Search Results for 'Software Legal'
Software Legal published presentations and documents on DocSlides.
Custody and Parenting Time
. Susan R. Harvey. Assistant Prosecuting Attorn...
the Convention is most likely to work its way into the American legal
e bulk of norms reflecting the rights of women in ...
Page 1A6.94Razorbill Alca torda (breeding)1. Status in UK
Biological status Legal status Conservation status...
CLARIN licensing schemes
Anje Müller Gjesdal & Gunn . Inger. Lyse, U...
REAMS software: This software calculates potential rigoals, and includ
are included in REAMS. REAMS software is used to d...
CONCRETE SOFTWARE SOLUTIONS PVT. LTD.
A leading Digital Marketing Firm In India. DIGITA...
Based Economic Model for
REARM: A Reuse - Software Reference Architecture...
Law School Clinical Programs Serving Veterans
Vet Law 2014. Veterans Law School Clinics: A Snap...
IMPORTANT STUDENT REASSIGNMENT INFORMATION
You mustrequestParent/Legal Guardian must be perma...
This machine uses a laser that burns through the material.
diameter and is 60W (watts) of power, . this mean...
The informal
,. free association . of software . developers ....
Telehealth Equipment
Enabling . Successful Telehealth Encounters. Endp...
Rebutting the Myths About Race and the Death The best models which Bal
Legal Director, Criminal Justice Legal Foundati...
Wayne Coleman
FTZ Networks. President. wcoleman@ftznetworks.com...
1 CITES
and Food for Forests. CITES Secretariat. Conventi...
Chapter 11 Receiverships
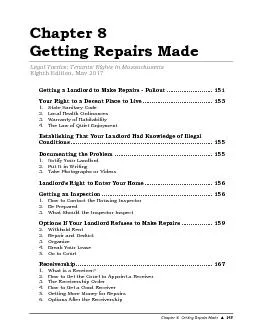
177 Legal Tactics: Tenants' Rights in Massachusett...
AREAS OF EXPERTISE
Keyboard skills Office software Administration Rec...
Make Your Summer Experience a Success
getting it right: communicating . with your supe...
Understanding the Value of Your CAR Membership
From the Colorado Association of REALTORS. ®. 5 ...
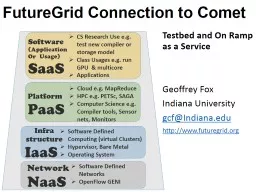
FutureGrid Connection to Comet
Testbed and On Ramp as a Service. Geoffrey . Fox....
Chapter
10:. Project Communications Management. Note: See...
COMPASS Software
System Navigation and Test Launch . COMPASS Custo...
Chapter 17 Component-based software engineering
Lecture 1. 1. Chapter 17 Software reuse. Topics c...
CSE4701
Midterm Exam Statistics . (Spr15). Worry a lot!. ...
Discuss the use of software-based training methods
3.3.4. The aim of this presentation. As this is a...
Presentation Software-Group Assignment
Lindsay Hartgraves, . Kaci. Barry . E-Material: ...
eSolutions Service Desk
IT Services for Students. http://intranet.monash....
COMPUTER ARCHITECTURE
JC Harambearachchi. Recommended Text. 1 Computer ...
Hardware vs. Software
A “Java Fun For Everyone” Interactive Quiz. W...
Myths about MOOCs and
Software Engineering Education. Armando . Fox &am...
Computing Degree Programs at Winthrop University
Winthrop Day 2015. Are there computing jobs . ava...
Lecture
11. Malicious Software. modified from slides of ....
Lecture 14
Malicious Software (. cont. ). modified from slid...
Computer Terms
Part 7(Computer Engineers). Computer engineers co...
Internal/External Computer
Components. Kim . Roselli. . Emily . Mross. What...
Objectives Overview
Discovering Computers 2012: Chapter 15. 2. See Pa...
Creating Computer Science for All Students
Mark Guzdial. School of Interactive Computing. St...
Chapter 14
Computer Security Threats. Dave Bremer. Otago Pol...
Computer Security: Principles and Practice
EECS710: Information Security. Professor Hossein ...
Ethical and Legal Aspects of Computer Security
Computer Crime/Cybercrime. “Computer crime, or ...