Search Results for 'Attack Offenders'
Attack Offenders published presentations and documents on DocSlides.
BLADE
: . An . Attack-Agnostic Approach for . Preventin...
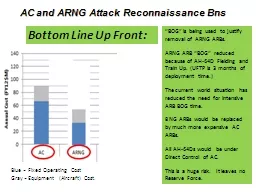
AC and ARNG Attack Reconnaissance
Bns. . “BOG” is being used to justify remova...
Recommendations for Alien Contact
U.S. Congressional Staffers Sharon Kim, Alex Bran...
Basic Game AI
IMGD 4000. With material from: Ian Millington an...
TEL 283
DoS. on Competitor Web Site. Phoenix has a “re...
A GUIDE FOR VENDORS, CONTRACTORS AND VOLUNTEERS WHO PROVIDE
Engaging in any form of overfamiliar activity wit...
When the Sky is Falling
Network-Scale Mitigation of High-Volume . Reflect...
n-gram analysis
Intrusion Detection Within Networks and ICS. Litt...
Towards efficient traffic-analysis resistant anonymity netw
Stevens Le Blond . David . Choffnes. . Wenxu...
The Need for Security
Chapter 2. Information security’s primary missi...
Advanced Persistent Threats
(APT). Sasha Browning. Breakdown . Advanced. Comb...
Synthesis of Benzene Derivatives: Electrophilic Aromatic Su
15-8. Benzene undergoes substitution reactions wi...
Understanding Vigilantism
in Khayelitsha. Examining evidence submitted to t...
Analyzing and Profiling Attacker Behavior in Multistage Int
1. Contents. Introduction and Background. Literat...
Denial of Service
Denial of Service Attacks. Unlike other forms of ...
Denial of Service
Denial of Service Attacks. Unlike other forms of ...
How topology decisions affect speed/availability/security/c
Network Topology. Metrics for judging network des...
Security Lab 2
MAN IN THE MIDDLE . ATTACK. Objectives. To unders...
SCSC 555 Computer Security
. Chapter 10 Malicious software. Part B. Index....
Dynamic Taint Analysis for Automatic Detection, Analysis, a
Paper by: James Newsome and Dawn Song. Network an...
LASTor
: A Low-Latency AS-Aware Tor Client . Masoud. . ...
Attacking Concepts
Installation of the 30 Stack Defense. COPYWRIGHT�...
170173
Team Offense: The 21 Set. The 21 Set: Level of Pl...
SSCI E-100b Graduate Research Methods and Scholarly Writin
Joe & Doug Bond. Class 7. March 24, 2014. Age...
Probation Officer V.S Bailiff
By: Jon Taroy. Backgrounds Of my Career choices. ...
List 4
Vocabulary Cartoons Practice. Ignorant, unenlight...
Attack TrendsEditors: Iv
IVAN ARCETechnologiesELIAS LEVY uring the past dec...
Basement Fires
Introduction. From a firefighting standpoint, bas...
Attack
What picture of the battlefield does . S. asoon. ...
Lucky 13, BEAST, CRIME,...
. Is TLS dead, or just resting?. Kenny Paterson....
hones Security
Smart P - Touch Screen Smudge Attack Khalid AlRowa...
Volleyball Rules & Mechanics Session
UD . Intramural Employment . Criminal Background ...
Rampage
Higgins O’Brien. Spring 2012. Methodical and Se...
D efending
against malicious hardware. Sam King. People invo...
Why was the Gallipoli Campaign a failure?
L/O – To identify the reasons why the campaign ...
Nazarudin Wijee
Mohd Sidek Salleh. Grid Computing Lab. MIMOS Berh...
Agent-based
modelling. . of burglary. Andy Evans. Nick . Mal...
Automating Bespoke Attack
Ruei-Jiun. Chapter 13. Outline. Uses of bespoke a...
Preserving Caller Anonymity in
Voice-over-IP . Networks. Mudhakar Srivatsa, Ling...
"STONE COLD CRAZY" Queen heard on Sheer Heart Attack Freddie MercuryRo
1 Intro (0:00) Fast .J = 248 B~S cs B~S/C x...