Search Results for '2019 Attacks'
2019 Attacks published presentations and documents on DocSlides.
Script less Attacks
Stealing the Pie Without Touching the Sill. Backg...
Web Security Project
Creating an anonymous proxy server to monitor and...
Are you secured in the network ?: a quick look at the TCP/I
Based on: A look back at “Security Problems in ...
Security Requirements of NVO3
draft-hartman-nvo3-security-requirements-01. . S...
Shanti
. Bramhacharya. and Nick McCarty. Attacks and i...
Website Fingerprinting Attacks and Defenses
Touching from a . Distance. In a nutshell …. W...
Privacy Requires Security, Not Abstinence: Protecting an In
Facebook. Article by Simon . Garfinkel. Presentat...
עופרת יצוקה
Operation Cast . Lead. זרעים של שלום. ...
What are the potential implications of an increasingly ‘w
WATER CONFLICTS. To understand where the potentia...
Fault Tolerant Infective Countermeasure for
AES. Sikhar . Patranabis and Abhishek Chakraborty...
I nferring Denial of Service Attacks
David Moore, Geoffrey Volker and Stefan Savage. P...
Inferring Internet Denial-of-Service Activity
David Moore, Colleen Shannon, Douglas J. Brown, G...
Command Injection Attacks
CSE 591 – Security and Vulnerability Analysis. ...
Insider Threat
Smart Card . Causes of Insider Threat. Personal M...
Afghanistan Illegal Drug Trade
LT Dan Ryan. Capt Steve Felts. Capt Bethany Kauff...
Examination of the Interplay of Reliability and Security us
Modeling Language (SysML).. By. . Venkateswa...
The need to protect young people
Peter . Anderson MD, MPH, PhD, FRCP. Professor, A...
Intrusion Detection
MIS.5213.011 . ALTER. 0A234. Lecture 3. Objectiv...
Building Survivable Systems based on Intrusion Detection an
Paper by: T. Bowen. Presented by: Tiyseer Al Homa...
Ambivalence in Suicide
Lisa Firestone, Ph.D.. The Glendon Association. A...
The Arab-Israeli Conflict
2000-Present. People/Things to Know. Hamas: A rad...
The Feasibility of Launching and Detecting Jamming Attacks
Authors: . Wenyuan. XU, Wade Trappe, . Yanyong. ...
Combining Cryptographic Primitives to Prevent Jamming Attac
Abstract. The Open Nature of wireless medium leav...
Joining
the Cybersecurity Revolution. : What i...
Indirect File Leaks
in Mobile Applications. Daoyuan Wu . and Rocky K....
Concurrency Attacks
Inaddition,wehopethatitwillraiseawarenessofconcurr...
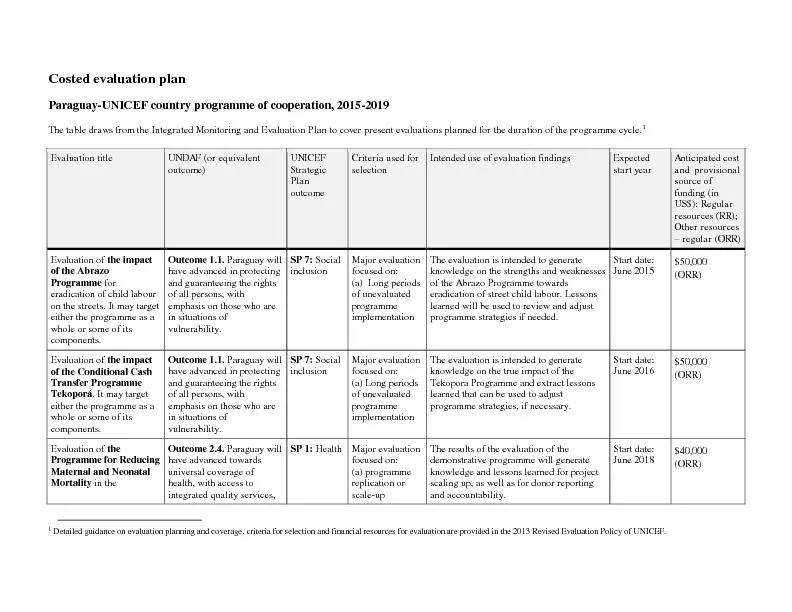
osted evaluation plan
C Paraguay - UNICEF country programme of cooperat...
Peer Attacks and Counter Attacks
A Survey of P eer - to - Yu Yang and Lan Yang Com...
Dynamic Pharming Attacks and Locked Same-Origin Policies Fo
Chris . Karlof. , J.D. . Tygar. , David Wagner, ....
YOUR WEAPONS FOR SPIRITUAL
WARFARE. Bro. Godwin Nene. Your Weapons For Spiri...
Attacks and secure configuration
Authenticationtokens-generateOne-TimePasswords,som...
Countering Web Defacing Attacks with System Self Cleansing
read-only storage device or any nonvolatile storag...
Defeating script injection attacks with browser enforced embedded policies
1Wemusttakecaretopreventcleverlyformattedcontentfr...
M ALICIOUS
. S. OFTWARE. (. 악성 소프트웨어. ). ABHI...
International league of Dermatological societies
WCD 2015 WCD bidding 2019 2-3 ILDS2013Certi�...
Using Correct
Quoting, Paraphrasing, and Summarizing. Avoid Pla...
338684
Terrorism. Political in aims and motives. Threate...
Introduction
to. Security. . Computer Networks . Term . A1...
Management Information Systems
Chapter Eight. Securing Information Systems. Md. ...
Drtzon�y: Cyuxrxsp|ontzx AtttvksAzt|nst Enxrzy Suppl|xrsSym
Dragonfly: Cyberespionage Attacks Against Energy S...