Search Results for 'Security Threats'
Security Threats published presentations and documents on DocSlides.
Welcome
Cyber Security for Small . and Medium Business, N...
Presentation at the Security and Standards Track
ConnectivityWeek. Conference, June 11, 2009. Guy...
Steve Frederick
December 2012. Summit 2012 Trending Topics . and ...
Brian Carter
May 2012. WebFOCUS . 8. 1. Core Mission & Phi...
The Iraq War, the United Nations Security Council, and the Legitimacy
YAMASHITA, Hikaru Introduction The Iraq War, whi...
UNJUSTIFIED THREATS IN INTELLECTUAL PROPERTY LITIGATIONBefore issuing
Professional advisers can be added as defendants t...
Clery Act Compliance
Training. Lisa Carickhoff. Clery Compliance Offic...
A Presentation
on. “Recognition of Alphanumeric Character and...
Alternatives to PKI-based SSL
on the web. Dr. István Zsolt Berta. www.berta.hu...
Attachment:
Close observation . Clinical applications. John R...
Chapter 3
. Middle Earth and . Three Great Debates . in In...
Android Security
CEG436: Mobile Computing. Prabhaker. . Mateti. S...
Android
The most exploitable . smartphone. on the market...
Presenter:
Suzanna Schmeelk. Course: . E6998 . Date: . Dece...
Android Security Enforcement
and Refinement. Android Applications --- Example....
Aurasium
: Practical Policy Enforcement for Android Applic...
U.N. Security Council
A FTER THE endorsed a six-point diplomatic plan ...
Ensuring the Safety of all those that put their trust in th
.. Transit . Protective Services. Our . Mission S...
Baby Biometrics
By: Danielle, Laine, Taylor, & Celeste . Miss...
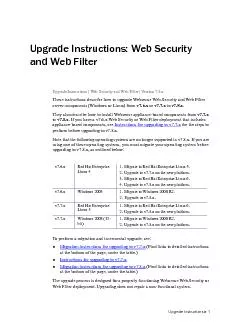
Upgrade Instructions Upgrade Instructions: Web Security and Web Filter
for the steps to perform before upgrading to v7.8...
Security Descriptions Extension for Media Streams
. (draft-zhou-mmusic-sdes-keymod-00). ...
To: UN Ambassadors of State Parties to the Rome Statute of the ICC, Me
Security Council (UNSC) unanimously passed Resolut...
Useful Computer Security
16 www.computer.org/internet/IEEE INTERNET COMPUTI...
Energy Security Initiativeat BROOKINGS
October 2014 Policy Brief 14-05 Business As Usual ...
Germany: Status Quo
Dr. Georg Heidenreich. IHE Deutschland e.V.. Over...
African Security Review 16.2
Poverty, pipeline vandalisation/explosion and huma...
Step up monitoring or install a security camera in areas where there i
• Organize a “School Watch” to enco...
VAST Program combines
Highlights • Each application security ex...
McAfee, now a part of Intel
McAfee, Inc.Pro�leWorld’s leading ...
Legal Writing and Written Advocacy
January . 2012. Factums . Purposes and Overview....
Computer Security
coursework 3. (part 2). Dr Alexei Vernitski. Aims...
Nuclear Security and
Non-Proliferation in Kazakhstan. The U.S. Foreign...
Java Unit 5: Applets and Graphics
Putting Applets into Web Pages. Two things are in...
1 Overview and General Application
Code of Ethics for Professional Accountants. Gopa...
Social Security
Number Trace : Verifies that the number issued w...
3.2 Appreciating Culture
Appreciating Tourism. How can tourists experience...
A CONSERVATIVE
APPROACH TO. IMMIGRATION REFORM. BY. LINDA CHAVEZ...
Computing and Approximating
Equilibria. : How…. …and What’s the Point?...
1 Title goes here
Julian Rapisardi Fernando Russ . jrapisardi@onap...
Advanced Persistent Threat Assessment Services
AT&T Security Solutions. APT Attacks on the R...