Search Results for 'Jn0 230 : security Associate (jncia Sec)'
Jn0 230 : security Associate (jncia Sec) published presentations and documents on DocSlides.
Computer Programming Effective Catalog Year Revised April Page of Program Planning Guide Computer Programming Associate in Applied Science Degree credits Web Design Certificate of Proficiency
Computer programmers design b uild and support so...
Interim Decision In re HO Petitioner In Visa Petition Proceedings WAC Decided by the Associate Commissioner Examinations July
1 Merely establishing and capitalizing a new comm...
Gregg Brown Principal Adam Wallace Associate Principal Natalie Ratz Associate Principal SHAHALA MIDDLE SCHOOL Dear Students Parents and Families Entering my first year as principal at Shahala I f eel
Over the p ast two months I have had the opportun...
How to Shop for Free Online Security Analysis of CashierasaService Based Web Stores Abstract Web applications increasingly integrate thirdparty services
The integration introduces new security challenge...
IJCSNS International Journal of Computer Science and Network Security VOL
7 No12 December 2007 171 This study was carried o...
Redesigned Endo Clip III mm Clip Applier TECHNICAL BROCHURE The Endo Clip III mm underwent a redesign that yielded improvements in clip security and jaw stability
The critical ligation function has been improved ...
Computers Security A History Of Computer Viruses The Famous Trio Harold Joseph Highland FICS FACM EditorinChief Emeritus It was not until the fall of that computer virus es began to command worl
Late in 1987 computer viruses struck at two unive...
David Mazi eres Associate Professor of Computer Science Stanford University Serra Mall Room httpwww
scsstanfordedu dm Stanford CA 94305 Education Mass...
ROTARY DIRECT Rotarys recurring giving program YES I WILL ENROLL IN ROTARY DIRECT Name Rotary membership ID Club name Club number Billing address City StateProvince Postal code Country Phone
For security purposes please do not send credit c...
Preventing Cell Phone Intrusion and Theft using Biometrics Fingerprint Biometric Security utilizing Dongle and Solid State Relay Technology Donny Jacob Ohana Sam Houston State University Huntsville
edu Liza Phillips Law Enforcement College Station ...
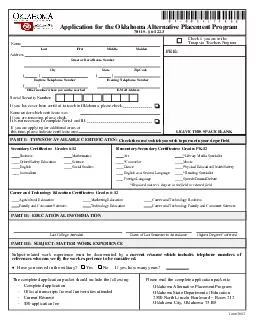
PART II EDUCATIONAL INFORMATION ame Address Social Security Number Application for the Oklahoma Alternative Placement Program O
S 61223 Last First Middle Maiden Street or Rural ...
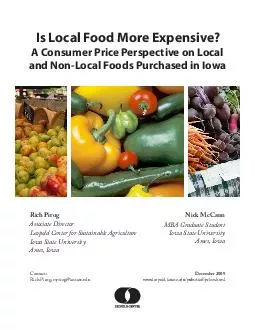
Is Local Food More Expensive A Consumer Price Perspective on Local and NonLocal Foods Purchased in Iowa Rich Pirog Associate Director Leopold Center for Sustainable Agriculture Iowa State University
leopoldiastateedupubssta priceshtml Contact Rich P...
SECURITY FREEZE INFORMATION Any consumer in Illinois may place a security fre eze on his or her credit report by requesting one in writing by certified mail to the consumer reporting agency
The consumer reporting agency is not allowed to c...
Journal of Information Assurance and Security Secure and Trusted innetwork Data Processing in Wireless Sensor Networks a Survey Alessandro Sorniotti Laurent Gomez Konrad Wrona and Lorenzo Odorico
Maurice Donat 06250 Mougins France Emailnamesurna...
WHY DEDICATED SERVERS high security you have exclusive access to your server and have the capability to restrict access to your server from outsiders control in your hands you have rootadmin access s
0DLQWDLQLQJ57347VHUYHUV57347LQ57360KRXVH57347FDQ5...
