Search Results for 'Giac Security Expert (gsecertification'
Giac Security Expert (gsecertification published presentations and documents on DocSlides.
2011 IEEE Symposium on Security and Privacy1081-6011/11 $26.00
152 148 150 156 159 154 151 153 155 160 158 161 15...
FINDING THE LOGIC OF ARGUMENTATION
Douglas Walton. CRRAR. Coimbra, March 24, 2011. N...
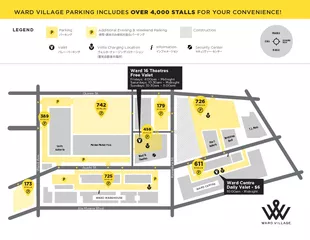
Ward Ave.Kamake‘e St.Auahi St.Ala Moana Blvd.Queen St.
LEGEND Additional Evening & Weekend Parking Inform...
EZID data security and risks
Situation. EZID is “system of record”: data i...
Skin Reaction to Essential Oils
Video with Dr. Scott. http. ://bit.ly/1CrAM1f. Es...
Deferred Action for Childhood Arrivals
Penn for Immigrant Rights . What is it?. Deferred...
New Recruits-What does it take to attract the younger gene
. Ann Thor, M.D.. The Multigenerational Workforc...
Nuclear Security Summit 2014
Chairs: Hank Chau, . Evonne. Pei, Jonathan Wu. M...
Ascension Point Capital
An Entrepreneurial Investment Firm. Table of Cont...
Security you can trustThe marine museum OZEANEUM in Stralsund in North
WRBFL27 Wavy LineReversible key system with a wave...
Consulting and planningStructured and thorough planning is the basis o
Security you can trustThe marine museum OZEANEUM i...
Common Weal : Submission to
The Expert Group on Welfare The Common Weal Comm...
by Jim Hightower Where's the Department of Homeland Security when we r
only evasive answers, so they got to organizing, w...
Snart får vi nya rutiner för löner och förmåner.
Sverige är först ut.. Date Created: [YYYY-MM-DD...
Security Evaluation of an
Organization. TA. Md. . Morshedul. Islam. Proce...
Janna
Miletzki. , LSE, Human Geography. Refugees in a S...
Improving Application Security with Data Flow Assertions
Yip, X. Wang, N. . Zeldovich. , M. F. . Kaashoek....
Resistance Welding Manual
2 Ruukki is a metal expert you can rely on all the...
Network Security Essentials
Fifth Edition. by William Stallings. Chapter 1. I...
Cryptography and Network Security
William Stallings, 6. th. Ed. . Chapter 1. Overv...
Introduction to Computer and
Network Security. Chapter #1 in the text book ( S...
Chapter 14
Computer Security Threats. Seventh Edition. By Wi...
CS457 – Introduction to Information Systems Security
Cryptography 1a. Elias Athanasopoulos. elathan@ic...
Chapter 7: Assuring Safety and Security in Healthcare Inst
Safety and Security – Risk?. Health facilities ...
How do we assign words meaning?
Connotation vs. Denotation . SWBAT. Define connot...
The Electoral College
Used for presidential elections. Framers had conc...
Mobile Threats and Attacks
Possible attack threats to mobile devices. Networ...
Attackers Vs. Defenders: Restoring the Equilibrium
Ron Meyran. Director of Security Marketing. Janua...
Lecture
14. Intrusion Detection. modified from slides of ...
OWASP Web
Vulnerabilities . and Auditing. Not just another ...
Crisis Action Plan
Troy University Police Department Dothan Campus. ...
Modelling and Multi-Objective Optimization of Quality Attri
Rafael Olaechea, Steven Stewart, Kryzstof Czarnec...
1 ````````````````````````````````````````
AEGIS . A Fast Authenticated Encryption Algorithm...
Distributed Web Security for
Science Gateways. Jim Basney. jbasney@illinois.ed...
Securing User Access with Multi-Factor Authentication
Sarah . Fender, Director of Product Marketing . S...
Troubleshooting
Active Directory Federation Services (AD FS) and ...
Chapter 4
Authentication policy. Cyber Security for Educati...
Security of Authentication Protocols
Alexander . Potapov. Authentication definition. P...
Provide a second layer of security to access site in
Joomla. Two Factor Authentication (TFA) is a 100%...
Web Security
CS598MCC Spring 2013. Yiwei. Yang. Definition. ...