Search Results for 'Passwords Security'
Passwords Security published presentations and documents on DocSlides.
Passwords and Email Passwords
It is important to make a . good password. Stops...
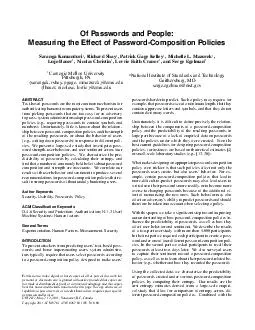
Of Passwords and People Measuring the Effect of PasswordComposition Policies Saranga Komanduri Richard Shay Patrick Gage Kelley Michelle L
Mazurek Lujo Bauer Nicolas Christin Lorrie Fait...
Passwords
Tom Ristenpart. CS 6431. The game plan. Historica...
1 Authentication with Passwords
Prof. . Ravi Sandhu. Executive Director . and End...
Human Computable Passwords
Jeremiah Blocki. Manuel Blum. Anupam Datta. Santo...
Passwords & Behavioral Ads
. Project Team. [. Insert Team Member Names]. Pr...
Passwords, Rehashed All Over Again
Avi Douglen. AppSec Israel 2014. About Me. Avi Do...
1 Authentication with Passwords
Prof. . Ravi Sandhu. Executive Director . and End...
Total Recall: Persistence of Passwords in Android
Jaeho. Lee, Ang Chen, Dan S. Wallach. Motivatio...
[READING BOOK]-What the fuck is my password: An Organizer for All Your Passwords and Shit, Floral Organizer for All Your Passwords and Shit, Abstract Tropical Design ... ALL THE FUCKING PASSWORDS I HAVE TO REMEMBER
The Desired Brand Effect Stand Out in a Saturated ...
(BOOK)-Secret Passwords Alphabetical Logbook for Internet Website Address Username & Passwords Login Organizer Log (Secure Passwords)
The perfect book to keep track of your passwords. ...
(DOWNLOAD)-Password Book - I\'m Hunting For Passwords Password Logbook for Internet Passwords | Black Password Keeper | Alphabetized | Home or Office Passwords |
Hunting Style Password Book - The Perfect Black Pa...
(DOWNLOAD)-Password Book - I\'m Hunting For Passwords Password Logbook for Internet Passwords | Black Password Keeper | Alphabetized | Home or Office Passwords |
Hunting Style Password Book - The Perfect Black Pa...
Lecture 5
User Authentication. modified from slides of . La...
Lecture 5
User Authentication. modified from slides of . La...
Authentication for
Operating Systems. What is authentication?. How d...
A Comprehensive Study of the Usability of multiple Graphica
SoumChowdhury. . (Presenter). Ron Poet. Lewis Ma...
Strong Passwords
2014-2005. Today’s Objective:. I will create a ...
Strong Passwords
2014-2005. K-2. Today’s Objective:. I will crea...
Privileged Account Management
Jason Fehrenbach, Product Manager. Customer Use C...
Team:
SuperBad. Cats. MSIT . 458 . – Dr. . Chen. Aut...
INSuRE
Project: “Name of Project”. Team member name...
Thinking in Computer
CFS 2015. This Class. cfs-web.weebly.com has all ...
Password Management
Password Protection. Virtually . all multiuser . ...
Pa$$w3rd c0mpl3X1ty
BRKSEC-1005v. Who am I and Why Should You Listen?...
Malicious Attacks
Nicole Hamilton, Dennis . Meng. , Alex . Shie. , ...
Testing Metrics for Password Creation Policies
by Attacking Large Sets of Revealed Passwords. Ma...
A Study of Passwords and Methods Used in Brute-Force SSH Attacks Jim O
usernames and passwords used in attacks. In Sectio...
Honeywords:
Making Password-Cracking Detectable. by Ari . Ju...
Module 4
Password Cracking. Presented by Heorot.net. Obje...
Cryptology
Passwords . and Authentication. Prof. David . Sin...
User Authentication
CS457. Introduction to Information Security Syste...
CS 483 – SD Section
By Dr. Daniyal Alghazzawi. (7). AUTHENTICATION . ...
Mr. Picky and Mr. Casual
HW: p843 #23 - 49. First: Basic Counting. How man...
Implications of an
Information Society. Computers in our day-to-day ...
Authentication for Operating Systems
What is authentication?. How does the problem app...
At Halliburton, solving customer challenges is second only to keeping everyone
safe and healthy. You can find more safety tips a...
Stopping Cybercrime A presentation by the
Financial Cybercrime . Task Force of Kentucky. KY...
Lecture 5 User Authentication
modified from slides of . Lawrie. Brown. RFC 282...
Stealing Credentials Breaking in Without Bugs
Many attackers steal users’ passwords. This is ...




![[READING BOOK]-What the fuck is my password: An Organizer for All Your Passwords and Shit, Floral Organizer for All Your Passwords and Shit, Abstract Tropical Design ... ALL THE FUCKING PASSWORDS I HAVE TO REMEMBER](https://thumbs.docslides.com/972275/reading-book-what-the-fuck-is-my-password-an-organizer-for-all-your-passwords-and-shit-floral-organizer-for-all-your-passwords-and-shit-abstract-tropical-design-all-the-fucking-passwords-i-have-to-remember.jpg)