Search Results for 'Recdroid Malicious'
Recdroid Malicious published presentations and documents on DocSlides.
Collaborative Attacks on Routing Protocols in
Ad hoc Networks. . Neelima. . Gupta. University...
Secure Computation
(. Lecture 3 & 4). Arpita. . Patra. Recap . ...
Test on 11/6 (A-day)
and 11/7 (B-day). Alacrity. Assiduous. Bucolic. C...
SAT Vocabulary: Unit Five-Bad Reputations
Ignoble: Of low character. Licentious: lacking m...
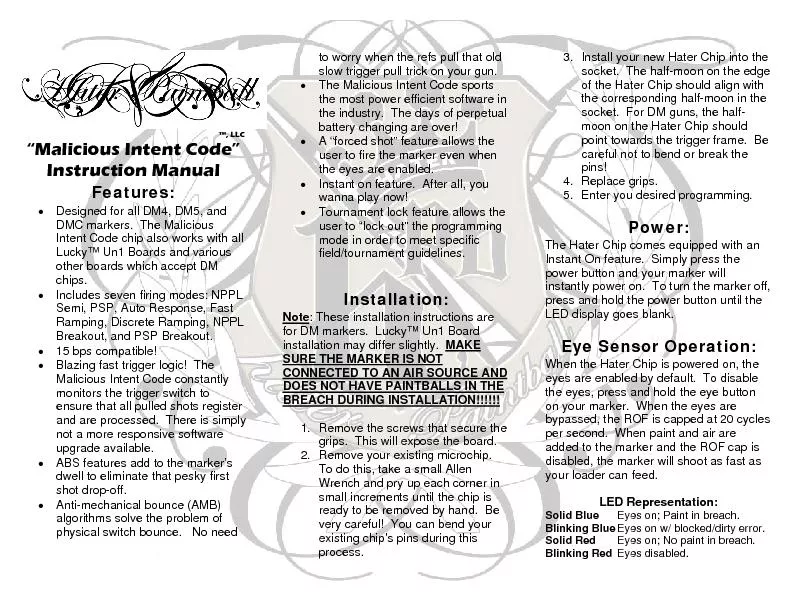
Designed for all DM4, DM5, and DMC markers. The Malicious Intent Cod
CONNECTED TO AN AIR SOURCE AND DOES NOT HAVE PAIN...
Part 4: Malware Functionality
Chapter 11: Malware Behavior. Chapter 12: Covert ...
Instructor:
Dr. . Narisa. . N. Y. . Chu. Thousand Oaks, CA, ...
Automate, or Die
Building . a Continuous Response Architecture. Co...
Malicious
Logic. What is malicious logic. Defenses. Compute...
The Rise of Ransomware
in Healthcare:. New Threats, Old Solutions. Chuck...
The Current State of
Ransomware. Ryan Archer. Sophos Sales Engineer. A...
Ransomware
t. oday: . How to protect against . Locky. and f...
I John 2:9-11
“He that . saith. he is in the light, and . ha...
An Efficient Distributed Trust Model for Wireless Sensor Ne
J. Jiang, G. Han, F. . Weng. , L. Shu, M. . Guiza...
Smartening the Environment using Wireless Sensor Networks i
Presented By. Al-Sakib Khan Pathan. Department of...
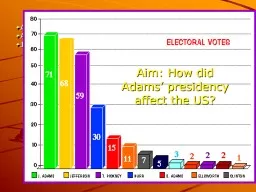
Aim: How did Adams’ presidency effect the US?
1796 Election. Adams(Federalist) vs. Jefferson (A...
Latin Roots
“. Bene. ” and “Bon. ”. means . “Good�...
Escalation Of Ad Wars
Boosts Malware Delivery. Get free antivirus. Real...
PyCRA
: Physical Challenge-Response Authentication For ...
Trespass to Person
By. Waseem I. khan. Assistant Professor. Shri Shi...
E xplaining Bitcoins will be the easy part:
Email . Borne Attacks and How You Can Defend Agai...
Dynamic Trust Management for Delay Tolerant Networks and It
1. Abstract. 2. In this paper, the authors design...
Securing Embedded User Interfaces:
Android and Beyond. Franziska Roesner and . Taday...
Malicious Software
Computer Security . Peter Reiher. February. 21, ...
Towards Trustworthy Multi-Cloud Services Communities: A Tr
. -presented by-. Andreea. Sistrunk & . Jos...
Smart Agent For Users Reviews
Design Review. Big Data Workshop, Spring 2015. Yo...
The New Generation of Targeted Attacks
Eric Chien. Technical Director, Symantec Security...
Network Security Essentials
Fifth Edition. by William Stallings. Chapter 10. ...
Stalking The willful, malicious and repeated following and harassing of another person
Robert John . Bardo. has had a long history of s...
1 Malware Detection Prof
. Ravi Sandhu. Executive Director . and Endowed C...
CSE 486/586 Distributed Systems
Byzantine Fault Tolerance. Steve Ko. Computer Sci...
Social Implications of IT
This lecture is not about nerd dating habits. Flu...
CS3235: Introduction to Computer Security
Lecture . 4: Malware. CS3235 Lecture 4. 1. Review...
HIPAA Privacy & Security
Annual Training. Training Overview. This course w...
Chapter 7 Prejudice Prejudice is a malicious, pervasive, and persistent social problem
Although its harmful effects are experienced most...
Cyber-Physical Cloud(y) Computing:
Good News, Bad News and . Looking Forward. Haibo ...
Malware Incident Response
Erdal Ozkaya . Raymond Comvalius. CISO...
Mobile Security Issues A.D. Anderson
Mobile Devices vs. Desktops. Physical Theft . –...
E xplaining Bitcoins will be the easy
part: . Email . Borne Attacks and How You Can Def...
Web Security Defense Against The Dark Arts
Cedric Cochin 1 TBD. Intel Security - McAfee La...