Search Results for 'Security Vulnerability'
Security Vulnerability published presentations and documents on DocSlides.
There is no greater assurance than that which is found in r
Who I am . in . Christ. I am Secure in Christ. I ...
Users Get Routed: Traffic Correlation on Tor by Realistic A
Aaron Johnson. 1 . . Chris Wacek. 2. . Rob J...
Scalable Parametric Verification of Secure Systems:
How to Verify Reference Monitors without Worrying...
Empowering Youth Advocates with Data and Advocacy Skills
Improving availability of RH/FP services and supp...
IJCSNS International Journal of Computer Science and Network Security,
Figure 1- SBML with Uncoordinated Checkpoint To al...
IJCSNS International Journal of Computer Science and Network Security,
Manuscript revised May 20, 2008(GQM) Abdul Azim A...
Jackie Dooley
Program Officer, OCLC Research. & President, ...
Outline (Draft) nderutilised Crops for Food Security and Poverty Alle
more recent origin will generate the same external...
SENTENCING
What do we know about sentencing?. Excerpt from t...
Food Security and
Sociopolitical Stability . Christopher B. Barrett...
Globalized (in)Security:the Field andthe Ban-opticonDidier Bigo**Intr
article didier-def CCC-reimp.qxp 03/07/2006 13:0...
3GPP TSG SA WG3 Security S3z000037 Ad-hoc meeting S3#15bis Munich, 8-
3GPP CN1 455ge/09/TR/00/021 Issue 1 British Tele...
Welcome
Cyber Security for Small . and Medium Business, N...
Presentation at the Security and Standards Track
ConnectivityWeek. Conference, June 11, 2009. Guy...
Steve Frederick
December 2012. Summit 2012 Trending Topics . and ...
Brian Carter
May 2012. WebFOCUS . 8. 1. Core Mission & Phi...
The Iraq War, the United Nations Security Council, and the Legitimacy
YAMASHITA, Hikaru Introduction The Iraq War, whi...
Clery Act Compliance
Training. Lisa Carickhoff. Clery Compliance Offic...
A Presentation
on. “Recognition of Alphanumeric Character and...
Alternatives to PKI-based SSL
on the web. Dr. István Zsolt Berta. www.berta.hu...
Attachment:
Close observation . Clinical applications. John R...
Chapter 3
. Middle Earth and . Three Great Debates . in In...
Android Security
CEG436: Mobile Computing. Prabhaker. . Mateti. S...
Android
The most exploitable . smartphone. on the market...
Presenter:
Suzanna Schmeelk. Course: . E6998 . Date: . Dece...
Android Security Enforcement
and Refinement. Android Applications --- Example....
Aurasium
: Practical Policy Enforcement for Android Applic...
U.N. Security Council
A FTER THE endorsed a six-point diplomatic plan ...
Ensuring the Safety of all those that put their trust in th
.. Transit . Protective Services. Our . Mission S...
Baby Biometrics
By: Danielle, Laine, Taylor, & Celeste . Miss...
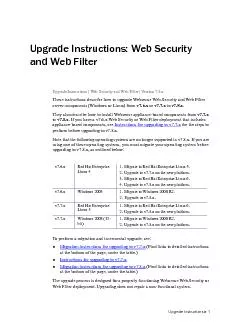
Upgrade Instructions Upgrade Instructions: Web Security and Web Filter
for the steps to perform before upgrading to v7.8...
Security Descriptions Extension for Media Streams
. (draft-zhou-mmusic-sdes-keymod-00). ...
To: UN Ambassadors of State Parties to the Rome Statute of the ICC, Me
Security Council (UNSC) unanimously passed Resolut...
Useful Computer Security
16 www.computer.org/internet/IEEE INTERNET COMPUTI...
Energy Security Initiativeat BROOKINGS
October 2014 Policy Brief 14-05 Business As Usual ...
Support for today’s
n°1 topic …. Anticipating Burn-out. How to ant...
Germany: Status Quo
Dr. Georg Heidenreich. IHE Deutschland e.V.. Over...
African Security Review 16.2
Poverty, pipeline vandalisation/explosion and huma...
Step up monitoring or install a security camera in areas where there i
• Organize a “School Watch” to enco...
VAST Program combines
Highlights • Each application security ex...