Search Results for 'Message Difference(2)'
Message Difference(2) published presentations and documents on DocSlides.
Cryptography and Network Security
Chapter 2. Fifth Edition. by William Stallings . ...
CISSP
®. Common Body of . Knowledge Review:. . Crypt...
Cis 4930
Introduction to cryptography. In 60 minutes ….....
Cryptography
Lecture 1. Arpita. . Patra. Welcome to the secon...
Cryptography
Aalto . University. , . autumn. . 2012. Outline....
Cryptography Introduction
CS 465. Last Updated. : . Aug 25, 2015. Outline. ...
Topic 7:
Using cryptography in mobile computing. . Crypto...
Cryptography and Network Security
Sixth Edition. by William Stallings . Chapter 19....
Cryptography and Network Security
CSL 759. Shweta Agrawal. Course Information. 4-5 ...
Understanding Cryptology
Core Concepts. Dr. Kerry A. McKay. 1. Approved fo...
Cryptology
Kylie Brown. Outline. Introduction. What is Crypt...
Internet Security 1 (
IntSi1. ). Prof. Dr. Andreas Steffen. Institute f...
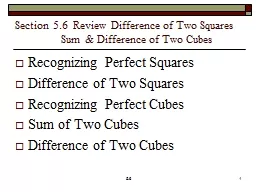
Section 5.6 Review Difference of Two Squares
Sum & Difference of Two Cubes...
Computer Systems
An Integrated Approach to Architecture and Operat...
Visual Programming
C#. Hozan. K. . Hamarashid. hozancsi@gmail.com. ...
Cryptography
Zac . Blohm. & Kenny Holtz. Importance of Al...
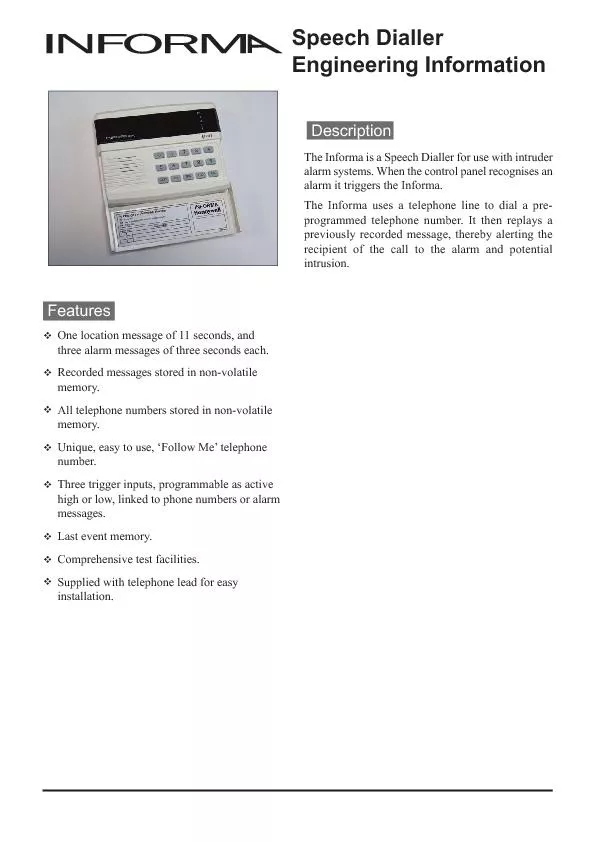
Engineering Information
location message) may be up to 11 seconds long,Typ...
CST8177 – Linux II
Services, logging, accounting. Todd Kelley. kelle...
Ch 8 - Justice
From Plato to Rawls. Plato’s Account of Justice...
Message Queue Dumping
MPI Side Document. History. MPIR and MQD were des...
Text Message Campaigns for Health Advocates
SMS 101. Agenda. What are text message campaigns?...
9:1-29
A CD of this message will be available (free of c...
Educators, Technology and 21st Century Skills: Dispelling Five MythsA
@ @ Contents A Message from the President and Dean...
Uncontrolled copy not subject to amendment
Principles of Flight. Learning Outcome 1. Underst...
Cryptography
a connection between language and mathematics. In...
Difference Between a Declaration of Independence and a Cons
We want Independence!. EXECUTIVE BRANCH. Governor...
The Many Faces of Publish/Subscribe
Erin Collins. Topics in Computer Science. Spring ...
Chapter 1 – Introduction
Part 3. 1. Cryptographic Concepts. Encryption. : ...
Encryption / Security
Victor Norman. IS333 / CS332. Spring 2014. Proble...
Cryptography
Dec 29. This Lecture. In this last lecture for nu...
Cryptography
Dan Fleck. CS 469: Security Engineering. These sl...
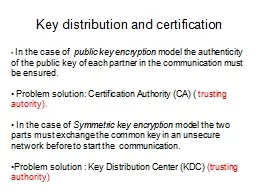
Key distribution and certification
. In the case of . public key encryption . mode...
The cognitive theory of
multimedia. learning. Based on the work of. Rich...
Chapter 8 - Social Influence and Persuasion
Two Types of Social Influence. Techniques of Soci...
Making a difference in 60 Minutes
Managing Loan Default:. Facing the Facts. . Fa...
Detecting defectors when they have incentives to manipulate
Toko. . Kiyonari. . (Aoyama . Gakuin. Universi...
1 A New Steganographic Method for Data Hiding in Microsoft
Source:. . IEEE Transactions on Information Fo...
ChatON
FAQ. Customer Consultant Guide. Version . 2.0. G...
Julian Zbogar-Smith
Senior Program Manager Lead. Information Protecti...
OTHER FEATURES and FUNCTIONS
Other features. You can do a few other actions in...