Search Results for 'Edition Security'
Edition Security published presentations and documents on DocSlides.
Last updated: 4-24-2015 The INI discourages students from enrolling in
Information Security and Privacy
Chapter 6
Portfolio Risk and Return: Part II. Presenter. V...
A Parallel Repetition Theorem for
Any. Interactive Argument . Or . On. . the Ben...
What Anyone Can Know
The Privacy Risks of Social Networking Sites....
Anywhere Roadmap:
Construction Ahead. Goals for Anywhere. Hardware/...
BUY BACK OF SECURITIES
By Vishal Shah. Synopsis. Introduction & Hist...
THE ORANGE BOOK
Ravi Sandhu. ORANGE BOOK CLASSES. A1 Verified Des...
This edition 4
February 2003 PRS PALLET RETURN SYSTEM PALLETS Edi...
Cloud Survey Results
CSG 9/13. Thank you. UW. -Madison . Penn . State ...
RedPanda_MD Edition Date
Red Panda Photo courtesy of Karen Marzynski Habita...
EN107 Week one
How to read a play. From course materials. 'In . ...
Physical Layer Security Made Fast and Channel-Independent
Shyamnath Gollakota. Dina Katabi. What is Physica...
Transportation Security AdministrationPage of 1
REV 4, 122012 Smart SecuritySaves Time… Parac...
The dark side of standards
Luis Jorge Romero . Gobal. Wireless Summit, Aa...
We, the Heads of State or Government of on Security and Co-operation i
Now that a new era is dawning in Europe, we are d...
Litigation Holds:
Don’t Live in Fear of Spoliation. Jason Pufahl....
Patches for Optimal UptimeSteve Beattie, Seth Arnold, Crispin Cowan, P
Beattie, et al.security resources. Wave used the e...
A Trend Micro White Paper | March 2012
Virtual Patching: Lower Security Risks and Costs ...
),2009 ff, and directed ncse, 2008, an online edition of nineteenth-ce
Victorian Aesthetic Conditions:Pater Across the Ar...
Moving Target Defense in Cyber Security
Jianjun “Jeffrey” Zheng. July 2014. Moving Ta...
(DRAFT) Section 1. Patrol Organization
the objective. The security unit secures the obje...
Secure Computation with
Minimal Interaction, Revisited . Yuval . Ishai. ...
Form Approved
SOCIAL SECURITY ADMINISTRATION TOE 250 OMB No. ...
Five important considerations when choosing a rep payee
According to the Social Security Administration (S...
Chapter 11 – Security and Dependability
Lecture 1. 1. Chapter 11 Security and Dependabili...
SOCIAL SECURITY ADMINISTRATION
BALTIMORE, MD 21235 - 0001 SOCIAL SECURITY The Co...
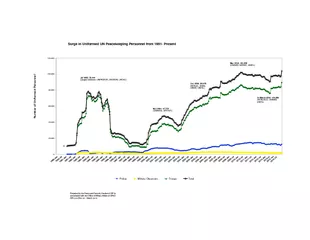
Prepared by the Peace and Security Section of DPI inconsultation with
20,00040,00060,00080,000100,000120,000Number of Un...
Written Technical
Communication (Part II) . Klara. Nahrstedt. We a...
RBI Guidelines
Report of the Working Group on Electronic Banking...
312. Perfection of security interests in chattel paper, deposit accou
G.S. 25 - 9 - 312 Page 1
Perfecting a Security Interest in an LLC Membership Interest in Virgin
Thompson McMullan, P.C. (804) 698-6223 / rbowen@t-...
U.S.-Mexico 21
st. Century Border Initiative. Roger Petzold. Fe...
Your guide toeffectiveand responsiblecitation analysis
AnneWil Harzing The Publishor PerishBook Edition: ...
This presentation is a section of the Brush Strokes PowerP
Noden. . It comes from the book . Image Grammar. ...
New Servelec
permeating security technology inspired by the d...
European Scientific Journal July edition vol. 8,
No.16 ISSN: 1857 – 7881 (Print) e - IS...
AUTHENTICATION IN the CLOUD
Are we really safe in the cloud?. G-Force. Veron...
Cloud Computing
An In-Depth Discussion. Introductions. Nathaniel ...