Search Results for 'Enter Security'
Enter Security published presentations and documents on DocSlides.
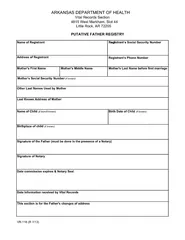
ARKANSAS DEPARTMENT OF HEALTH Vital Records Section
g icoRegistrant’s Social Security Numbertnart...
Slide Heading
Security Auditing . Wireless Networks . Ted J. Eu...
Certificates:
“The Other Academic Credential”. September 10...
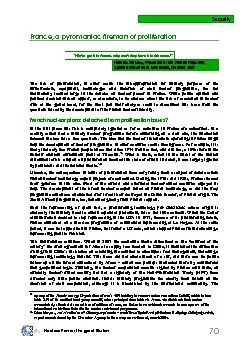
French nuclear plans: detached from proliferation issues? In the first
Security Nuclear Power: the great illusion 72 ...
Online Login Security Enhancement
Creating an online username & password. Janua...
1 Core-CT
Student Worker Self Service. Time and Attendance...
Chapter 12 – Dependability and Security Specification
Lecture 1. 1. Chapter 12 Dependability and Securi...
1 iSecurity GUI
for. U. ser . Management. . 2. Internationally r...
Find and enter a chat room
Use Lync search to find rooms . that you have acc...
Let the Market Drive Deployment
A Strategy for Transitioning to BGP Security. Phi...
Content Management Systems
What Your Mother Never Told You…. What is Stati...
Spring 2015 Test Coordinators
Pretest Workshop. 1. Contact Information. Cherie ...
Managing and Protecting Key Company Assets:
Trade Secrets . Pamela Passman. President and CEO...
Introducing
Cisco Networking Academy. Speaker Name. Title / R...
This article was downloaded by: [University of Chicago]On: 14 August 2
Security StudiesPublication details, including ins...
CLARIN AAI,
Web Services Security Requirements. Daan Broeder....
Social Network
Priyanka. . Agrawal. Abstract. Social Networks t...
HSMM-PI VPN Setup
Presented by . W1BAW Bruce Wattendorf. What is a ...
AWE Approval Administration Reassign and Approval ScenariosRole assign
Enter EMPLID, Begin & End Date range, and select P...
Defending Against Modern Cyber Advisories
Rajitha. . Udayanga. , CISSP | rajitha.udayanga...
3GPP TSG SA WG3 Security
Draft Reply to S3-030672 on use of authentication ...
3GPP TSG SA WG3 Security
151 09 - 13 February 2004 Edinburgh, Scotland, UK ...
3GPP TSG SA WG3 Security
3GPP TSG CN WG4 Meeting #21 N4-031152 Bangkok, Tha...
Condover Hall Meeting
Wednesday 25. th. February 5:30 – 6:00pm. Agen...
Morning Work – RELA
December 1. st. – December 5. th. . Monday �...
ColdFusion Security Review
Presented by Denard Springle. NVCFUG January, 201...
ColdFusion On The Cloud
Amazon EC2 and S3. Presented by Denard Springle @...
Recalibrating Homeland Security
Mobilizing American Society to Prepare for Disaste...
Wayne Coleman
FTZ Networks. President. wcoleman@ftznetworks.com...
How Smart Government Collects Debt
Michelle Burk. CIO. Ohio Attorney General Mike De...
Farmland Law Food Security Working Group
The author w the staff of t goes out t o assis...
Responsibilities and Strategies for Recitation TAs
1 enter for the nhancement of eaching and TAweb TA...
UNCLASSIFIED
Village Stability Operations . Pre-Mission Tr...
Welcome to Technology
Ms. . Swartwout. Today we will:. Talk about class...
Lecture
11. Intrusion Detection (. cont. ). modified from...
Lecture
1: . Overview. modified from slides of . Lawrie. ...
Lecture 1:
Overview. modified from slides of . Lawrie. Brow...
Computer Security
Hugo . Andr. és López. Summary. Distributed Sys...
Chapter 14
Computer Security Threats. Dave Bremer. Otago Pol...
Computer Security: Principles and Practice
EECS710: Information Security. Professor Hossein ...








![This article was downloaded by: [University of Chicago]On: 14 August 2](https://thumbs.docslides.com/149640/this-article-was-downloaded-by-university-of-chicago-on-1.jpg)