Search Results for 'Internet Manufacturer'
Internet Manufacturer published presentations and documents on DocSlides.
Domain Name System
Introduction. There are several applications that...
TM Office Comes to CA. - 2008
1. Shootout at the ICANN Corral: . Domainers vs. ...
1 Domain Registration
Copyrights and Patents. Revised: April . 29, . 20...
Gestores de …descargas…
Presentado por:. Lina . M. arcela Córdoba Mena. ...
Against Music Piracy
Paul Kelly . CIS1055.001. Music Piracy. Music Pi...
The Augmented Chef
The solution. : Using a projector and camera, the...
1 What this program is NOT
NOT. . Residential. NOT. . Resale Internet Serv...
DSL Technology
Presented by:. Eng. . Karam. Al-. sofy. What is ...
Assignment Report
ON. ‘Broadband Commercial Aspects’. Submitted...
CHAPTE
R. . 12. Access & Interconnection. Technolog...
AppraisalofFluidDynamicEfficiencyofRetreated-BladeandTurbofoilImpeller
*Correspondingauthor.E-mail:soldati@uniud.it.Phone...
Architecting a Scalable WebHosting Platform with Internet I
Thomas Deml. Principal Program Manager. Microsoft...
SynergyCardiff Business Schoolwww.cardiff.ac.uk/carbsIssue 11Winter 20
the internet has revolutionised communications. Pr...
Following on from the successful implementation of its new Internet .
Bank, Nationwide was quick to capitalise on their ...
Three important
forces. . are shaping education today…. Online...
C:\Documents and Settings\ktodd\Local Settings\Temporary Internet File
Introduction Rockeries have been included in the d...
WorkKeys Internet Version
Training. North Carolina High Schools. WorkKeys I...
Customer Case Study Medical Manufacturer Delivers Round-the-Clock BBC
Challenge EXECUTIVE SUMMARY BBC BIOCHEMICAL Indu...
Getting the Most From
Internet Advancement. National Advancement Commit...
Prof. Vincenzo Cuomo
Italian National Council of Research. Institute o...
Airborne Internet
Definition. Proposed network in which all nodes w...
Unit III
Mass Media, Political Parties and Interest Groups...
IMF Country Report No. 13/229 Under Article IV of the IMF
Internet: http://www.imf.org International Monet...
Saunacore is one of the worlds most extensive manufacturer of sauna an
saunacore profileOur mission is to manufacture the...
Alliance Lite2 & SWIFT Connectivity
Middle East Regional Conference. Javier . Pérez-...
Backafallsbyn AB
Internet: www.hven.com Tel. +46 - 418 - 44 99 99 ...
Internet Anonymity
By . Esra. . Erdin. Introduction. Types of Anony...
Section
3.5-3.6. CptS. 401. Adam Carter. Discuss Paper. ...
Remote Control of Home Appliances Using the Internet
Team DEC0905. Elie. . Abichar. . Rachel . Ayoro...
Value Added Packaging (VAP)
Right-sized packaging for aerospace, . e. lectron...
Berlin, 1st October 2011
What interests’ children on the internet?...
Glipizide Xl Manufacturer
The added draw is they can begin releasing billio...
ARIA + HTML5
Steve Faulkner & Hans Hillen & Karl Grove...
Accessibility of HTML5 & WAI-ARIA
The . Paciello. . G. roup. Accessing Higher Grou...
** 30-day minimum subscription may be required. A High Speed Internet
12716_PROG_ONT_0115 Have a second home?Get 50% off...
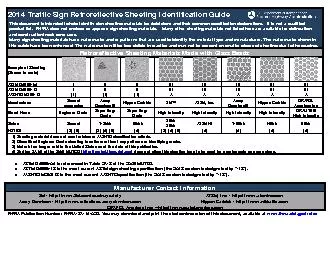
ASTM Type I II II III III III III III III
Manufacturer See note A Dennison
Blogging in business
Blogs. Began in 1990s to facilitate collaboration...
Denial of Service
Denial of Service Attacks. Unlike other forms of ...
Denial of Service
Denial of Service Attacks. Unlike other forms of ...
How topology decisions affect speed/availability/security/c
Network Topology. Metrics for judging network des...