Search Results for 'Ieee Security'
Ieee Security published presentations and documents on DocSlides.
Social Network
Priyanka. . Agrawal. Abstract. Social Networks t...
Defending Against Modern Cyber Advisories
Rajitha. . Udayanga. , CISSP | rajitha.udayanga...
3GPP TSG SA WG3 Security
Draft Reply to S3-030672 on use of authentication ...
3GPP TSG SA WG3 Security
151 09 - 13 February 2004 Edinburgh, Scotland, UK ...
3GPP TSG SA WG3 Security
3GPP TSG CN WG4 Meeting #21 N4-031152 Bangkok, Tha...
IEEE ISPLC
2015 Proposal. General Chair. : Brian L. Evans, ...
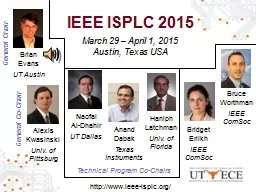
IEEE ISPLC 2015
March 29 – April 1, 2015. Austin, Texas USA. Al...
Condover Hall Meeting
Wednesday 25. th. February 5:30 – 6:00pm. Agen...
Morning Work – RELA
December 1. st. – December 5. th. . Monday �...
ColdFusion Security Review
Presented by Denard Springle. NVCFUG January, 201...
Recalibrating Homeland Security
Mobilizing American Society to Prepare for Disaste...
Wayne Coleman
FTZ Networks. President. wcoleman@ftznetworks.com...
How Smart Government Collects Debt
Michelle Burk. CIO. Ohio Attorney General Mike De...
Farmland Law Food Security Working Group
The author w the staff of t goes out t o assis...
UNCLASSIFIED
Village Stability Operations . Pre-Mission Tr...
Lecture
11. Intrusion Detection (. cont. ). modified from...
Lecture
1: . Overview. modified from slides of . Lawrie. ...
Lecture 1:
Overview. modified from slides of . Lawrie. Brow...
Computer Security
Hugo . Andr. és López. Summary. Distributed Sys...
Chapter 14
Computer Security Threats. Dave Bremer. Otago Pol...
Computer Security: Principles and Practice
EECS710: Information Security. Professor Hossein ...
Ethical and Legal Aspects of Computer Security
Computer Crime/Cybercrime. “Computer crime, or ...
Hi – 5
Marcus Hogue. Chris Jacobson. Alexandra Korol. Ma...
Viruses
Chris Howe and Patrick . Weingardt. Introduction....
Computer Security
set . of slides . 6. Dr Alexei Vernitski. Viruses...
HIPAA Security Awareness
What You Need To Know. Training Overview. This co...
Restructuring & Turnaround –
Indian . Scenario. IAIP Speaker Event. The India...
Michelle Lane
Augmented Reality Contact Lenses. The . overlayin...
I’m using a Black ball point pen
To ensure the security of your mail when you move ...
IntroductionAttackvectorsCounteractivemeasuresConclusionandoutlook ...
Shortandcrispdetailsaboutme StudyingIT-Securityatt...
Cordless Systems and Wireless Local Loop
Class Contents. Cordless systems. . Time Division...
Does Social Security Continue to Favor Couples?
by . Karamcheva. , Wu and . Munnell. . D...
Equip Inc. Custom Security Covers
Retail Covers for RMUs, Kiosks, Fixtures and Disp...
COS 433: Cryptography
Princeton University . Spring 2010. Boaz Barak. L...
Fall 2008
CS 334: Computer Security. Slide #. 1. Malicious ...
PART-IProposals for Electoral Reforms1.AFFIDAVITS TO BE FILED BY CANDI
2.NEED TO INCREASE THE SECURITY DEPOSIT OF CANDIDA...
Indian Diplomacy At Work
UN SECURITY COUNCIL REFORMS Our View India believe...
Web-Based Attacks
: Offense. Wild . Wild. West. Bob,. Jeff, and J...
Section 2.3 – Authentication Technologies
1. Authentication. The determination of . identit...
Merchant Card Processing
(PCI Compliance for Supervisors). Sponsored by UW...