Search Results for 'Attack Cyber'
Attack Cyber published presentations and documents on DocSlides.
Section 5.2
Network Forensics. TRACKING HACKERS THROUGH CYBER...
Science Starter – Daily Challenge
Science Trivia . #10. Science Trivia. 1. . Which ...
Peeking into Your App
. without Actually Seeing It. : . UI State Infer...
1 SENSS
Security Service for the Internet. Jelena Mirkovi...
Governor’s
Office of . Homeland . Security & Emergency ...
homophobia
definition: negative thoughts, actions and feelin...
Brain Control
By: Kurt De Leon, Samony Riyaz, Caroline George. ...
Phishing – Are You Getting Hooked?
Facilitators. Janet Wilson, Project Manager C² T...
DIRECT PARTICIPATION IN HOSTILITIES
Civilians in Non-International Armed Conflicts. F...
EXPERIMENTAL STUDIES ON HYDRODYNAMIC CHARACTERISTICS OF SUP
Associate Prof. . Xulong. Yuan. College of Marin...
Asymptotic fingerprinting capacity in the
Combined Digit Model . Dion Boesten and Boris . �...
Mr. Robert Bennett
Chief, Resources & Analysis Division, J6-R. C...
Script less Attacks
Stealing the Pie Without Touching the Sill. Backg...
Cyber Security threats to
Open . Government Data . Vishal Marria. April 20...
Web Security Project
Creating an anonymous proxy server to monitor and...
Are you secured in the network ?: a quick look at the TCP/I
Based on: A look back at “Security Problems in ...
Security Requirements of NVO3
draft-hartman-nvo3-security-requirements-01. . S...
E-Safety and cyberbullying
What actually is E-Safety?. E-Safety is the safe ...
Browser Security
Presenter: Yinzhi Cao. Slides Inherited . and Mod...
Privacy Requires Security, Not Abstinence: Protecting an In
Facebook. Article by Simon . Garfinkel. Presentat...
Weapons: The Future of War
By Nicholas Ng. HON 301. Professors Eduardo . Men...
Attack of the Superbugs
Lab Introduction. Mrs. Stewart. Medical Intervent...
The Homograph Attack Evgeniy Gabrilovich Alex Gontmakher gabr@acm.org
gsasha@cs.technion.ac.il Computing veterans rememb...
Tackling Attack Detection and
Incident Response Research and Analysis by Intel S...
The Indispensable Component of Cyber Security: The Dynamics
Cooperation. Prof. . Nazife. Baykal. Director of...
Glasgow University Library
Attack of the Spanish on the Mixt
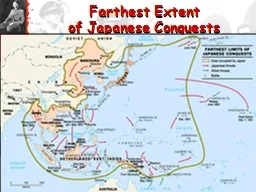
Farthest Extent
of Japanese Conquests. Early WWII Battles in the ...
Fault Tolerant Infective Countermeasure for
AES. Sikhar . Patranabis and Abhishek Chakraborty...
Inferring Internet Denial-of-Service Activity
David Moore, Colleen Shannon, Douglas J. Brown, G...
Loading…
Hero. Juan Luna. Fernando A.. HP. MP. 560/560. 34...
Business Unit
Security & Authentication - An industry persp...
Published on 16 April 2014 by authority of the House of Commons London
Bastion Attack Thirteenth Report of Session 2013...
A methodology and supporting techniques for the assessment
insider threats. Nicola . Nostro. Tutors. Bondava...
Next Generation Intelligent Cyber-Physical System for Integ
ASFPM 2012. Decision, Information and Knowledge. ...
Afghanistan Illegal Drug Trade
LT Dan Ryan. Capt Steve Felts. Capt Bethany Kauff...
Examination of the Interplay of Reliability and Security us
Modeling Language (SysML).. By. . Venkateswa...
Shadow:
Simple HPC for . Systems Security Research. Invit...
Terrorism
7th Grade UBD - Unit 3 - Terrorism. Reach Into Yo...
Presented by Richard Skowyra
An Overview of Knowledge Compilation for Solving ...
CSc 8222 Network Security
Intruders. WenZhan. Song. Cryptography and Netw...