Search Results for 'Sa3 Security'
Sa3 Security published presentations and documents on DocSlides.
Ensuring the Safety of all those that put their trust in th
.. Transit . Protective Services. Our . Mission S...
Baby Biometrics
By: Danielle, Laine, Taylor, & Celeste . Miss...
Upgrade Instructions Upgrade Instructions: Web Security and Web Filter
for the steps to perform before upgrading to v7.8...
Security Descriptions Extension for Media Streams
. (draft-zhou-mmusic-sdes-keymod-00). ...
To: UN Ambassadors of State Parties to the Rome Statute of the ICC, Me
Security Council (UNSC) unanimously passed Resolut...
Useful Computer Security
16 www.computer.org/internet/IEEE INTERNET COMPUTI...
Energy Security Initiativeat BROOKINGS
October 2014 Policy Brief 14-05 Business As Usual ...
Germany: Status Quo
Dr. Georg Heidenreich. IHE Deutschland e.V.. Over...
African Security Review 16.2
Poverty, pipeline vandalisation/explosion and huma...
Step up monitoring or install a security camera in areas where there i
• Organize a “School Watch” to enco...
VAST Program combines
Highlights • Each application security ex...
McAfee, now a part of Intel
McAfee, Inc.Pro�leWorld’s leading ...
Legal Writing and Written Advocacy
January . 2012. Factums . Purposes and Overview....
Computer Security
coursework 3. (part 2). Dr Alexei Vernitski. Aims...
Nuclear Security and
Non-Proliferation in Kazakhstan. The U.S. Foreign...
Java Unit 5: Applets and Graphics
Putting Applets into Web Pages. Two things are in...
Social Security
Number Trace : Verifies that the number issued w...
A CONSERVATIVE
APPROACH TO. IMMIGRATION REFORM. BY. LINDA CHAVEZ...
Computing and Approximating
Equilibria. : How…. …and What’s the Point?...
1 Title goes here
Julian Rapisardi Fernando Russ . jrapisardi@onap...
Advanced Persistent Threat Assessment Services
AT&T Security Solutions. APT Attacks on the R...
Security for costs in investment treaty arbitration
Jakob Ragnwaldh. Mannheimer. . Swartling. , Stoc...
10/03/2015
Privacy and Security by Design Methodology II. 1....
2011 IEEE Symposium on Security and Privacy1081-6011/11 $26.00
152 148 150 156 159 154 151 153 155 160 158 161 15...
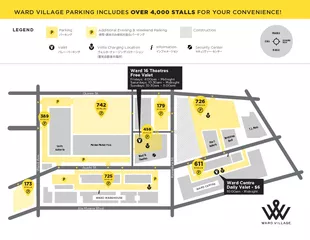
Ward Ave.Kamake‘e St.Auahi St.Ala Moana Blvd.Queen St.
LEGEND Additional Evening & Weekend Parking Inform...
EZID data security and risks
Situation. EZID is “system of record”: data i...
Deferred Action for Childhood Arrivals
Penn for Immigrant Rights . What is it?. Deferred...
New Recruits-What does it take to attract the younger gene
. Ann Thor, M.D.. The Multigenerational Workforc...
Nuclear Security Summit 2014
Chairs: Hank Chau, . Evonne. Pei, Jonathan Wu. M...
Ascension Point Capital
An Entrepreneurial Investment Firm. Table of Cont...
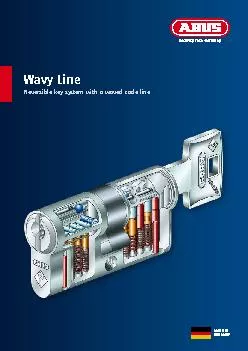
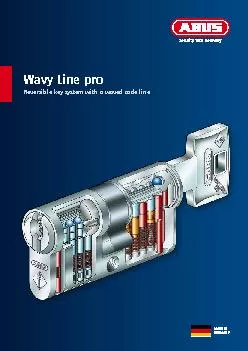
Security you can trustThe marine museum OZEANEUM in Stralsund in North
WRBFL27 Wavy LineReversible key system with a wave...
Consulting and planningStructured and thorough planning is the basis o
Security you can trustThe marine museum OZEANEUM i...
by Jim Hightower Where's the Department of Homeland Security when we r
only evasive answers, so they got to organizing, w...
Snart får vi nya rutiner för löner och förmåner.
Sverige är först ut.. Date Created: [YYYY-MM-DD...
Security Evaluation of an
Organization. TA. Md. . Morshedul. Islam. Proce...
Janna
Miletzki. , LSE, Human Geography. Refugees in a S...
Improving Application Security with Data Flow Assertions
Yip, X. Wang, N. . Zeldovich. , M. F. . Kaashoek....
Network Security Essentials
Fifth Edition. by William Stallings. Chapter 1. I...
Cryptography and Network Security
William Stallings, 6. th. Ed. . Chapter 1. Overv...
Introduction to Computer and
Network Security. Chapter #1 in the text book ( S...