Search Results for 'Dawn Message'
Dawn Message published presentations and documents on DocSlides.
Name: _________________________________ The Dawn’s Awake The
1. Pitifully sad and abandoned or lonely: 2. A so...
Dawn
1 Introduction.......................................
Measuring the Effectiveness of Error Messages Designed for
Guillaume Marceau. Kathi Fisler (WPI). Shriram Kr...
Edward
Estlin. Cummings. . (1894 - 1962). All in green...
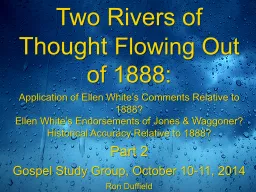
Two Rivers of Thought
Flowing Out of 1888:. Application of Ellen White�...
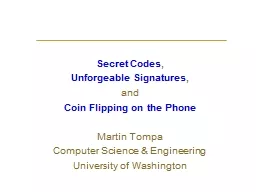
Secret Codes
,. Unforgeable Signatures. ,. and. . Coin Flippi...
A Presentation by:
~Ksenia Potapov. ~Amariah Condon. ~Janette Fong. ...
Cryptography and Network Security
Chapter 2. Fifth Edition. by William Stallings . ...
CISSP
®. Common Body of . Knowledge Review:. . Crypt...
Cis 4930
Introduction to cryptography. In 60 minutes ….....
Cryptography
Lecture 1. Arpita. . Patra. Welcome to the secon...
Cryptography
Aalto . University. , . autumn. . 2012. Outline....
Cryptography Introduction
CS 465. Last Updated. : . Aug 25, 2015. Outline. ...
Topic 7:
Using cryptography in mobile computing. . Crypto...
Cryptography and Network Security
Sixth Edition. by William Stallings . Chapter 19....
Cryptography and Network Security
CSL 759. Shweta Agrawal. Course Information. 4-5 ...
Understanding Cryptology
Core Concepts. Dr. Kerry A. McKay. 1. Approved fo...
Cryptology
Kylie Brown. Outline. Introduction. What is Crypt...
Internet Security 1 (
IntSi1. ). Prof. Dr. Andreas Steffen. Institute f...
Computer Systems
An Integrated Approach to Architecture and Operat...
Scientists detonated the first H-bomb in 1952, creating an explosive f
Just after Dawn on November 1, 1952, American scie...
Visual Programming
C#. Hozan. K. . Hamarashid. hozancsi@gmail.com. ...
Cryptography
Zac . Blohm. & Kenny Holtz. Importance of Al...
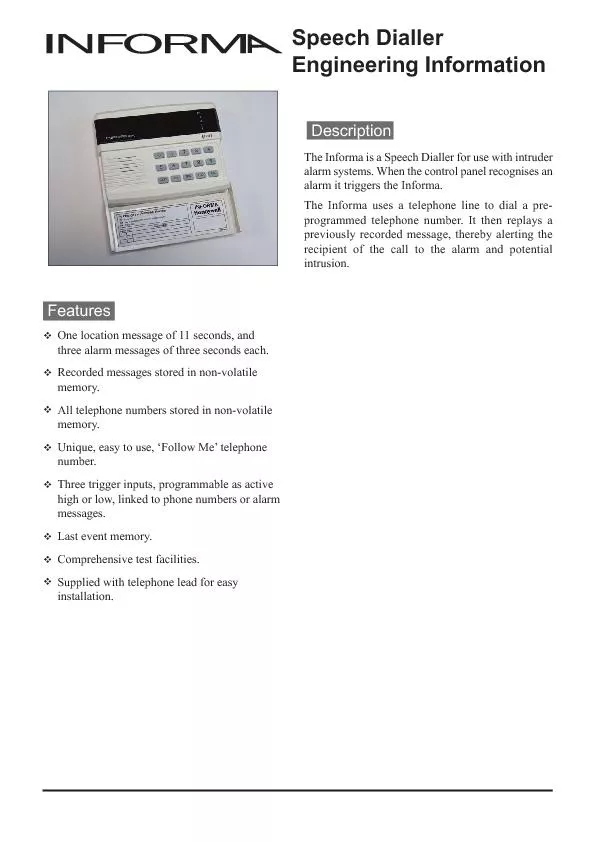
Engineering Information
location message) may be up to 11 seconds long,Typ...
CST8177 – Linux II
Services, logging, accounting. Todd Kelley. kelle...
Computer Science: A new way to think
COS116: 4/28/11 . Sanjeev . Arora. “. Computer ...
Facing The Dawn
Luke 24:13-35. He Is Risen. Going from Jerusalem ...
Martin Flügge
martin.fluegge@mftech.org. http://www.mftech.org....
Oh, say can you see, by the dawn's early light,
What so proudly we hailed at the twilight's last ...
It Is Always Darkest Before the Dawn By Krista Fink Standing on the p
I was secretly happy that someone was attemp whom ...
Message Queue Dumping
MPI Side Document. History. MPIR and MQD were des...
Text Message Campaigns for Health Advocates
SMS 101. Agenda. What are text message campaigns?...
9:1-29
A CD of this message will be available (free of c...
Educators, Technology and 21st Century Skills: Dispelling Five MythsA
@ @ Contents A Message from the President and Dean...
Cryptography
a connection between language and mathematics. In...
The Many Faces of Publish/Subscribe
Erin Collins. Topics in Computer Science. Spring ...
Chapter 1 – Introduction
Part 3. 1. Cryptographic Concepts. Encryption. : ...
Encryption / Security
Victor Norman. IS333 / CS332. Spring 2014. Proble...
Cryptography
Dec 29. This Lecture. In this last lecture for nu...
Cryptography
Dan Fleck. CS 469: Security Engineering. These sl...