Search Results for 'Claims Server'
Claims Server published presentations and documents on DocSlides.
Microsoft SQL Server Data Tools:
Database . Development from . Zero . to . Sixty ....
SIP and NAT
Dr. Jonathan Rosenberg. Cisco Fellow. What is NAT...
Made-to-stock (MTS) operations
Product is manufactured and stocked in advance of...
Reporting Services – Data Driven Subscriptions
1. General Steps. Step 1, . Create report and Ide...
Solid State Storage in Oracle Environments
Mark Henderson & Rick Stehno. CAUTION. : We s...
M ANAGING
Y. OUR. W. EBSITE. 06/06/2014. Team:. Tony Ada...
Mikrotik Dude
A powerful network monitoring system . Hey Dude !...
Duress Detection for Authentication Attacks Against
Multiple . Administrators. Emil Stefanov. UC Berk...
juliandyke.com
Understanding. GoldenGate. Julian Dyke. Independe...
Mark Asmus | Plumbline Solutions
Upgrading to Microsoft Dynamics SL 2015. Supporta...
The Buggers’ Dilemma:
Eavesdroping. and . Traceback. . on the Interne...
Accessing Public Wi-Fi:
Security Issues. Sankar. Roy. Department of Comp...
Providing Ubiquitous Networks Securely
Using Host Identity Protocol (HIP). Akihiro Takah...
Echo Cookie TCP Option
Bob Briscoe. Nov 2014. Bob Briscoe’s work is pa...
Language
Change. . Theorists. AO2 –Concepts and Theorie...
Lesson 10:
GUI HTML Editors. Lesson 10 Objectives. Identify ...
Flexible & On-demand Cloud Services
Adapt and grow easily by hosting apps in the clou...
MARITIME LIENS IN GHANA
GODWIN DJOKOTO. LECTURER, FACULTY OF LAW, UNIVERS...
Patent Law Developments and Statistics for 2013
June 2013. Table of Contents. 1. Case . Law . ......
Money and The Ruling Elite
Money, Organized Interests, and American Politics...
Email Server Migration
Briefing. Session For . IDLPs. ITSC. iMail. The ...
COMMENTS RECEIVED
ON . REVISED DRAFT GUIDELINES FOR EXAMINATION OF ...
Study on the Sufficiency of Disclosure (SCP/22/4)
Standing Committee on the Law of Patents (SCP) Tw...
THE SOUTH CHINA SEA :
SEPARATING FACT FROM FANCY. FOUNTAIN OF MISINFORM...
Andrea French
Technical . Specialist, Insurance Sector Team. 3....
Computer Science 490.002
Topical Paper Presentation #07. John Jenkins. The...
Verificationism
and religious language. Michael Lacewing. enquir...
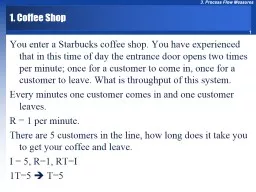
1. Coffee Shop
You enter a Starbucks coffee shop. You have exper...
EMu enhancements and
developments. Darrell J. Siebert. NHM Collections...
PrimoGENI
Tutorial. Jason Liu, Miguel . Erazo. , Nathanael...
DELIVERING TO
MULTIPLE SOLUTIONS. INP COMPUTER TECHNOLOGY PVT. ...
Lonny Bastien Kevin Cunnane
Senior Program Manager Senior Software Engineer. ...
Offline-Enabled Data Services And Desktop Applications
Pablo Castro. Software Architect. Microsoft...
Windows Azure Enables Next Generation Conferencing Solution
Michael Conrad. . Product Unit Manager. Mic...
5: DataLink Layer
5-. 1. Chapter 5. Link Layer and LANs. A note on ...
Mapping:
Data Transport. Jered McClure. Walden University....
Monomi
: Practical Analytical Query Processing over Encr...
CryptDB
:. Protecting Confidentiality with Encrypted Que...
Building web applications on top of encrypted data using My
Presented by. Tenglu Liang. Tai Liu. Motivation ....
CryptDB
: Protecting Confidentiality with Encrypted Query...