Search Results for 'Phi Malicious'
Phi Malicious published presentations and documents on DocSlides.
Screenmilker
: How to Milk Your Android Screen . for Secrets. ...
Threat Intelligence
with Open Source tools. Cornerstones of Trust 201...
Trustworthiness Management in the Social Internet of Things
Michele Nitti, Roberto . Girau. , and Luigi . Atz...
Privacy-Preserving and Truthful Detection of Packet Droppin
Abstract. Link error and malicious packet droppin...
Detecting drive-by-downloads using human behavior patterns
Alex . Crowell, Rutgers University. Computer Scie...
Secure web browsers, malicious hardware, and hardware suppo
Sam King. Browser m. otivation. Browsers most com...
Malwares, Worms, and Web Issues
IT443 – Network Security Administration. Instru...
FRAppE
: Detecting Malicious Facebook . Applications. Md...
Protocols for Multiparty Coin Toss With Dishonest Majority
Eran Omri, Bar-Ilan University. Joint work with ...
2 Timothy Introduction
The Call to Christian Perseverance. Answering . N...
Discovery of Emergent Malicious Campaigns
in Cellular Networks. Nathaniel Boggs. , Wei Wang...
Non Malicious Program Errors (Buffer Overflows)
Gabe Kanzelmeyer. CS 450. 4/14/10. Overview. What...
Word-Within-a-Word
Unit 1B. intro (into). introvert: shy. The teache...
On the Knowledge Soundness of a Cooperative Provable Data P
Multicloud. Storage. Abstract. Provable data pos...
SAT Vocabulary: Unit Five-Bad Reputations
Ignoble: Of low character. Licentious: lacking m...
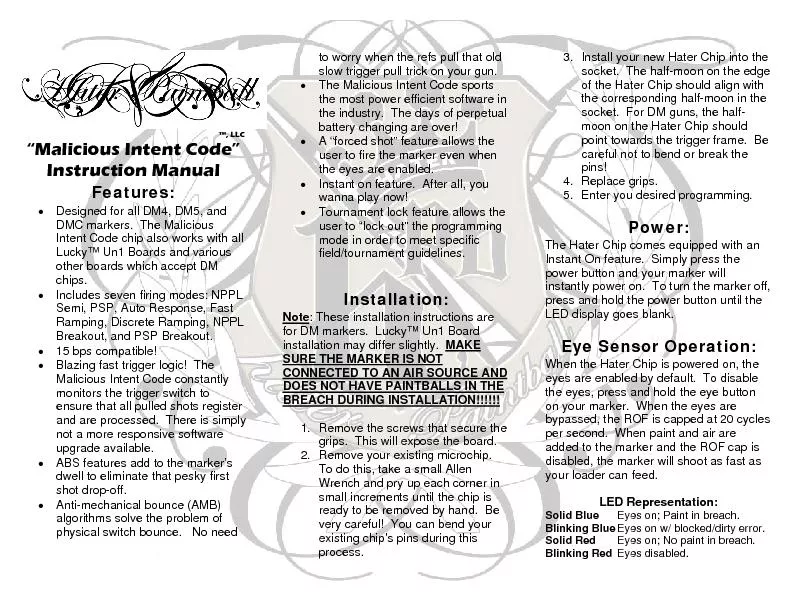
Designed for all DM4, DM5, and DMC markers. The Malicious Intent Cod
CONNECTED TO AN AIR SOURCE AND DOES NOT HAVE PAIN...
Part 4: Malware Functionality
Chapter 11: Malware Behavior. Chapter 12: Covert ...
Instructor:
Dr. . Narisa. . N. Y. . Chu. Thousand Oaks, CA, ...
Automate, or Die
Building . a Continuous Response Architecture. Co...
Malicious
Logic. What is malicious logic. Defenses. Compute...
The Rise of Ransomware
in Healthcare:. New Threats, Old Solutions. Chuck...
The Current State of
Ransomware. Ryan Archer. Sophos Sales Engineer. A...
Ransomware
t. oday: . How to protect against . Locky. and f...
I John 2:9-11
“He that . saith. he is in the light, and . ha...
UNIT 8 VOCABULARY
Theme:. Good and Bad. PREFIXES. . Bene. = ...
Malicious Code
CSH6 Chapter 16. “Malicious Code”. Robert Gue...
An Efficient Distributed Trust Model for Wireless Sensor Ne
J. Jiang, G. Han, F. . Weng. , L. Shu, M. . Guiza...
Smartening the Environment using Wireless Sensor Networks i
Presented By. Al-Sakib Khan Pathan. Department of...
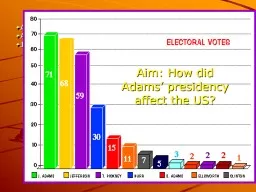
Aim: How did Adams’ presidency effect the US?
1796 Election. Adams(Federalist) vs. Jefferson (A...
Malicious Code and Application Attacks
Unit - . 2. Outline. Malicious code. Password att...
Latin Roots
“. Bene. ” and “Bon. ”. means . “Good�...
Escalation Of Ad Wars
Boosts Malware Delivery. Get free antivirus. Real...
PyCRA
: Physical Challenge-Response Authentication For ...
Trespass to Person
By. Waseem I. khan. Assistant Professor. Shri Shi...
1 Dual Execution Protocols
(for when semi-honest is only semi-good-enough). ...
E xplaining Bitcoins will be the easy part:
Email . Borne Attacks and How You Can Defend Agai...
Dynamic Trust Management for Delay Tolerant Networks and It
1. Abstract. 2. In this paper, the authors design...
Securing Embedded User Interfaces:
Android and Beyond. Franziska Roesner and . Taday...
Malicious Software
Computer Security . Peter Reiher. February. 21, ...
Towards Trustworthy Multi-Cloud Services Communities: A Tr
. -presented by-. Andreea. Sistrunk & . Jos...