Search Results for 'Vulnerability Security'
Vulnerability Security published presentations and documents on DocSlides.
1 ````````````````````````````````````````
AEGIS . A Fast Authenticated Encryption Algorithm...
Distributed Web Security for
Science Gateways. Jim Basney. jbasney@illinois.ed...
Securing User Access with Multi-Factor Authentication
Sarah . Fender, Director of Product Marketing . S...
Troubleshooting
Active Directory Federation Services (AD FS) and ...
Chapter 4
Authentication policy. Cyber Security for Educati...
Security of Authentication Protocols
Alexander . Potapov. Authentication definition. P...
Provide a second layer of security to access site in
Joomla. Two Factor Authentication (TFA) is a 100%...
Web Security
CS598MCC Spring 2013. Yiwei. Yang. Definition. ...
Identification, Authentication and Authorisation Issues in
Ms.. Hemali Shah. PhD Researcher. Department of ...
VPN SENTRY-
Gw. Sentry-Gw. : A . P. roject and an . Achieveme...
Your First Name and Initial Last NameYour Social Security NumberIf a J
Minnesota wages and tax withheld from W-2s, other...
www.DLR.de/fl
•. Chart . 1. > . Aviation Vulnerability ....
IC470: Flight Scheduler Assistant
Topical . Areas: . Artificial Intelligence, Datab...
Security Through Obscurity
Clark . Thomborson. Version of. 7 December 2011. ...
Data Protection in Microsoft Azure
DCIM-B387. Ramesh Chinta Principal GPM...
International Journal of Network Security & Its Applications (IJNSA),
International Journal of Network Security & Its Ap...
Guide to Network Defense and Countermeasures
. Third . Edition. . Chapter . 12. Internet and...
OFFICE OF INPECTOR GENERALDepartment of Homeland Security Washin
For more information visit our website, www.oig.d...
PsycCRITIQUES
When Resilience Fails, Vulnerability Wreaks Havoc ...
1 Welcome to the Guests of ALLAH
In the name of . Allah. ,. the beneficent and the...
NATIONAL CHALLENGES AND LOCAL NARRATIVES: THE USES OF CULT
by . JAMES C. CARLSON. BLUF. It is through a shar...
Funnypots
and Skiddy Baiting: Screwing with those that scr...
United Nations
S /RES/2201 (2015 ) Security Council Distr.: Gener...
http://www.population
- security.org/rave - 91 - 03.htm | Page 1 of 2...
BUILDING PARTNERSHIPS FOR ENERGY SECURITY
www.inogate.org. Lecture . in Energy Auditing:. L...
HOSTED EMAIL SECURITY |DATASHEETPage 1 of 2
Trend MicroHosted Email Security . Email is the mo...
Stephen D. Krasner
University of Cardiff. September 2, 2014. NATO an...
Community Food Security Coalition
3 for Community Food Systems:VALUES-BASEDPLANNING ...
Web Application Security
Grant Murphy, CISSP VP Enterprise Solutions. Cen...
Barracuda Networks
Steve Scheidegger. Commercial Account Manager. 73...
SOCIAL SECURITY NUMBERDATE
LOCATIONDAYSWORKEDOUTSIDEDELAWARETotalNumberofDays...
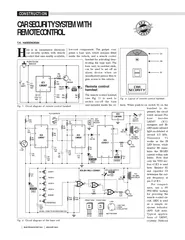
ELECTRONICS FOR YOUJANUARY 2003
CONSTRUCTIONCAR SECURITY SYSTEM WITHREMOTE CONTROL...
decades ago has taken hold of people’s imagination and stands a
an icon of strength, security, endurance, and fash...
1 Computer Security in the Real World Butler W. Lampson
blampson@microsoft.com, research.microsoft.com/la...
Concepts and Terminology for Computer Security Donald L. Brinkley and
com-puter security
Firewalls
. Dr.P.V.Lakshmi. ...
Lecture
15. Firewalls. modified from slides of . Lawrie. ...
Network Security Essentials
Fifth Edition. by William Stallings. Chapter 12. ...
CSc 8222 Network Security
Firewalls. WenZhan. Song. Cryptography and Netw...
Researching violence
and Human Security. Categories-severity-spaces. ...