Search Results for 'Access Cisco'
Access Cisco published presentations and documents on DocSlides.
The FedLoan Servicing Experience
An Overview of Borrower and School Services. Agen...
2004 cisco systems inc all rights reserved dmvpn hub and
DYNAMIC MULTIPOINT VPN HUB AND SPOKE INTRODUCTION ...
Hitachi data ingestor
Bottomless, backup-free . cloud on-ramp delivers ...
The World Data
System . at . the. University . of Colorado Boul...
WI-FI ACCESS FOR ALL IN STADIUMS
The stadium of the future will need to deliver a c...
Peter Alspaugh and Richard DeLong with Bentley Systems Inc.
AutoPLANT Piping - Tips and Tricks. Projects Tool...
EE360: Lecture 18 Outline
Course Summary. Announcements. Poster session W 3...
Cisco ASA 5500 Series Configuration Guide using the CLIOL-18970-03 ...
CHAPTER 33-1 This chapter describes how to configu...
The Multi-Principal OS Construction of the Gazelle Web Brow
Presented by . Vaibhav. . Rastogi. A new protect...
Introducing Tibetan Buddhism
Chapter . 10: . Tibetan Buddhism, . women . and ....
Get Started
with Splunk. Reports & Dashboards. Workshop S...
Medida Holidays
1 Access ibility Statement for Ullswater Steamers...
Digital India
A programme to transform India into a digitally e...
Bushy Park Industrial
Complex. 1588 Bushy Park Road Goo...
CS 4700 / CS 5700
Network Fundamentals. Lecture . 6. : Data Link. (...
High Performance Cache
Replacement Using Re-Reference . Interval . Predi...
Cacti
Network Monitoring . http://cactiez.cactiusers.or...
Guidance on how to access
the O ral C holera V accine (OCV) from the ICG ...
Hazards covered by
P1 App 4, . PLUS . Env. : Freshwater, . Rural a...
Serials
DeDup. Project. Training Exercise. Antoinette Ne...
ACCESS HOUSINGFor more information, call 1-800-888-4784 (4STI) or visi
KEY FEATUESGeneral InformationProtects against bot...
Cool Tools
How to Use the Midwest Genealogy . Center. . Loc...
Carton Recycling is Happening!
How to Make Carton Recycling Part of Your Program...
A POSTCODE LOTTERY?
ACCESS TO Self monitoring of blood glucose by peop...
Struts will automatically create and populate a
Summar formbeanrepresentingincomingrequestdata for...
Stubbed Aerial Terminal
SLiC ™ Easy Access and Reliable Protection Th...
Segment based inter-networking to accommodate diversity at
DCSLAB Cho wan-. hee. Introduction. Motivation. M...
Not getting caught in the web: Credible sources on the web
Megan Lowe, Reference Librarian. Session Overview...
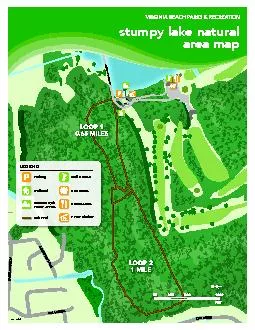
Water Access
Parking Trailhead Canoe/Kayak Soft Trail LEGEND Go...
Desigo CC
TM . . Your milestone in building management. D...
Internet Censorship
What is Internet Censorship. Control or suppressi...
Introduction to
Chalk & Wire. Kiel McQueen. k. ielmcqu@umich....
Local variables can be stack-dynamic - Advantages
Pass an access path
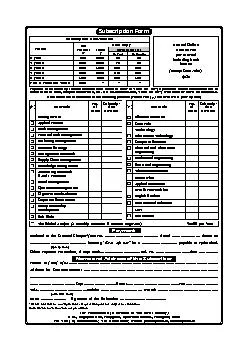
Subscription Form
Annual Online Access Feeper Journalincluding back ...
An NYTimes.com Group Subscription provides unlimited access to NYTimes
NYTIMES.COM GROUP Before ordering, please read th...
The Medium Access Control
Sublayer. Chapter 4. The Medium Access Control . ...
Virtual chassis enhancements
in . Junos. 12.2. Build high-performance network...