Search Results for 'Authentication Fido'
Authentication Fido published presentations and documents on DocSlides.
Motivation4!Prone to lifting !User authentication
9 10!First Touch Position!!First Touch Area!First ...
What’s New in Active Directory Domain and Federation Serv
Samuel Devasahayam. @MrADFS. BRK3871. Self-servic...
Section 2.3 – Authentication Technologies
1. Authentication. The determination of . identit...
ECE454
/599. . Computer and Network Security. Dr. . Ji...
Remotely authenticating against the Service Framework
Cathal Connolly. Senior Engineer DNN Corporation....
Francois Doremieux (Microsoft Corporation)
Rui Maximo (Lync-Solutions). Unlocking Lync Mobil...
WLAN Security
Issues, technologies, and alternative solutions. ...
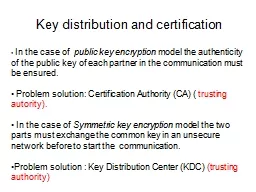
Key distribution and certification
. In the case of . public key encryption . mode...
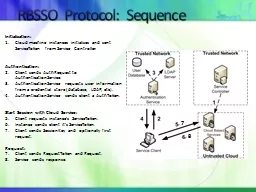
RBSSO Protocol:
Sequence. Initialization:. Cloud machine instance...
Candidate Authentication The completed form should be retained within
The work you submit for assessment must be your ow...
Paul Robichaux
Dell. paul_robichaux@dell.com. SERV301-R. Better ...
IPSec
1. Outline. Internet Protocol. IPv6. IPSec. Secur...
Public key (asymmetric) cryptography
Modular exponentiation for encryption/decryption....
Exposing the Secrets of Windows Credential Provider
Presented By:. Subrat Sarkar. Give . me your pass...
Federated Identity
Management and Access . Andres Carvallo. Dwight M...
Authentication
IT443 – Network Security Administration. Instru...
Figure 1 GPRS Architecture and Interfaces The HLR is a database that c
IV. GPRS AUTHENTICATION When MS initiates a connec...
UsingSecureCoprocessorsBennetYeeMay1994CMU-CS-94-149SchoolofComputerSc
Keywords:authentication,coprocessor,cryptography,i...
Authentication Protocols
Rocky K. C. . Chang, 18 March 2011. 1. Rocky, K. ...
Research Experiment Design Sprint:
Keystroke Biometric Intrusion Detection. Ned Bake...
Physical Security
Chapter 8. Objectives. Describe how physical secu...
Lexical Neutrality
. Composite . Meanings. Paul M. Pietroski. Dept....
Group-based Source Authentication in VANETs
You Lu, Biao Zhou, Fei Jia, Mario Gerla. UCLA. {y...
The Future of Authentication and Security
Kevin Dohrmann. CTO . Cosentry. MOVING FORWARD WI...
Unique
Identification Authority of India. Aadhaar Authen...
Resolution
http://users.encs.concordia.ca/~c474_4/Resolution...
Pass the Hash Whitepaper v2
CDP-B241. Patrick Jungles, . TwC. Mark Simos, . M...
Cloud federation
A. re we there. yet?. . Marek Denis. CERN . ope...
Securely Deploying Windows Mobile in Your Enterprise
Vik. . Thairani. Mobility Technical Sales Consul...
Securing Big Data
Kaizen Approach, Inc.. Big Data Defined. Big data...
1 Authentication beyond Passwords
Prof. . Ravi Sandhu. Executive Director . and End...
Grouper UI Part 1
Shilen Patel. Duke University. This work licensed...
ECE 454/CS594
Computer and Network Security. Dr. . Jinyuan. (...
Technical white paperPage �� &#x/MCI; 0 ;&#x/MCI; 0 ;Name serv
Note Authentication should generally be configured...
Security for Operating Systems: Cryptography, Authenticatio
CS. . 111. Operating . Systems . Peter Reiher. ...
Security in Operating Systems
CS. . 111. Operating . System Principles . Peter...
Securing a Place in History: Authentication, Authorization,
01-04-2015. Steelsen S. Smith and Melissa A. Wisn...
ASP.NET Identity
From Membership to Identity. Goals. One ASP.NET M...
H.C. Agrawal
DDG . Application & . Authentication Divisio...
Identity management
Aalto . University. , . autumn. 2012. Outline. S...