Search Results for 'Security Statistics'
Security Statistics published presentations and documents on DocSlides.
Class Name,
Instructor Name. Date, Semester. Chapter 2. The C...
Transportation Security AdministrationPage of 1
REV 4, 122012 Smart SecuritySaves Time… Parac...
The dark side of standards
Luis Jorge Romero . Gobal. Wireless Summit, Aa...
Statistics in Retail Finance
Chapter 4: Selection Bias and Reject inference 1 S...
We, the Heads of State or Government of on Security and Co-operation i
Now that a new era is dawning in Europe, we are d...
Litigation Holds:
Don’t Live in Fear of Spoliation. Jason Pufahl....
Patches for Optimal UptimeSteve Beattie, Seth Arnold, Crispin Cowan, P
Beattie, et al.security resources. Wave used the e...
A Trend Micro White Paper | March 2012
Virtual Patching: Lower Security Risks and Costs ...
Moving Target Defense in Cyber Security
Jianjun “Jeffrey” Zheng. July 2014. Moving Ta...
(DRAFT) Section 1. Patrol Organization
the objective. The security unit secures the obje...
Secure Computation with
Minimal Interaction, Revisited . Yuval . Ishai. ...
Form Approved
SOCIAL SECURITY ADMINISTRATION TOE 250 OMB No. ...
Five important considerations when choosing a rep payee
According to the Social Security Administration (S...
Chapter 11 – Security and Dependability
Lecture 1. 1. Chapter 11 Security and Dependabili...
SOCIAL SECURITY ADMINISTRATION
BALTIMORE, MD 21235 - 0001 SOCIAL SECURITY The Co...
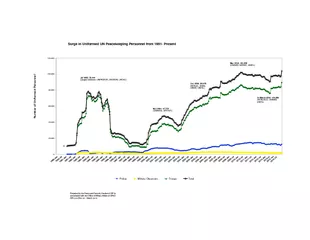
Prepared by the Peace and Security Section of DPI inconsultation with
20,00040,00060,00080,000100,000120,000Number of Un...
RBI Guidelines
Report of the Working Group on Electronic Banking...
Statistics
Estimates and Sample Sizes. Chapter . 7, Part 2. ...
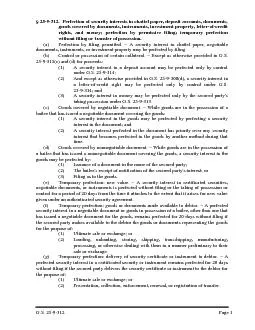
312. Perfection of security interests in chattel paper, deposit accou
G.S. 25 - 9 - 312 Page 1
Perfecting a Security Interest in an LLC Membership Interest in Virgin
Thompson McMullan, P.C. (804) 698-6223 / rbowen@t-...
U.S.-Mexico 21
st. Century Border Initiative. Roger Petzold. Fe...
New Servelec
permeating security technology inspired by the d...
Statistics and Data Analysis
Professor William Greene. Stern School of Busines...
AUTHENTICATION IN the CLOUD
Are we really safe in the cloud?. G-Force. Veron...
Cloud Computing
An In-Depth Discussion. Introductions. Nathaniel ...
Section 1-4
Data Collection & Sampling Techniques . Obje...
Introduction to Computer Security
Introduction to Computer Security. Books:. An . I...
Statistics
Probability Distributions. Assignment 5. Example ...
Making Mongo Cry:
NoSQL. for Penetration . Testers. Russell Buttur...
Shipping Dangerous Goods
Course Content. Background information. Infectiou...
Information Security
University of Notre Dame. What Does Infosec Do? ....
reliability. An elected Fellow of the Association
Computer security. Code certification and proof-...
Chapter 2
Security Market Indices. Presenter. Venue. Date....
The Rich Fool
Luke 12:13-21. Robert C. Newman. The Rich Fool. T...
Statistics on Waste Pickers in Brazilited education and skills. Moreov
Sonia M. Dias is WIEGO’s Waste Picker Sector ...
“Why Gun ‘Control’ is Not Enough” (Jeff McMahan)
What are his arguments?. How to evaluate them. MA...
Voices of the Hungry
A worldwide survey of people’s experience with ...
Global Collaboration on Automotive, ITS and Standards
ITS security – a topic for Study Group 17?. Rei...
Using block ciphers
Security for. many-time key. Online Cryptography ...