Search Results for 'Threats System'
Threats System published presentations and documents on DocSlides.
Information Systems Management
Part 4. MIS Security, Development, and Resources...
Offensive and Defensive Realism
March 5, 2013. Offensive and Defensive Realism. N...
Principles of Information Security,
Fourth Edition. Chapter 1. Introduction to Inform...
The 4th Manfred Lachs Conference
on Conflicts in Space and The Rule of Law. McGill ...
[eBOOK]-Computer Viruses, Worms, Data Diddlers, Killer Programs, and Other Threats to Your System: What They Are, How They Work, and How to Defend Your PC, Ma
The Desired Brand Effect Stand Out in a Saturated ...
Threats to Modern Cryptography and State-of-the-Art
Solutions. Kenny Paterson. Information Security Gr...
Module 16: Network Security Fundamentals
Introduction to Networks v7.0 (ITN). Module Object...
LM8. Wireless Security Audit
Dr. Liang Zhao. Road Map. 2. Introduction. Securit...
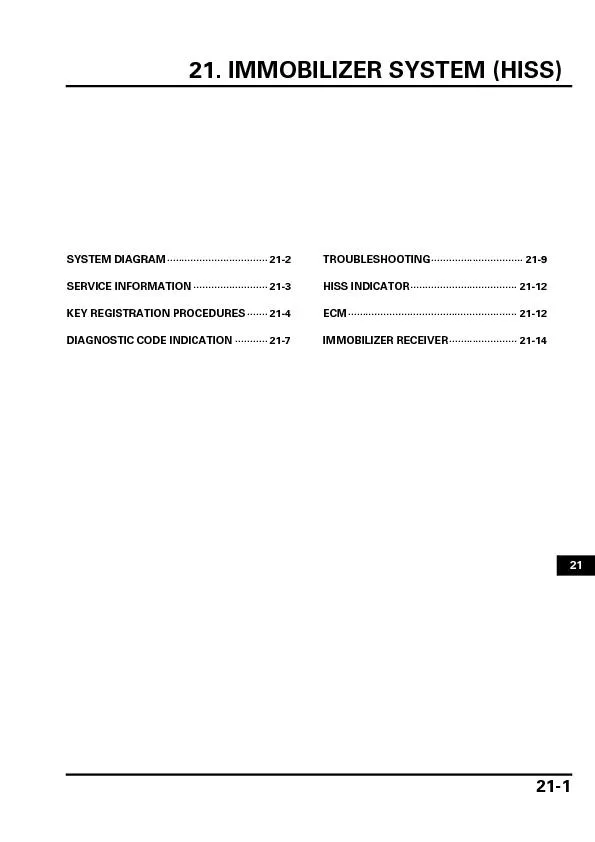
21. IMMOBILIZER SYSTEM (HISS)SYSTEM DIAGRAM
21-1 21 IMMOBILIZER SYSTEM (HISS) 21-2 IMMOBILIZER...
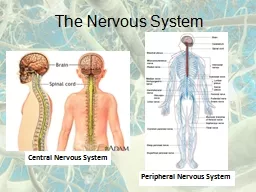
The Nervous System Central Nervous System Peripheral Nervous System
The Nervous System Central Nervous System Periphe...
The Nomad Power System PDF, eBook by Hank Tharp
Discover the truth and the facts about The Nomad P...
Endocrine system The endocrine system vs. nervous system
The nervous system and endocrine system controls d...
Sophos PureMessage for Microsoft Exchange Antivirus and antispam protection for your Microsoft Exchange servers Sophos PureMessage for Microsoft Exchange guards against emailborne threats such as spam
Control information sent and received both intern...
Unauthorized Origin Crossing on Mobile Platforms Threats and Mitigation Rui Wang Microsoft Research ruiwanmicrosoft
com Luyi Xing Indiana University luyixingindianaed...
A Worst Practices Guide to Insider Threats Lessons from Past Mistakes Matthew Bunn and Scott D
Sagan AMERICAN ACADEMY OF ARTS SCIENCES brPage 3...
Sealing Abandoned Wells The risk of abandoned wells An unused water well commonly known as an abandoned well poses one of the greatest threats to groundwater
It provides a direct unhindered route for polluta...
Note Norwegian Computing CenterApplied Research and Development Cheating in Online Games Threats and Solution Version
0 Knut Hkon T Mrch Copyright Norsk Regnesentral b...
Endpoint Protection Advanced Highlights Effective and efcient protection with minimal impact Block webborne threats before theyre downloaded Enforce safe and productive web usage using webcontent lte
Our Endpoint Protection Advanced provides you wit...
Server Protection Highlights Protects Windows Linux and UNIX systems from the latest threats Supports vSphere HyperV and XenServer Minimizes resource use for optimal server performance Includes Antiv
Frequent lightweight de64257nition updates keep y...
Index Policy Note Standing up to threats to digital freedom an we keep the internet free November As key stakeholders from government industry and civil society come together at the Internet Govern
Introduction The future of the internet is at sta...
Public Complacency under Repeated Emergency Threats Some Empirical Evidence XiaoHu Wang Naim Kapucu University of Central Florida ABSTRACT In the summer of the state of Florida was struck by four ma
Using data collected from jurisdictions experienc...
VOGELWELT Populations ecology and threats to the
Green Gerard Rocamora Norbert Schffer Green R E ...
NO AND NO The president made veto threats while Republ
PAGE A15 VOL CLXIV No 56753 57513 2015 The New...
THE MICHIGAN PENAL CODE EXCERPT Act of CHAPTER XXXIV
213 Malicious threats to extort money Sec 213 Mali...
Safeguarding your network assets and data from today’s threats isn’t easy. You ...
need detailed visibility into all your network lay...
Living in the world of cybersecurity is tough. Threats are growing, and the good guys ...
are often out-gunned. With attack vectors becoming...
Bills Committee on Trade Marks BillsRelief from Groundless Threats of
harmful effect that the issue of threats of this c...
IP groundless threats provisions
- why reform is required The Law Commission has ...
HONEYSUCKLES
MAJOR THREATS TOMIDWESTERN WOODLANDSLafayette: 608...
HONEYSUCKLES
MAJOR THREATS TOMIDWESTERN WOODLANDSLafayette: 608...
Andre Le Sage, “Africa’s Irregular Security Threats: Challe
�� Amy Belasco, “The Cost of Iraq, Afghanist...
HORTOMMUNIATION
JoTT 4(15): 3401–3409 Status, threats and co...
Chapter 2
Environment Scanning and Importance of Business E...
Develop future
s. cenarios. Phase II. Systemic risk and vulnerab...
BOMB THREAT CHECKLIST FOR PHONED THREATS (To be completed after contac
: 1. When is the bomb going to explode? __________...
essay, natural explanations for most of the Plagues are proposed and a
Plagues represent threats to the human control of...
Overview of the Six Step Planning Process
Introduction and Purpose. Schools . Provide . saf...
Elevation of Privilege
The easy way to threat model . Adam Shostack. Mic...



![[eBOOK]-Computer Viruses, Worms, Data Diddlers, Killer Programs, and Other Threats to Your System: What They Are, How They Work, and How to Defend Your PC, Ma](https://thumbs.docslides.com/986270/ebook-computer-viruses-worms-data-diddlers-killer-programs-and-other-threats-to-your-system-what-they-are-how-they-work-and-how-to-defend-your-pc-ma.jpg)