of Thread-Level Parallelism in Desktop Applicatio
Geoffrey Blake*. , Ronald G. Dreslinski*, . Trevo...
How things work --
Errata and Contingencies. David Edfeldt. Windows ...
The Path to Continuous Availability with Windows Server 201
Gene . Chellis. , Director of Program Management....
Fiscal Policy, Poverty and Redistribution in Latin America
Nora Lustig . Tulane University . Nonresident Fel...
Rocky Heckman
Senior Security Technologist. UAC Beyond the Hype...
Why Do States
Cooperate with Each Other. C8K3K4. Because this c...
Georgia Thespian ConferenceAgreement FormHealth/Security/Conference Ru
Troupe Directors: You will need THREEcopies of ea...
Application For Employment(An Equal Opportunity Employer)
Date: Social Security Number:Telephone Number Name...
University Policy No.: Safety and Security VIOLENCE AND THREATENING
1 2.3 "Property" means the Gordon Head Campus an...
Geogia ech gia ech Information Security Center (GTISC) andgia ech
Georgia Tech Introduction Over the last year, info...
2013 In Review
Costar Technologies Sales. CohuHD. Acquisition....
1 GOOD GUYS VS BAD GUYS:
USING BIG DATA TO COUNTERACT ADVANCED THREATS . ...
Appraisal of Event Risk
SEC 320. Table of Contents. Getting Started …�...
Quantum Money from Hidden Subspaces
Scott Aaronson and . Paul Christiano. As long as ...
Counterfeiting
EHS Forensic Science. Counterfeit Millionaire. ht...
Basic Security
and Guard Duty. Professional Military Education. ...
Washington State Archives
Presented by:. October 2010. Julie Woods. Local G...
Hunter’s Cove
Home Owner’s Association (HCHOA) . Annual Meeti...
ART Program Management
under . Universal Health Coverage. Sorakij. . B...
Module
6. : . Quantifying gaps and . measuring coverage....
Factors that Reduce Spendthrift/Tightwad Scott Rick Department of Ope
MANAGEMENTDECISIONCENTER theWhartonManagement deve...
Fire Suppression Systems Birmingham AL
When fire strikes and seconds count the fire alarm...
Context Information Security
Research. Response. Assurance www.contextis.com 1...
PRIORITIES
1. Basic Approach. Classify the persons claiming ...
Chapter 18: Security Interests
in Personal Property. 1. Learning Objectives. Wha...
Spiders
by . Arjun. Table of Contents. Home sweet home. T...
Tobacconists and bars: Moving towards greater security.
CASE STUDY www.axis.comThe T-Serve project provide...
WSS X509 Certificate Token Profile 1 February 2006 Copyright
Web Services Security X.509 Certificate Token Pro...
Binding Security Tokens to
TLS Channels A. Langley , Google Inc. D. Balfanz ...
Best Home Security System Australia
http://www.thompsonbros.com.au/product.php?id=3 | ...
Introduction to Messengers of Peace
Sir Robert Baden Powell. 3. rd. International Co...
Transforming the business of
cloud. Cloud Cruiser financial analytics . for Mi...
Module
6. Service Extend Services . with . Third Parties...
Enhancing File Data Security in Linux
Operating System. . by . Integrating Secure File...
The world is rapidly changing into a global village. However, dueprodu
MAR 2013 Integrated Security Solution Fire entry s...