Search Results for 'Security Pursuant'
Security Pursuant published presentations and documents on DocSlides.
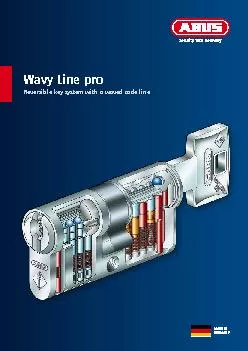
Consulting and planningStructured and thorough planning is the basis o
Security you can trustThe marine museum OZEANEUM i...
by Jim Hightower Where's the Department of Homeland Security when we r
only evasive answers, so they got to organizing, w...
Snart får vi nya rutiner för löner och förmåner.
Sverige är först ut.. Date Created: [YYYY-MM-DD...
Security Evaluation of an
Organization. TA. Md. . Morshedul. Islam. Proce...
Janna
Miletzki. , LSE, Human Geography. Refugees in a S...
Improving Application Security with Data Flow Assertions
Yip, X. Wang, N. . Zeldovich. , M. F. . Kaashoek....
Network Security Essentials
Fifth Edition. by William Stallings. Chapter 1. I...
Cryptography and Network Security
William Stallings, 6. th. Ed. . Chapter 1. Overv...
Introduction to Computer and
Network Security. Chapter #1 in the text book ( S...
Chapter 14
Computer Security Threats. Seventh Edition. By Wi...
CS457 – Introduction to Information Systems Security
Cryptography 1a. Elias Athanasopoulos. elathan@ic...
Chapter 7: Assuring Safety and Security in Healthcare Inst
Safety and Security – Risk?. Health facilities ...
How do we assign words meaning?
Connotation vs. Denotation . SWBAT. Define connot...
The Electoral College
Used for presidential elections. Framers had conc...
Mobile Threats and Attacks
Possible attack threats to mobile devices. Networ...
Attackers Vs. Defenders: Restoring the Equilibrium
Ron Meyran. Director of Security Marketing. Janua...
Lecture
14. Intrusion Detection. modified from slides of ...
OWASP Web
Vulnerabilities . and Auditing. Not just another ...
Crisis Action Plan
Troy University Police Department Dothan Campus. ...
Modelling and Multi-Objective Optimization of Quality Attri
Rafael Olaechea, Steven Stewart, Kryzstof Czarnec...
1 ````````````````````````````````````````
AEGIS . A Fast Authenticated Encryption Algorithm...
Distributed Web Security for
Science Gateways. Jim Basney. jbasney@illinois.ed...
Securing User Access with Multi-Factor Authentication
Sarah . Fender, Director of Product Marketing . S...
Troubleshooting
Active Directory Federation Services (AD FS) and ...
Chapter 4
Authentication policy. Cyber Security for Educati...
Security of Authentication Protocols
Alexander . Potapov. Authentication definition. P...
Provide a second layer of security to access site in
Joomla. Two Factor Authentication (TFA) is a 100%...
Web Security
CS598MCC Spring 2013. Yiwei. Yang. Definition. ...
Identification, Authentication and Authorisation Issues in
Ms.. Hemali Shah. PhD Researcher. Department of ...
VPN SENTRY-
Gw. Sentry-Gw. : A . P. roject and an . Achieveme...
Your First Name and Initial Last NameYour Social Security NumberIf a J
Minnesota wages and tax withheld from W-2s, other...
IC470: Flight Scheduler Assistant
Topical . Areas: . Artificial Intelligence, Datab...
Security Through Obscurity
Clark . Thomborson. Version of. 7 December 2011. ...
Data Protection in Microsoft Azure
DCIM-B387. Ramesh Chinta Principal GPM...
International Journal of Network Security & Its Applications (IJNSA),
International Journal of Network Security & Its Ap...
Guide to Network Defense and Countermeasures
. Third . Edition. . Chapter . 12. Internet and...
OFFICE OF INPECTOR GENERALDepartment of Homeland Security Washin
For more information visit our website, www.oig.d...
Depletion of the Asset Pool
premature distributions, wastage & add backs...
1 Welcome to the Guests of ALLAH
In the name of . Allah. ,. the beneficent and the...
DESIGNATED OFFICERS (for use with the Act, the attached Checklist) ...
Purpose : wrongdoing made pursuant to The Public ...