Search Results for 'Block Lightweight'
Block Lightweight published presentations and documents on DocSlides.
Block Paving
36 www.marshalls.co.uk/commercial/block-paving Teg...
An Optimized AMPM-based
Prefetcher. Coupled with Configurable Cache Line...
LISA: Design of Experiments
By Chris Franck. About LISA. Laboratory for Inter...
Random Number Generation
CSCI 5857: Encoding and Encryption. Outline. D. e...
Scott Aaronson (MIT)
Andris. . Ambainis. (U. of Latvia). Forrelation...
Teaching for Mastery
The vision of the new curriculum in England. Robe...
Maria Matuszczak MD
Professor of Anesthesiology. Division Chief Pedia...
Three Days of the Good Parts
Douglas Crockford. The First Day. Programming Sty...
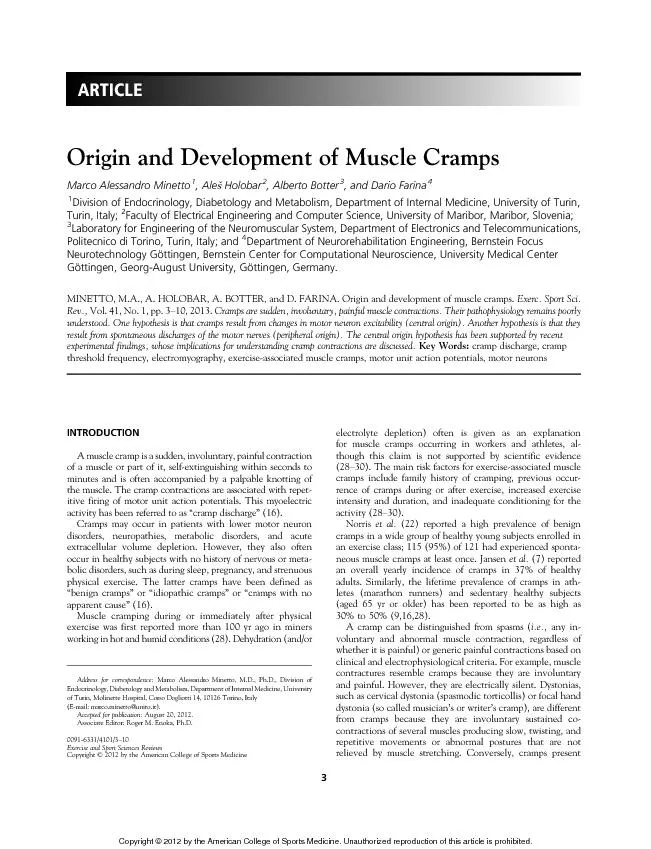
(21).Weelectricallyelicitedmusclecontractionsinthe
abductorhallucisofhealthysubjectsinthepresence(blo...
Reliability analysis of ZFS
CS 736 Project. University of Wisconsin - Madison...
Floating Elements
1. The CSS . float. property (reference). 2. img...
North By Northwest (1959)
By Joseph . Ratcliffe. Opening Title Sequence: Wh...
Simulations of Memory Hierarchy
Lab 2: Cache Lab. Overview. Objectives. Cache Se...
Integrating Quotations
Notes #12. There are three options for integratin...
