Search Results for 'Packet Soc'
Packet Soc published presentations and documents on DocSlides.
Introduction The information presented in this packet is designed to p
0 How much does the performer want to be part of ...
Presented by:
Priyank Gupta. 04/02/2012. Generic Low Latency . ...
Structure of a switch
We use switches in circuit-switched and packet-sw...
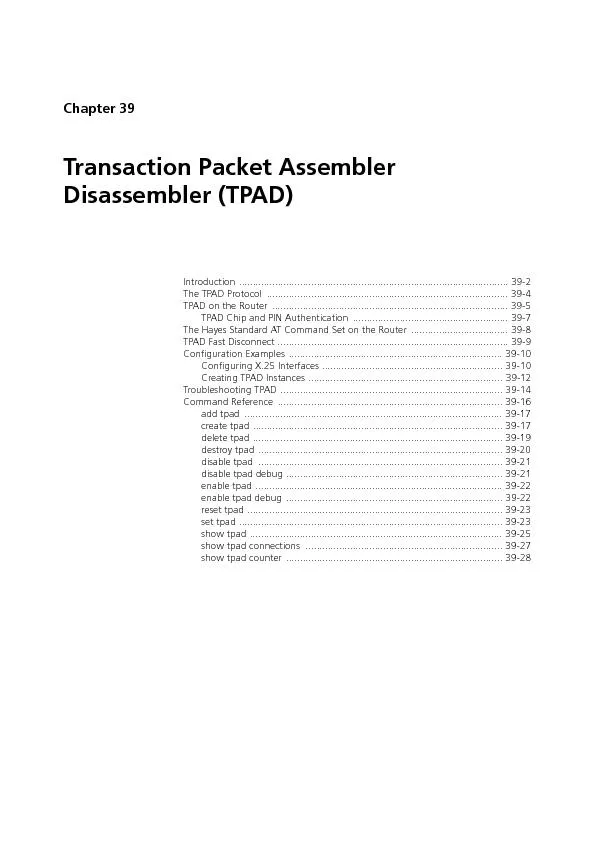
Chapter 39Transaction Packet Assembler Disassembler (TPAD)Introduction
39-2AR400 Series Router Software ReferenceSoftware...
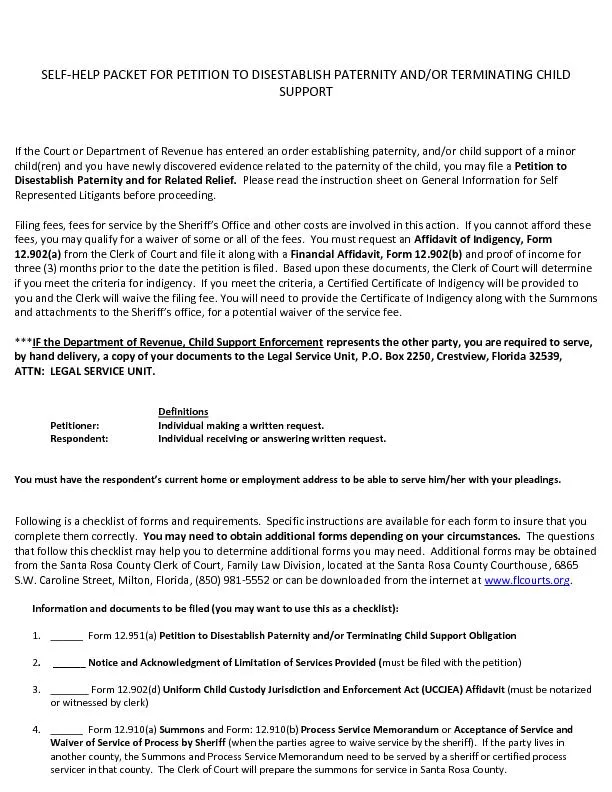
HELP PACKET FOR PETITION TO
SELF - DISESTABLISH PATERNITY AND/OR TERMINATING C...
Where is the Debugger for my Software-Defined
N. etwork?. [. ndb. ]. Nikhil Handigol, Brandon H...
Efficient Processing
of Multi-Connection. Compressed Web Traffic. Yaro...
When TTV is fixed and the number of malicious nodes increases, the def
0%5%10%15%20%30%35%40%45% Packet delivery improvem...
Decontaminate Your Skin Using the Reactive Skin Decontamina
PFC Powers, . Tifani. Decontaminate Your Skin Usi...
CEDAR
Counter-Estimation Decoupling for Approximate Rat...
Small Form Computing
A bump in the wire . . The . questions. What can...
D eep Packet Inspection(DPI)
E. ngineering for . E. nhanced . P. erformance of...
Multi-Core Packet Scattering to Disentangle Performance Bot
Yehuda. . Afek. . Tel-Aviv University. Anat. ....
Deep
Packet Inspection of Next Generation Network Devi...
C10M:
Defending the Internet at scale. by Robert David ...
Defending against Flooding-based Distributed Denial-of-Serv
Author Rocky K. C. Chang, The Hong Kong Polytechn...
Software-Defined Networking:
OpenFlow and Frenetic. Mohamed Ismail. Background...
An Overview of
Software-Defined Network. Presenter: . Xitao. We...
Network Delays, Statistical Multiplexing
EE 122 Discussion. 9/12/11. Transmission and Prop...
Probability
Review. Given. N = population. X = sample size . ...
PWE3 Congestion Considerations
draft-ietf-pwe3-congcons. (temporarily expired). ...
Hacking Techniques & Intrusion Detection
Ali . Al-. Shemery. arabnix. [at] . gmail. All m...
Performance Diagnosis and Improvement in Data Center Networ
Minlan Yu. minlanyu@usc.edu. . University of Sou...
Bellwork
(get a sheet from front table). What is the purp...
MPLS-TP
Yaakov (J) Stein. September 2011. Outline. MPLS-T...
Caught
y. a. Warm up. in the spacious and WELL-APPOINTE...
Data-Driven
Network Connectivity. Junda Liu, Scott Shenker, B...
1 If the Internet is the answer,
then what was the question?. EE122 Fall 2011. Sco...
E-Mail Capturing & E-mail Encryption
60-564 Project. Mohit. . Sud. Dr. . Aggarwal. Un...
Packet Sniffing
- By Aarti Dhone. Introduction. Packet ...
Introduction
1-. 1. CNT. . 4007C. . Computer Networks Fundam...
Quantum Mechanics
By: . Harlee...
Cro-Magnons!
By: . Ashleighh. , . Lilah. , . Ian. , . Marty. I...
Performance Evaluation of Packet
Classification on . FPGA-based TCAM Emulation . ...
Encryption
How To Secure My Data. . What . to Protect???...
Switching
Switching breaks up large collision domains into ...
On Coding for Real-Time Streaming
under Packet Erasures. Derek Leong. *#. , . Asma....
CSCI-1680
Link Layer Reliability. Based partly on lecture n...
An Intro to Network Analyzers
References:. “. Introduction to . Wiresharkl. �...
CS 4700 / CS 5700
Network Fundamentals. Lecture 20: Malware, Botnet...