Search Results for 'Security Vendor'
Security Vendor published presentations and documents on DocSlides.
Making Leaders Successful Every Day August Wipro Consulting Services Can Wipro Finally Crack The Code by Stephanie Moore for Sourcing Vendor Management Professionals Forrester Research Inc
All rights reserved Forrester Forrester Wave Role...
Throgs Neck Ny Security Camera Installations
IP cameras are very popular nowadays and they are ...
Exploiting Open Functionality in SMSCapable Cellular Networks William Enck Patrick Traynor Patrick McDaniel and Thomas La Porta Systems and Internet Infrastructure Security Laboratory Department of C
psuedu ABSTRACT Cellular networks are a critical c...
UHIOHFWLQJDFXVWRPHUVHSHULHQFH Product Protected Legitimate accuracy Total Accuracy Kaspersky Small Office Security Symantec Endpoint Protection Small Business Edition Sophos Anti Virus Busines
5 98 AAA Sophos Anti Virus Business 958 92 AA Tren...
Abstract Buffer overflows have been the most common form of security vulnerability for the last ten years
More over buffer overflow vulnerabilities dominat...
RECENT ADVANCES in EACTIVITIES INFORMATION SECURITY and PRIVACY ISSN
brPage 1br RECENT ADVANCES in EACTIVITIES INFORMAT...
Sophos Endpoint Security and Control standalone startup guide
3 Product version June 2014 Document date brPage 2...
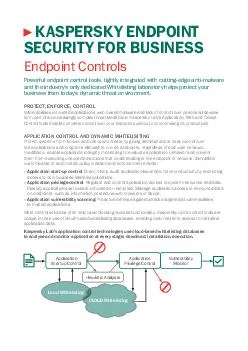
Kasperskys Application Control with Dynamic Whitelisting technology strengthens companies security stance by enabling IT administrators to set policies that allow block or regulate application or app
Equipped with these technologies organizations ca...
VNetLab An Approach for Realizing Logically Isolated Networks for Security Experiments Weiqing Sun Varun Katta Kumar Krishna R
Sekar Department of Computer Science Stony Brook ...
P Page P Application by an INDIVIDUAL FOR A NSW SECURITY LICENCE under the Mutual Recognition Act andor TransTasman Mutual Recognition Act Please use a BLACK or BLUE PEN
Print clearly within the boxes in CAPITAL LETTERS...
The Emperors New Password Manager Security Analysis of Webbased Password Managers Zhiwei Li Warren He Devdatta Akhawe Dawn Song University of California Berkeley Abstract We conduct a security analys
Unlike local password managers webbased password ...
AppsPlayground Automatic Security Analysis of Smartphone Applications Vaibhav Rastogi Yan Chen and William Enck Northwestern University North Carolina State University vrastogiu
northwesternedu ychennorthwesternedu enckcsncsuedu...
Online data storage using implicit security Abhishek Parakh Subhash Kak Computer Science Department Oklahoma State University Stillwater OK USA article info Article history Received October Recei
We describe the use of a data partitioning scheme...
Abstract Buffer overflows have been the most common form of security vulnerability for the last ten years
More over buffer overflow vulnerabilities dominat...
Laboratory for Computer Security Education Buffer Overow Vulnerability Lab Copyright Wenliang Du Syracuse University
The development of this document is funded by the...
Guest Editor Raul Siles is the guest editor for this issue of OUCH Raul is the founder of and a senior security analyst at Taddong and also a SANS author instructor and security passionate
You can follow Raul on Twitter at taddong and on ...
Annex C Approved Random Number Generators for FIPS PUB Security Requirements for Cryptographic Modules February Draft Randall J
Easter Carolyn French Information Technology Labo...
Your Social Security Number And Card Your Social Security Number And Card A Social Security number is important because you need it to get a job collect Social Security benets and receive some other
Many other businesses such as banks and credit co...
