Search Results for 'Security Keso'
Security Keso published presentations and documents on DocSlides.
Authenticated Encryption
Chosen . ciphertext. attacks. Online Cryptograph...
A Sunnier Security Outlook On Using The Cloud
Some industry analysts have predicted that within ...
PS3 Security
Julian Wechsler. Overview. Legal Issues. DMCA. Se...
Directory
Ras J. Baraka. Mayor. Touch the blue button for a...
Lecture 10
Intrusion Detection. modified from slides of . La...
Jeff Smith
Student Judicial Affairs Officer. Aims Community ...
What’s the Big Deal About a Security Clearance?
School of Science and Technology. Freshman Day. 1...
Form Approved OMB No. 0960-0062SOCIAL SECURITY ADMINISTRATION
(DO NOT WRITE IN THIS SPACE) VA DATE STAMP APPLIC...
Video Security
1 ADS-450 SwannSmart English M450IPC050411E 2 Bef...
National Capital Region (NCR)
Closed Circuit Television (CCTV) Integration Fram...
1 DESIGNING EFFICIENCIES AND PERFORMANCE INTO YOUR SECURITY
Sunday, June 20, 2010. 2. Designing Efficiencies ...
S ecurity challenges in a networked world
Theo Dimitrakos. Chief Security Researcher –Sec...
Simple Security. Simple Stability.
The Swerve Rack is a proven design that provides h...
U.S. Coast Guard
INTERTANKO North American Panel Presentation. Mr....
www.prodisplay.com | sales@prodisplay.co.uk | +44 (0)870 766 8438
PRIVACY / SECURITY ENVIRONMENTALLYFRIENDLY PRODUCT...
Terrorism
“On September the 11th, enemies of freedom comm...
is ideal suited for de-centralized, secure laser engraving of cards, s
Enhanced System Security and Quality not only pro...
U.S. Combatant Command
Intelligence, Surveillance, and . Reconnaissance ...
Workplace Violene
Threat/Interaction/Response. Leadership Review. U...
Unique tag design helps optimize performance
Enhance the productivity and security bene ts of R...
Rehabilitation after communal violence
Dr. Sajjad Hassan. Misaal. & Centre for Equi...
Cross-border citizens' network for peace, inter-communal re
Overall. . objective. To. . establish. a . hum...
Robot
companions. and . ethics. a . pragmatical. . ap...
2014 PCI DSS Meeting
OSU Business Affairs. Process Improvement Team (P...
Designing and Implementing a PCI-DSS Compliant
N. etwork using ‘Stealth’ Networks with Avaya...
Slide Heading
Cyber Security. Munish Verma, Ron Verhaalen. Erns...
Oracle BI Update
Brian Lawrence – Master Principal, Business Int...
50 States = 50 Concealed Carry Laws
How They Impact Your Business And . How You Can D...
3M Center, Building 225-4N-14www.3M.com/us/library3M, SelfCheck and Ta
a Tattle-Ta Security Strips DCD-2 Thbalanced stri...
MINISTRY OF LABOUR, EMPLOYMENT AND SOCIAL SECURITY
Application and Practice of the Settlement of . L...
Conclusion
1. Conclusion. Conclusion ...
PAUL L. SHANK P.E., C.M.
CHIEF ENGINEER . BWI MARSHALL AIRPORT. MARYLAND T...
Student and Faculty Core Orientation
©. Approved 5 23 2011, Revised . 4 22 2015. 1. ...
Ad hoc Networking Security: Solving
Node Selfishness Problem. Presented by : . Ali N...
Presented by,
. Sai. . Ch...
Food Insecurity & Older Adults
Prevalence. . Impact. Drivers. . Solutions?. Dian...
RESIDENTIAL TENANCIES ACT Entry of premises Locks and security devic
2004 Chapter R-17.1 2004 Chapter R-17.1 RE...
UCSF
Information Technology . Update on Key Topics. Oc...
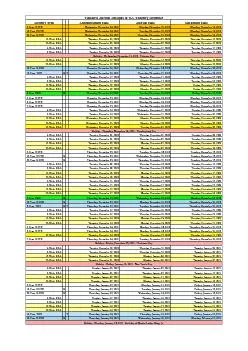
Tentative Auction Schedule of U.S. Treasury Securities
Security Type Announcement Date Auction Date Settl...
Lecture 20
Trusted Computing and Multilevel Security. modifi...