FREQUENTLY ASKED QUESTIONS Can some companies still review my credit history even with a Security Freeze in place Yes
Some private companies government agencies and co...
SYND RENT Purpose Any genuine business personal credit requirement Target group Eligibility Bonafide owners of residential or commercial property standing in their own names who have let out the same
Security Mortgage of the property being let out G...
International Journal of Electrical and Electronics Engineering IJEEE ISSN PRINT Vol Iss Design of a GSM Cell Phone based Vehicle Monitoring Theft Security System Amol S
Dhotre Abhishek S Chandurkar S S Jadhav Dept of ...
If you have questions or would like additional information on the material covered in this Alert please contact a member of the Reed Smith Advertising Compliance Team or the Reed Smith lawyer with wh
com Huw Morris Associate London 44020 3116 2816 hm...
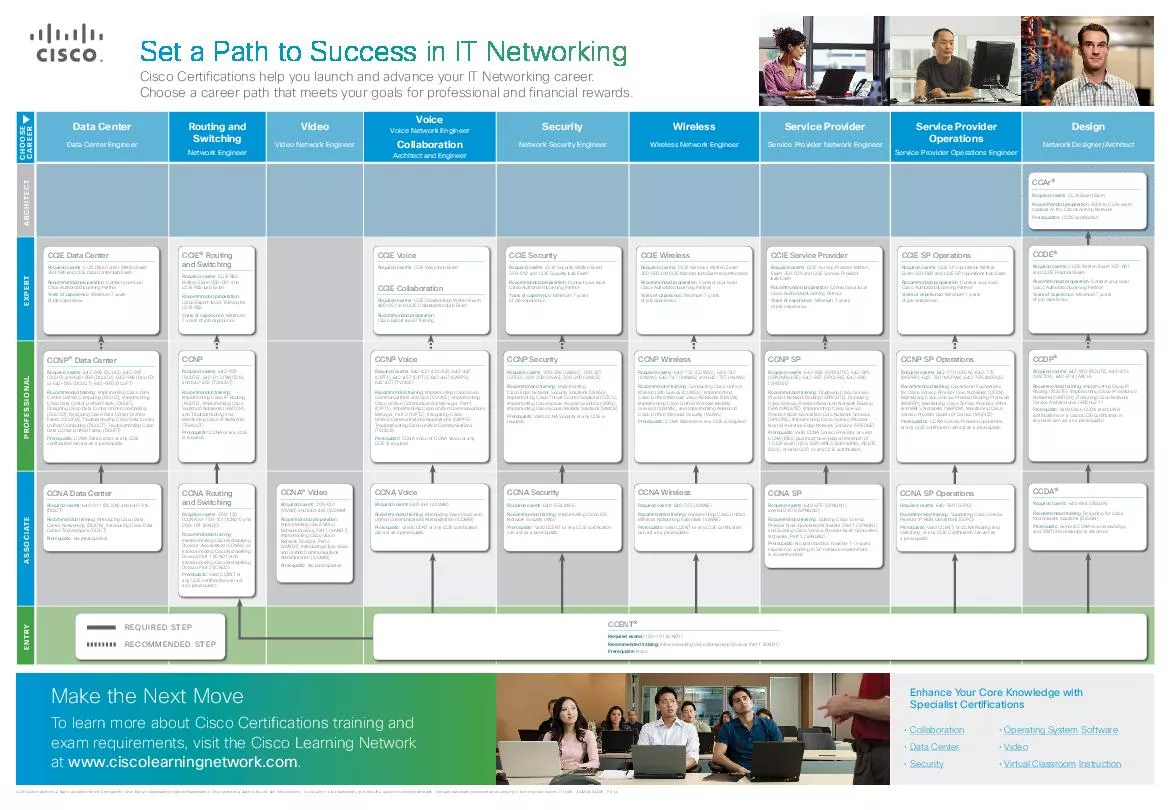
Data Center Data Center Engineer Routing and Switching Network Engineer Video Video Network Engineer Voice Voice Network Engineer Collaboration Architect and Engineer Security Network Security Engine
Choose a career path that meets your goals for pr...