Efcient Algorithms to Solve Bayesian Stackelberg Games for Security Applications Praveen Paruchuri Jonathan P
Pearce Janusz Marecki Milind Tambe Fernando Ordon...
Bayesian Stackelberg Games and Their Application for Security at Los Angeles International Airport MANISH JAIN JAMES PITA MILIND TAMBE FERNANDO ORD NEZ PRAVEEN PARUCHURI SARIT KRAUS University of Sou
jain jpita tambe fordon uscedu Intelligent Automa...
Intrusion Detection via Static Analysis Da vid agner
C Berk ele Dre Dean Xer ox ARC Abstrac...
Building Security In Editor Gary McGraw gemcigital
com sourcecode security analysis with static analy...
Improving Application Security with Data Flow Assertions Alexander Yip Xi Wang Nickolai Zeldovich and M
Frans Kaashoek Massachusetts Institute of Technol...
Nokia Siemens Networks Policy and Government Relations Security of Telecommunication Networks RNLDLHPHQVHWZRUNVHOLHIV he Internet and therefore the telecommunications networks on which it relies on a
elecommunication ne works enabl and link other cr...
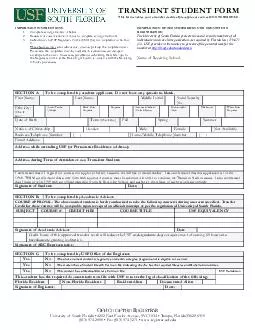
The University of South Florida protects the social security numbers of all individuals which are in its possession
As required by Florida law 119071 5 USF provides ...
WORLD HEALTH ORGANIZATION GUIDING PRINCIPLES TO ENSURE INJECTION DEVICE SECURITY Injections are the most common health care procedure worldwide
In developing and transitional countries alone so...
Model Policy on Collection of Dues and Repossession of Security
Introduction The debt collection policy of the ba...
Target Applications The Cx devices are designed to operate as simple coprocessors at maximum performance public key calculator mode or as hardware security modulessecure key management modules
When operating as a public key calculator the dev...
Exploring the characteristics of Internet security breaches that impact the market value of breached rms Francis K
AndohBaidoo KwekuMuata OseiBryson Department of I...
An Analysis of Private Browsing Modes in Modern Browsers Gaurav Aggarwal Elie Bursztein Stanford University Collin Jackson CMU Dan Boneh Stanford University Abstract We study the security and privacy
We 64257rst pro pose a clean de64257nition of the...
over Government Pension Offset A law that affects spouses and widows or widowers If you receive a pension from a federal state or local government based on work where you did not pay Social Security
This fact sheet provides answers to questions you...
I understand DMV will cancel or suspend my permit license or ID if I make any false statement or show false evidence of age identity legal presence Social Security number full legal name andor reside
If I am convicted of such acts I can be fined and...
Redesigned Endo Clip III mm Clip Applier TECHNICAL BROCHURE The Endo Clip III mm underwent a redesign that yielded improvements in clip security and jaw stability
The critical ligation function has been improved ...
Camera Security Nashville
Smartvue is all about innovation. Our new line of ...
New Security Concepts for Future Generation Automotive Electronic Control Units From the EVITA project to series applications in engine control units Oliver Bubeck and Vincent Bourgeois RobertBosch G
bubeckdeboschcom vincentbourgeoisfrboschcom Abstra...
Finite State Machine Parsing for Internet Protocols Faster Than You Think Robert David Graham Errata Security robert david grahamyahoo
com Peter C Johnson Department of Computer Science...
Control for Stability in Interconnected Power Systems ABSTRACT The increase in size and com plexity of interconnected power systems coupled with industlys commitment to max imum security at minimum c
These control devices ensure that the system is a...
Abstract Buffer overflows have been the most common form of security vulnerability for the last ten years
More over buffer overflow vulnerabilities dominat...
Prevent identity theftprotect your Social Security number UHSDUHGHVSHFLDOOIRUDQGDRUNHU www
socialsecuritygov WANDA WORKER 456 ANYWHERE AVENUE...