Search Results for 'Security Methodology'
Security Methodology published presentations and documents on DocSlides.
reliability. An elected Fellow of the Association
Computer security. Code certification and proof-...
Chapter 2
Security Market Indices. Presenter. Venue. Date....
The Rich Fool
Luke 12:13-21. Robert C. Newman. The Rich Fool. T...
CALIBRATING CERRADO PHYSIOGNOMIES USING SAR AND OPTICAL IMAGES IN BRAZ
1.2. Methodology Remote Sensing data have been fre...
“Why Gun ‘Control’ is Not Enough” (Jeff McMahan)
What are his arguments?. How to evaluate them. MA...
Voices of the Hungry
A worldwide survey of people’s experience with ...
Alignment of COBIT to Botswana IT Audit Methodology
Why COBIT. G. ives . a holistically view of the I...
Global Collaboration on Automotive, ITS and Standards
ITS security – a topic for Study Group 17?. Rei...
Using block ciphers
Security for. many-time key. Online Cryptography ...
Project Kickoff
Vicki Ann Frawley, Project Director. Margaret J. ...
The University of Florida
Police . Department. A . Triple Crown Accredited ...
Protecting the Confidentiality and Integrity of Corporate a
Mobile Protection for Trustmark Insurance. Topics...
How Hospitals Protect Your Health Information
Your Health Information Privacy Rights. You can a...
Return Concepts
Presenter. Venue. Date. Why Focus on Return Conce...
TheVacuityofPostmodernist
1 Methodology. NicholasShackel Thispaperappearsin ...
Lecture 2:
Overview (. cont. ). modified from slides of . La...
Threats, Vulnerabilities, and Risks
CS . 795/895. References. . Reference 1. Big Lis...
Engineers are People Too
Adam Shostack. Microsoft. Outline. Engineering in...
Prague Of
osce.org Organization for Security and Co-operati...
Securing Your Retirement
Transforming Social Security Into a Winning Retir...
Slide Template for Module 4
Data . Storage, Backup, and Security. Learner Obj...
How I Passed the
CISSP Test. : Lessons Learned in Certification. P...
You Jichallenge for a long time to come. Its gravity can be measured b
Security Outlook of the Asia Paci c Countries and ...
Other Methodology Articles
Original publication:Journal of ParapsychologyVolu...
Coping with rational prodigals: A Theory of Social Security and Saving
NTRODUCTIONAmong the efficiency theories of social...
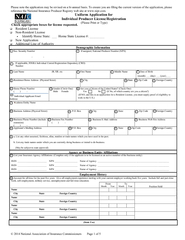
Please note the application may be revised on a bi-annual basis. To en
Soc. Security Number -...
Academic Listening
Track 5, page 5. Car Alarm. Product name?. Proble...
CONSTRUCTION BLUEPRINT READING
INTRO TO INTRUSION ALARM. CONSTRUCTION BLUEPRINT ...
FM 99.9,
Radio Virus: Exploiting FM Radio Broadcasts for M...
NOT PROTECTIVELY MARKED Page 1 of 4 NOT PROTECTIVELY MARKED Investigat
POLICY Security Classification NOT PROTECTIVELY MA...
IJCSNS International Journal of Computer Science and Network Security,
IJCSNS International Journal of Computer Science a...
Security in the
Casino Industry. Chuck Barry. cbarry@tropicanaent...
The Future of Homeland Security with the Commercial Facilit
January 10. th. , 2013. Overview. PSA’s Roles a...
Business Data Catalog
. Planning the Business Data Catalog . Configuri...
Message Integrity
CBC-MAC and NMAC. Online Cryptography Course ...
CCNA Security Overview
Updated April 2011. CCNA Security Course. Subtitl...
CCNA Security 1.1
Instructional Resource. Chapter 3 – Authenticat...
WIRELESS CCTV TV
PROJECT. . on. SUMMITED BY:-. GARGEE DEWANG...
CSIRTs
CSH5 Chapter 56. “Computer Security Incident Re...
Managing NPA & Securitization Act
A Perspective by . Mr. Sandeep . Vrat. , COO Reli...