Search Results for 'Evasion Malicious'
Evasion Malicious published presentations and documents on DocSlides.
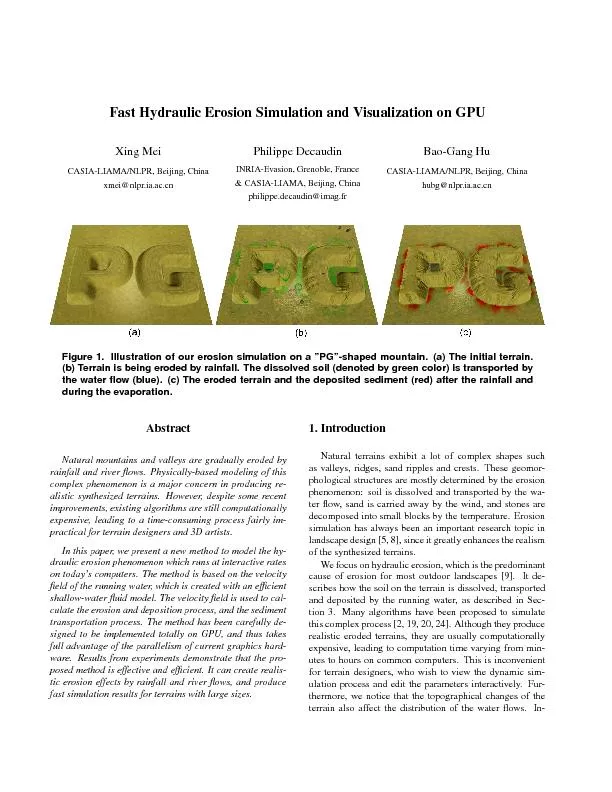
FastHydraulicErosionSimulationandVisualizationonGPUXingMeiCASIA-LIAMA/
(NOSPAM) nlpr.ia.ac.cnPhilippeDecaudinINRIA-Evasio...
SAT Vocabulary: Unit Five-Bad Reputations
Ignoble: Of low character. Licentious: lacking m...
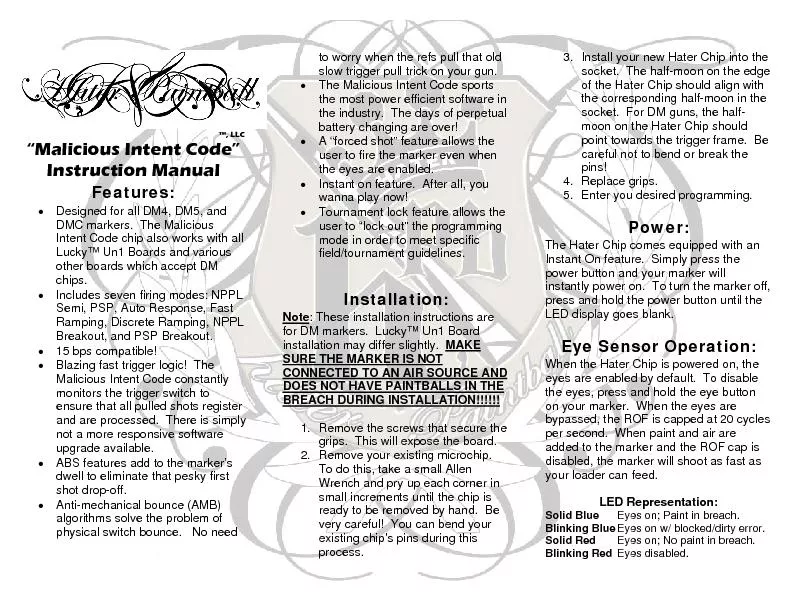
Designed for all DM4, DM5, and DMC markers. The Malicious Intent Cod
CONNECTED TO AN AIR SOURCE AND DOES NOT HAVE PAIN...
Part 4: Malware Functionality
Chapter 11: Malware Behavior. Chapter 12: Covert ...
Instructor:
Dr. . Narisa. . N. Y. . Chu. Thousand Oaks, CA, ...
Summary of the inal uleon mortgage loan originator qualification and c
To prevent evasion, the final rule prohibits compe...
Automate, or Die
Building . a Continuous Response Architecture. Co...
SWGOH – Skills
Part 1 - Dodge . with. Evasion and Foresight. S...
Malicious
Logic. What is malicious logic. Defenses. Compute...
The Rise of Ransomware
in Healthcare:. New Threats, Old Solutions. Chuck...
The Current State of
Ransomware. Ryan Archer. Sophos Sales Engineer. A...
Ransomware
t. oday: . How to protect against . Locky. and f...
I John 2:9-11
“He that . saith. he is in the light, and . ha...
UNIT 8 VOCABULARY
Theme:. Good and Bad. PREFIXES. . Bene. = ...
Malicious Code
CSH6 Chapter 16. “Malicious Code”. Robert Gue...
An Efficient Distributed Trust Model for Wireless Sensor Ne
J. Jiang, G. Han, F. . Weng. , L. Shu, M. . Guiza...
Smartening the Environment using Wireless Sensor Networks i
Presented By. Al-Sakib Khan Pathan. Department of...
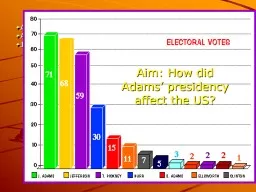
Aim: How did Adams’ presidency effect the US?
1796 Election. Adams(Federalist) vs. Jefferson (A...
Malicious Code and Application Attacks
Unit - . 2. Outline. Malicious code. Password att...
Latin Roots
“. Bene. ” and “Bon. ”. means . “Good�...
Escalation Of Ad Wars
Boosts Malware Delivery. Get free antivirus. Real...
PyCRA
: Physical Challenge-Response Authentication For ...
Trespass to Person
By. Waseem I. khan. Assistant Professor. Shri Shi...
September 2014
McAfee Next Generation Firewall. and Security Con...
1 Dual Execution Protocols
(for when semi-honest is only semi-good-enough). ...
E xplaining Bitcoins will be the easy part:
Email . Borne Attacks and How You Can Defend Agai...
Dynamic Trust Management for Delay Tolerant Networks and It
1. Abstract. 2. In this paper, the authors design...
Securing Embedded User Interfaces:
Android and Beyond. Franziska Roesner and . Taday...
Malicious Software
Computer Security . Peter Reiher. February. 21, ...
Towards Trustworthy Multi-Cloud Services Communities: A Tr
. -presented by-. Andreea. Sistrunk & . Jos...
Malicious Hubs
Sarah . Jaffer. PCs monitored by users. Varying l...
Emerging Trends in Anti-Tax Evasion Measures
Presentation to : . ACAE. CHARTERED ACCOUNTANTS...
Explaining Bitcoins will be the easy part:
Email Borne Attacks and How You Can Defend Agains...
Trust Management for SOA-Based IoT and Its Application to Service Composition
Ing-Ray Chen, Jia Gua, and Fenye Bao. Background....
Smart Agent For Users Reviews
Design Review. Big Data Workshop, Spring 2015. Yo...
The New Generation of Targeted Attacks
Eric Chien. Technical Director, Symantec Security...
White collar crimes White Collar Crimes
". White collar crime" can describe a wide variet...
Defending: Taxonomy of Botnet
Threats. Presented by GTR version M. Taxonomy of...
Adversarial Machine Learning
—An Introduction. Binghui. Wang, Computer Engi...
AppContext : Differentiating Malicious and Benign Mobile App Behavior Under Contexts
Wei Yang. , . Xusheng. Xiao, Benjamin . Andow. ,...