We propose a simple method for improving the security of hashed passwords the maintenance of additional honey words false passwords associated with each users accou nt
An adversary who steals a 64257le of hashed passw...
Your Payments While You Are Outside The United States Contacting Social Security Visit our website Our website www
socialsecuritygov is a valuable resource for info...
Homeland Security March ach year re claims the lives of Americans and injures
Bedrooms are a common area of 57375re origin Near...
Throgs Neck Ny Security Camera Installations
IP cameras are very popular nowadays and they are ...
Exploiting Open Functionality in SMSCapable Cellular Networks William Enck Patrick Traynor Patrick McDaniel and Thomas La Porta Systems and Internet Infrastructure Security Laboratory Department of C
psuedu ABSTRACT Cellular networks are a critical c...
UHIOHFWLQJDFXVWRPHUVHSHULHQFH Product Protected Legitimate accuracy Total Accuracy Kaspersky Small Office Security Symantec Endpoint Protection Small Business Edition Sophos Anti Virus Busines
5 98 AAA Sophos Anti Virus Business 958 92 AA Tren...
Abstract Buffer overflows have been the most common form of security vulnerability for the last ten years
More over buffer overflow vulnerabilities dominat...
RECENT ADVANCES in EACTIVITIES INFORMATION SECURITY and PRIVACY ISSN
brPage 1br RECENT ADVANCES in EACTIVITIES INFORMAT...
HYLVHG GRADUATE SCHOOL Office of the Associate Dean for Graduate Student Affairs LQWRQDOO DVWDQVLQJLFKLJDQ UDGPVXHGX MSU is an affirmative action equal opportunity employer
UDGXDWH573476WXGHQW573475HVHDUFK57347QKDQFHPHQW57...
Sophos Endpoint Security and Control standalone startup guide
3 Product version June 2014 Document date brPage 2...
Kasperskys Application Control with Dynamic Whitelisting technology strengthens companies security stance by enabling IT administrators to set policies that allow block or regulate application or app
Equipped with these technologies organizations ca...
VNetLab An Approach for Realizing Logically Isolated Networks for Security Experiments Weiqing Sun Varun Katta Kumar Krishna R
Sekar Department of Computer Science Stony Brook ...
Confederation of Indian Industry ELIGIBILITY FOR CII MEMBERSHIP Categories Members Any Company or Firm in India engaged in manufacturi ng activity or providing consultancy services EngineeringTechnic
Associate Members Representative offices of forei...
P Page P Application by an INDIVIDUAL FOR A NSW SECURITY LICENCE under the Mutual Recognition Act andor TransTasman Mutual Recognition Act Please use a BLACK or BLUE PEN
Print clearly within the boxes in CAPITAL LETTERS...
The Emperors New Password Manager Security Analysis of Webbased Password Managers Zhiwei Li Warren He Devdatta Akhawe Dawn Song University of California Berkeley Abstract We conduct a security analys
Unlike local password managers webbased password ...
AppsPlayground Automatic Security Analysis of Smartphone Applications Vaibhav Rastogi Yan Chen and William Enck Northwestern University North Carolina State University vrastogiu
northwesternedu ychennorthwesternedu enckcsncsuedu...
Online data storage using implicit security Abhishek Parakh Subhash Kak Computer Science Department Oklahoma State University Stillwater OK USA article info Article history Received October Recei
We describe the use of a data partitioning scheme...
Abstract Buffer overflows have been the most common form of security vulnerability for the last ten years
More over buffer overflow vulnerabilities dominat...
Laboratory for Computer Security Education Buffer Overow Vulnerability Lab Copyright Wenliang Du Syracuse University
The development of this document is funded by the...
Guest Editor Raul Siles is the guest editor for this issue of OUCH Raul is the founder of and a senior security analyst at Taddong and also a SANS author instructor and security passionate
You can follow Raul on Twitter at taddong and on ...