Search Results for 'Attack Allies'
Attack Allies published presentations and documents on DocSlides.
Moving Target Defense in Cyber Security
Jianjun “Jeffrey” Zheng. July 2014. Moving Ta...
Privacy Enhancing Technologies
Elaine Shi. Lecture 2 Attack. slides partial...
Vampire Attacks: Draining Life from
Wireless Ad Hoc Sensor Networks. Eugene Y. . Vass...
Denial of Service Attack and Prevention on SIP VoIP
Ge. Zhang, Sven . Ehlert. , and Thomas . Magedan...
Mitigating
. DDoS. Attacks. ------ An Overview. Zhang Fu. ...
Collision resistance
Generic . b. irthday attack. Online Cryptography ...
and at the same time the hero is presented with new allies and hostile
ordinary world) in which resolving the problems of...
FATAL ATTACK:SIZE OF DOG POPULATION:780,00017.00217%PIT BULLSFATAL ATT
A LABRADOR MIX attacked a 70-year-old man, sending...
Man vs.
Machine: Adversarial Detection . of Malicious . C...
Man in The Middle
Christopher Avilla. What is a . MiTM. attack?. M...
Practical Aspects
of . Modern Cryptography. Josh Benaloh. Br...
By C.Sneha
. (ME12B1011). What is ECG?. Why is ECG used?. -...
Threats, Vulnerabilities, and Risks
CS . 795/895. References. . Reference 1. Big Lis...
Monday
Tuesday. Wednesday. Thursday. Friday. 10:00am-10:...
FM 99.9,
Radio Virus: Exploiting FM Radio Broadcasts for M...
Why did castles change?
L/O - To . understand . and explain how and why ....
A 501(c)3 nonprofit organization. We are dedicated to the c
Our organization only holds. adoption fairs in o...
Defending Against Modern Cyber Advisories
Rajitha. . Udayanga. , CISSP | rajitha.udayanga...
Lecture
11. Malicious Software. modified from slides of ....
Lecture 1:
Overview. modified from slides of . Lawrie. Brow...
Click to begin the simulator. You will be facing decision t
Counter . S. trike. G. lobal Offence. Before You ...
COS 433: Cryptography
Princeton University . Spring 2010. Boaz Barak. L...
Password cracking
Password cracking. From the cryptanalysis . and c...
The Berlin Airlift
&. Iron Curtain. By. Blake Wilson. The Iron C...
Weapons(Page 186)eapon Attack Pool Rang
107-95-6 3-4 1 2 Character BodyAthletics + =Endu...
Today’s plan
Video Introduction: Saving Private Ryan. Presenta...
Lecture 15
Denial of Service Attacks. modified from slides o...
Building Floodgates: Cutting-Edge Denial of Service Mitigat
Yuri Gushin & Alex Behar. Introductio. n. DoS...
Malware
Computer Forensics. Attack Phases. Computer Foren...
IntroductionAMY DILLWYNyears after the actual attack on the Pontardula
Intros. 5/5/06 9:33 AM Page v Swansea to work o...
Statistical properties of
Tardos. codes. Boris . Š. kori. ć and Antonino...
maps. In order above, they are the Allies: Belgium,France, United Stat
not limit game play.During the game, the AlliesFin...
DEVELOPING WINNING
TEAMS. IT. Strategic . issues. Data quality. Deal...
Emergency Department Stroke and Transient Ischaemic Attack Care Bundle
Information and implementation package ATIL HH ML...
Assessment Tools in Stroke and Transient Ischaemic Attack (TIA) Dr Dwa
1 dwai_sen@yahoo.com Stroke and Transient ischemi...
Vehicular Ad-Hoc Networks
overview. Motivation. Ongoing research on VANETs....
Select Team Defense: Near Man
Near Man: Level of Play. “Near man” is a base...
Cyber Aggressors
A Concept of Operations. Quick Introduction. Raph...
BLADE
: . An . Attack-Agnostic Approach for . Preventin...
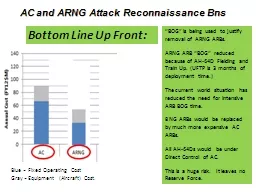
AC and ARNG Attack Reconnaissance
Bns. . “BOG” is being used to justify remova...