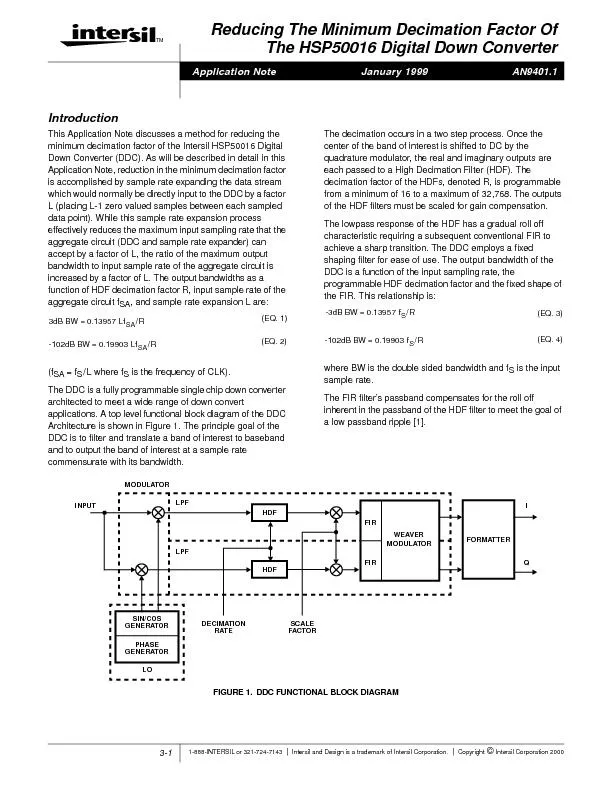
The FIR
3-2 FIGURE 2.BLOCK DIAGRAM SPECTRAL REPRESENTATION...
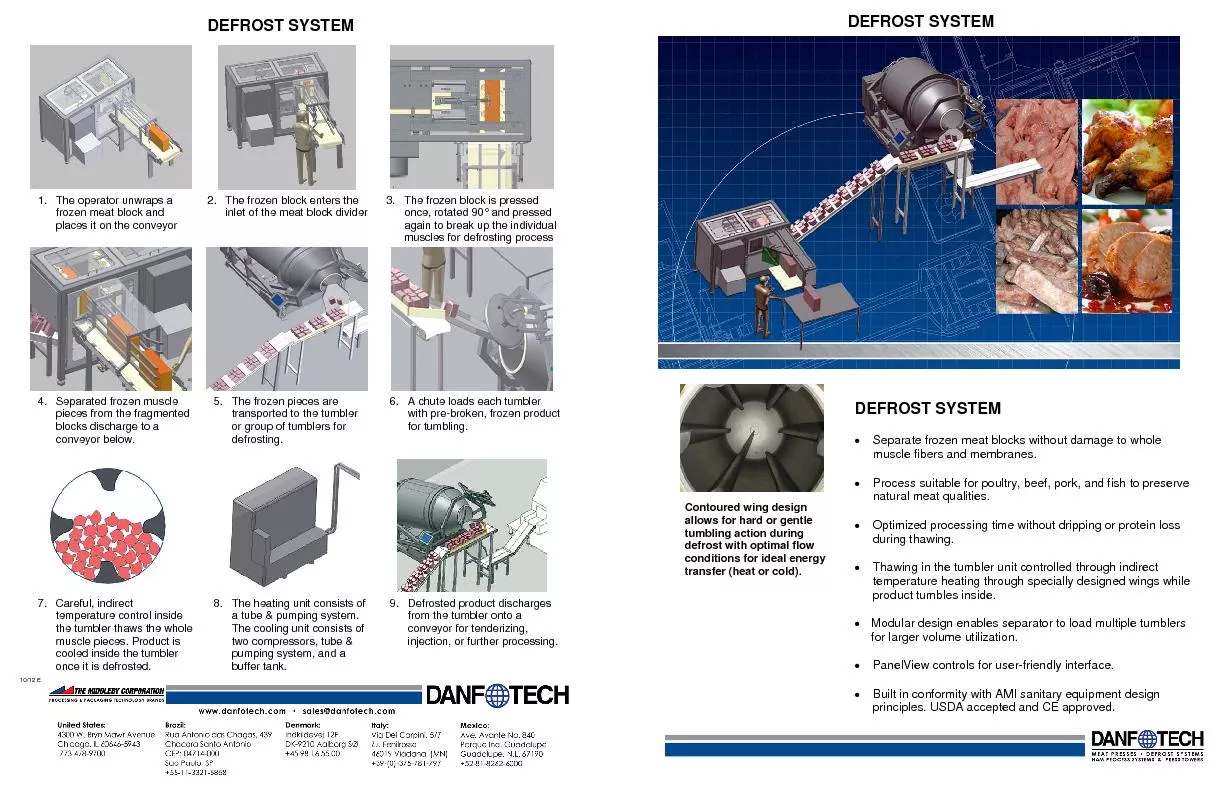
The operator unwraps a frozen meat block and places it on the conveyor
Separated frozen muscle pieces from the fragmented...
