Search Results for '1 User'
1 User published presentations and documents on DocSlides.
Innovation is at hand.Continual improvement throughinnovation. The ful
The user-friendly design of 3Mstaples which allow ...
User’s Guide
Localization system StarGazer TM for Intelligent ...
SWIFT & TARGET2
Event Name. Name. Date. Presentation title – d...
Web Browsers
And Mobile Web Browsers. Guiding Questions. What ...
CC3100SimpleLink
GettingStartedGuide User'sGuide LiteratureNumber:S...
Security
and . Privacy-preserving . Applicatio...
Simple Buffer
Overflow Example. Dan Fleck. CS469 Security Engin...
Software Security
Chapter. 15 : . Attacking. . Compiled. Applica...
July 2013 Microsoft Security Bulletins
Jonathan Ness. Security Development Manager. Dust...
October 2013 Microsoft Security Bulletins
Jonathan Ness. Security Development Manager . Dus...
e.g .
Click & Collect penetration variation. Some c...
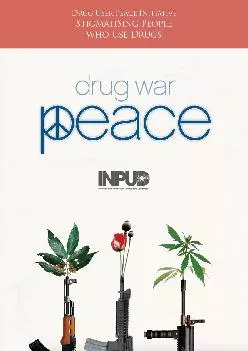
Drug User Peace InitiativeStigmatising People who Use DrugsIntroductio
1 ‘Drug use’ should be taken to refer t...
Smart Cane – P14043
Systems Design Review. Lauren Bell, Jessica Davil...
Smart Cane – P14043
Sub-Systems . Design Review. Lauren Bell, Jessica...
Smart Cane – P14043
Lauren Bell, Jessica Davila, Jake Luckman, Willia...
After the Canvass
ePledge. A . tutorial. for canvassers: . Assisti...
By Toby Reed
. E-Mail. What is E-Mail?. Email stands for ‘e...
Ryan hickling. What is an email. An email message...
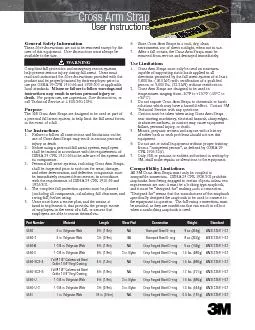
Cross Arm Strap
User Instructions Part NumberMaterialLengthWear Pa...
Information Security
4. Identify the . five . factors that contribute ...
7 Information Security
Introduction to Information Security. Unintention...
Shape of Caring Event
22. nd. July 2014. Kathy Branson. Director – S...
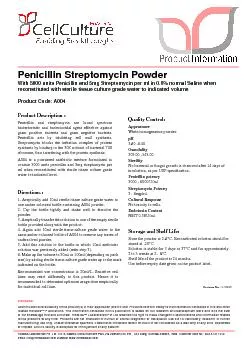
User must ensure suitability of the product(s) in their application pr
Penicillin and streptomycin are broad spectrumbact...
L-Glutamine-Penicillin-StreptomycinSolutionWith 200mM L-Glutamine, 100
Disclaimer :User must ensure suitability of the pr...
Need a lift? Want to carpool?
Characteristics of different target groups of rid...
User Manual Model:Y8POLAR STRIDE SENSOR
ENGLISHCongratulations!PolarStrideSensorBluetooth
Uni -Caster
is an Information Broadcasting Application . for ...
Catch A Ride
Ashwini, Keith, and Jarret. Overall problem and s...
Parex USA Stucco Detailsthe assembly. The designer and the user shall
PAG Non Insulated General Details PAG Insulated (H...
Linear
Submodular. Bandits . and their Application to D...
Using Styled Layer Descriptor (SLD) for the dynamic generation of user
http://www.geoinform.fh-mainz.de/~zipf/ Abstra...
Chipping Away at Censorship with User-Generated Content
Sam Burnett, Nick . Feamster. and . Santosh. . ...
CHAMELEON
Troy Ferrell. Liancheng. . Shen. ECE 256 – 2/2...
Carbon Chat Virtual Sales Agent
Engage Exit Traffic. You spend a lot of time and ...
US ARMY FINANCIAL
MANAGEMENT COMMAND. GFEBS Access and Familiarizat...
Visibility & Control
– . Identity, Application . & Content Awar...
CS Division, EECS Department University of California at Berkeley Berk
the basis of any user interface prototyping tool t...
SoftCorporation LLC.
Suggester User Manual Version 1. 1 SoftCorporation...
Framework for suggesting POPULAR ITEMS to users by Analyzing Randomize
Fig. 1: User interface to enter TagsIn this paper,...
SUITOR: An Attentive Information SystemPaul P. Maglio Rob Barrett Ch
interrupt the user with a noisy alert, or replace ...