Search Results for 'Facet Random'
Facet Random published presentations and documents on DocSlides.
Random Number Generation
CSCI 5857: Encoding and Encryption. Outline. D. e...
CS 450 – Modeling and Simulation
Dr. X. Topics. What Does Randomness Mean?. Random...
On Combinatorial
vs. Algebraic. Computational Problems. Boaz Bara...
Exam I review
Understanding the meaning of the terminology we u...
Advanced Java and Android
Day 1. Object-Oriented Programming in Java. Advan...
Investor Contagion: A Network Model for Asset Markets
James Luo. ELE 381. Mini-project Presentation. In...
Randomized and Quantum Protocols in Distributed Computation
Michael Ben-Or. The Hebrew University. Michael Ra...
Environmental Data Analysis with
MatLab. Lecture 23:. Hypothesis Testing continued...
Enhancing Fluid Animation with Adaptive, Controllable and
Ye Zhao. , . Zhi. Yuan and Fan Chen. Kent State ...
Possible counter
- attacks against random geometric distortions Jea...
Statistics for
Engineers. Lecture 2. Antony Lewis. http://cosmol...
Statistics for Engineers
Antony Lewis. http://cosmologist.info/teaching/ST...
Stats for Engineers Lecture 6
Answers for Question sheet 1 are now online. http...
CHAPTER 6
Control Problems in Experimental Research. Chapte...
Efficient Triangle Counting in Large Graphs via Degree-base
. Charalampos (Babis) E. Ts...
Numerical Methods for Empirical Covariance Matrix Analysis
Miriam Huntley. SEAS, Harvard University. May 15,...
Genetic Algorithms
Chapter 3. GA Quick Overview. Developed: USA in t...
Linear Cryptanalysis of DES
M. Matsui.. Linear Cryptanalysis Method for DES C...
Secrets & Lies, Knowledge & Trust.
(Modern Cryptography). COS 116, Spring . 2012. Ad...
Cryptography
Lecture 1. Arpita. . Patra. Welcome to the secon...
Cryptology
Passwords . and Authentication. Prof. David . Sin...
PHA Bioplastics
Synthesis and Material Properties. University of ...
Commensal
Cuckoo. : Secure Group Partitioning for Large-Sc...
How many daisies?
Aims. To understand how scientists count . organi...
Better Pseudorandom Generators from Milder Pseudorandom Res
Raghu Meka (IAS). Parikshit Gopalan, Omer Reingol...
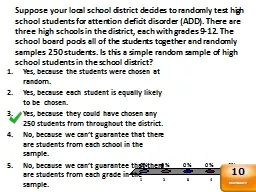
Suppose your local school district decides to randomly test
Yes, because the students were chosen at random.....
Session 4
Asymmetric ciphers. Contents. Definition of asymm...
Decoupling with random quantum circuits
Omar Fawzi (ETH Zürich). Joint work with Winton ...
Symmetric-key algorithms
Symmetric-key algorithms. use the same cryptograp...
Authentication
Authentication with symmetric key. Server sends r...
Explaining
Matlab’s. Axis Alignment. When it deems it pra...
Anatomy of Attack: Code Red
Dan Fleck. CS 469: Security Engineering. These sl...
Chapter 2 Title and Outline
1. 2. Probability. 2-1 Sample Spaces & Even...
In addition, the IOC will conduct further random and unannounced tests
). As with previous editions of the Games, sample...
Data Destruction
How to Erase your Hard Drive’s so that there is...
Zipf’s
monkeys. Observations from real and random genom...
DeepFont
: Large-Scale Real-World Font Recognition from Im...
Evolutionary Mechanisms
Genetic Drift (and Inbreeding). DEVIATION. . fro...
1 Econometrics
Advanced . Panel Data Techniques. 2. Advanced Pan...
Secure Storage
1. Lost Laptops. Lost and stolen laptops are a co...