Chap-6: Friction
Frictional forces are unavoidable in our daily li...
1 Symmetric-Key Encryption
CSE 5351: Introduction to Cryptography. Reading a...
Block ciphers 2
Session 4. Contents. Linear cryptanalysis. Differ...
Cryptography and Network Security
Sixth Edition. by William Stallings . Chapter 3. ...
Cryptography
Aalto . University. , . autumn. . 2012. Outline....
Cryptography and Network Security
Chapter 3. Fifth Edition. by William Stallings . ...
Understanding Cryptology
Core Concepts. Dr. Kerry A. McKay. 1. Approved fo...
Ln Lou
2014.8. Modern Cyphers. 0. . Security System. Key...
Dam Rehabilitation & Improvement Project
First National Level Steering Committee Meeting. ...
Copyright
© . 2014. . The McGraw-Hill Companies, Inc.. Sys...
Introduction to
the design (and analysis) of experiments. James M...
DeadSpy
A Tool to Pinpoint . Program Inefficiencies. Mili...
CS168: Debugging
Introduction to GDB, . Wireshark. . and . Valgri...
A Lightweight Interactive Debugger for Haskell
Simon Marlow. José Iborra. Bernard Pope. Andy Gi...
Synchronization Exercises
Exercise . 1 . Let S be a . semaphore . that is i...
Symmetric-key algorithms
Symmetric-key algorithms. use the same cryptograp...
Security Fundamentals
Noah Mendelsohn. Tufts University. Email: . noah@...
Eagan Wildcat Defense 2014
Practice Priorities – Achieve What You Emphasiz...
Chapter 11.2
Types of Mountains. The process of building a mou...
Prentice
. Hall. . EARTH SCIENCE. Tarbuck. ...
Disposal of Disk and Tape Data by Secure Sanitization
EECS711 : Security Management and Audit . Spring ...
TAZ/TAD delineation program overview
Overview. Traffic Analysis Zone (TAZ) and Traffic...
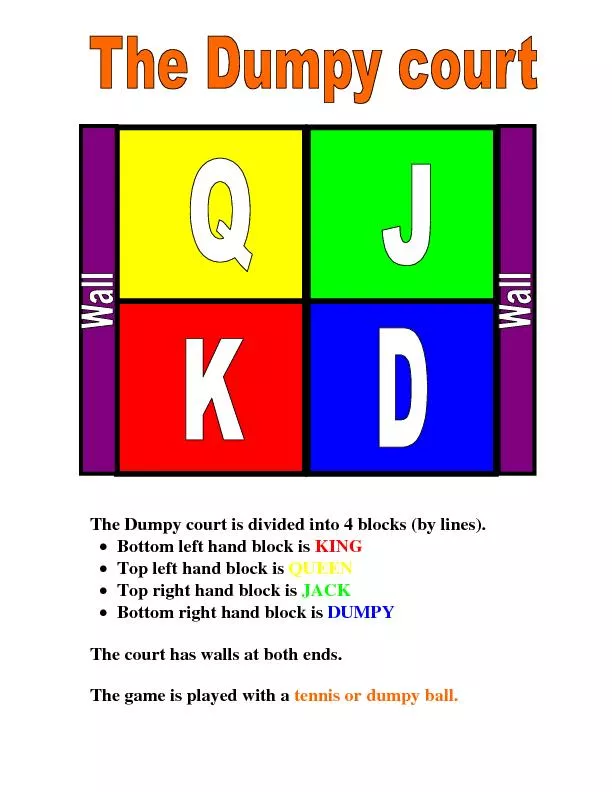
The Dumpy court is divided into 4 blocks (by lines).
Bottom left hand block is KING ...
Block ciphers
Exhaustive Search Attacks. Online Cryptography Co...