Search Results for 'Intent User'
Intent User published presentations and documents on DocSlides.
Principles of
Engineering System Design. Dr T Asokan. asok@iit...
RDA Relationship Designators and Linked Data: Solutions to
Scott Cowan. MLIS Candidate . Faculty of Informat...
MTH800’s colour display provides a more user-
friendly interface and makes it easier to display ...
www.cedar-foundation.org
The Cedar Foundation. Joanne Barnes & Shauna ...
The International DSD Registry – An Update
Jillian Bryce. I-DSD Project Manager. Disclosure ...
Real-time
Human. -Computer Interaction. with . Supervised...
MIO Alpha User Guide
Complete User Guide MIO Alpha User GuideTable of C...
Defining your
next generation desktop. Peter Menham. Technology...
User-Centric Management of Wireless LANs
Group 9. {. Summary. User–centric vs. AP-centr...
DNA Extraction: A User’s Manual
Margarita Hernandez . Instruction Manual . ENC325...
Eli Research and Engineering Inc.
with . TOTAL. T. otal ...
ECE454/CS594
Computer and Network Security. Dr. . Jinyuan. (...
Secure Information Sharing Using
Attribute Certificates and Role Based Access Cont...
Honeywords:
Making Password-Cracking Detectable. by Ari . Ju...
The “NUTS & BOLTS” of Building A Sewer & Water
Presented by: John R. Woodard, MS . GIS Specialis...
Aggression in sport
Definition. “Any behaviour that is intended to ...
User’s Guide
Linktropy
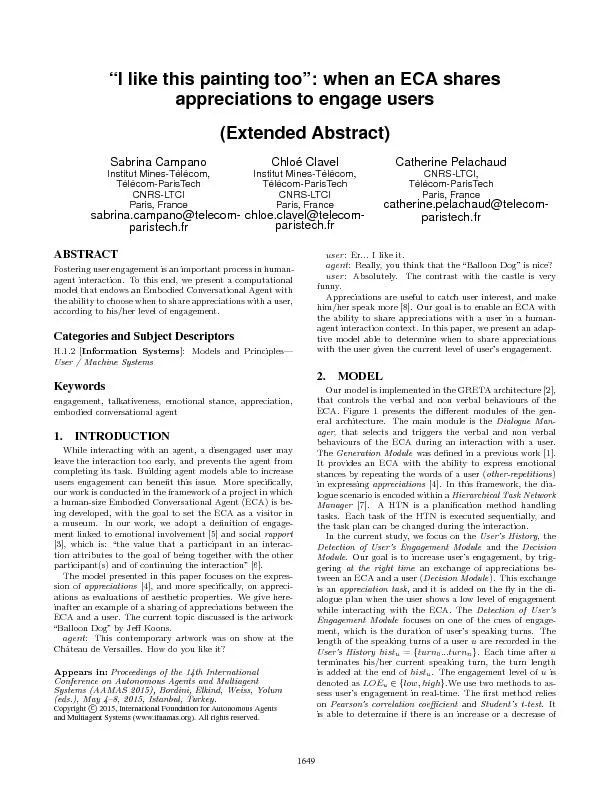
Figure1:Generalarchitectureoftheappreciationmoduleuser'stalkativeness,
user’s speech DIALOGUE MANAGER D etection ...
Recommender Systems
Problem formulation. Machine Learning. Example: P...
On Frequent
Chatters Mining. Claudio Lucchese. 1. st. HPC La...
William H.
DeLone. Ephraim . R. McLean. Information Systems ...
Susie’s lecture notes are in the presenter’s notes, bel
Disclaimer: Susie may have made errors in transcr...
BACKSEAT BABY ALARM USER AGREEMENT AND WAIVER OF LIABILITY
The agreement of the purchaser or recipient of th...
Computer Forensics
Principles and . Practices. . Edited slide-...
Archiving and Retention in Exchange 2010
Andrew Ehrensing. Principal Consultant. Microsoft...
Planning the USERRA Investigation
Organization Critical. ■ . Prepare a . written ...
Clarification in Spoken Dialogue Systems
: Modeling . User Behaviors. Julia Hirschberg. Co...
Speech-to-Speech Translation with Clarifications
Julia Hirschberg, Svetlana Stoyanchev. Columbia U...
The Classmate
Sharable Social Scheduler System. Presented by Te...
The Pledge or Betrothal is a declaration of intent. You declare tothe
16 17 F. ________, will you have ________ to ...
Log Based Query Recommendation
Speaker: . Rui-Rui. Li. Supervisor: Prof. Ben Ka...
How much can Behavioral Targeting Help Online
Advertising. Harini. . Sridharan. Stephen Durask...
A Two-Dimensional Click Model for Query
Auto-Completion . Yanen. Li. 1. , . Anlei. Dong...
Modelling
Relevance and User Behaviour in Sponsore. d Sear...
Click
Evidence . Signals . and Tasks. Vishwa Vinay. Mic...
Protecting
Client Data . with . System Center. Data Protecti...
Electronics Diversified, Inc.
Bijou Control Console User Manual
Location Privacy
CompSci. 590.03. Instructor: Ashwin Machanavajjh...