Search Results for 'Bit Attacker'
Bit Attacker published presentations and documents on DocSlides.
Using Attacker Capabilities and Motivations in Estimating Security Risk Lot ben Othmane Dept
of Mathematics and Computer Science Eindhoven Uni...
From Patches to HoneyPatches Lightweight Attacker Misdirection Deception and Disinformation Frederico Araujo Kevin W
Hamlen The University of Texas at Dallas frederic...
WHITE PAPER THE ATTACKER WITHIN ABSTRACT As enterprise defenses evolve so too do the attack vectors leveraged by those seeking to bypass such controls
We are entering an era where attackers are no lon...
From Patches to HoneyPatches Lightweight Attacker Misdirection Deception and Disinformation Frederico Araujo Kevin W
Hamlen The University of Texas at Dallas frederic...
TRE PASS PlugandPlay Attacker Proles for Security Risk
pieters dhadziosmanovic tudelftnl University of Tw...
Grapple Flowchart:
Initiating a Grapple Attacker rolls CMB vs Defend...
This paper considers the problem of an attacker disrupting an en-crypt
by whether or not a node sends a short packet (i.e...
Juice:
A Longitudinal Study of an SEO Campaign. David ...
Tom Cross, Drawbridge Networks
Dave Raymond, West Point. Greg Conti, West Point....
Viruses, Worms, Zombies, and other Beasties
COS 116, . Spring . 2012. Adam Finkelstein. Encry...
DoS Threats for Cognitive Radio Wireless Networks
Carl A. Gunter. University of Illinois. With Omid...
Malware
Computer Forensics. Attack Phases. Computer Foren...
COUNTEREXAMPLES
to. Hardness Amplification. beyond negligible. Ye...
Advanced Persistent Threats
(APT). Sasha Browning. Breakdown . Advanced. Comb...
Analyzing and Profiling Attacker Behavior in Multistage Int
1. Contents. Introduction and Background. Literat...
Principles of Play
Systems of Play. Styles of Play. “Understanding...
Denial of Service
Denial of Service Attacks. Unlike other forms of ...
Denial of Service
Denial of Service Attacks. Unlike other forms of ...
Security Lab 2
MAN IN THE MIDDLE . ATTACK. Objectives. To unders...
Physical Layer Security
1. Outline. 2. Overview. Physical Security in Wir...
SCSC 555 Computer Security
. Chapter 10 Malicious software. Part B. Index....
Hey, You, Get Off of My Cloud
Exploring Information Leakage in Third-Party Comp...
Blood stain analysis
Objective: to understand how blood stains can giv...
July 2013 Microsoft Security Bulletins
Jonathan Ness. Security Development Manager. Dust...
October 2013 Microsoft Security Bulletins
Jonathan Ness. Security Development Manager . Dus...
Techniques for Self-Defense
By: Juan Sotelo. EDSC 304. What is Self-Defense?...
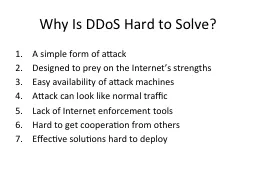
Why Is DDoS Hard to Solve?
A simple form of attack. Designed to prey on the ...
Authenticated Encryption
CBC paddings attacks. Online Cryptography Course ...
Message integrity
Message Auth. Codes. Online Cryptography Course ...
Mitigating
DoS. Attacks against Broadcast. Authentication i...
Competitive
Fall. 1. st. Session. U11/U12 – Individual D...
Computer Forensics
Network Protocols. Overview for Network Forensics...
Information About Microsoft
July 2012 Security Bulletins. Jonathan Ness. Secu...
Beyond Reactive Management of Network Intrusions
Professor Sushil Jajodia. Center for Secure Infor...
Intrusion Detection Research
Stephen Huang. Sept. 20, 2013. News. 2. http://ar...
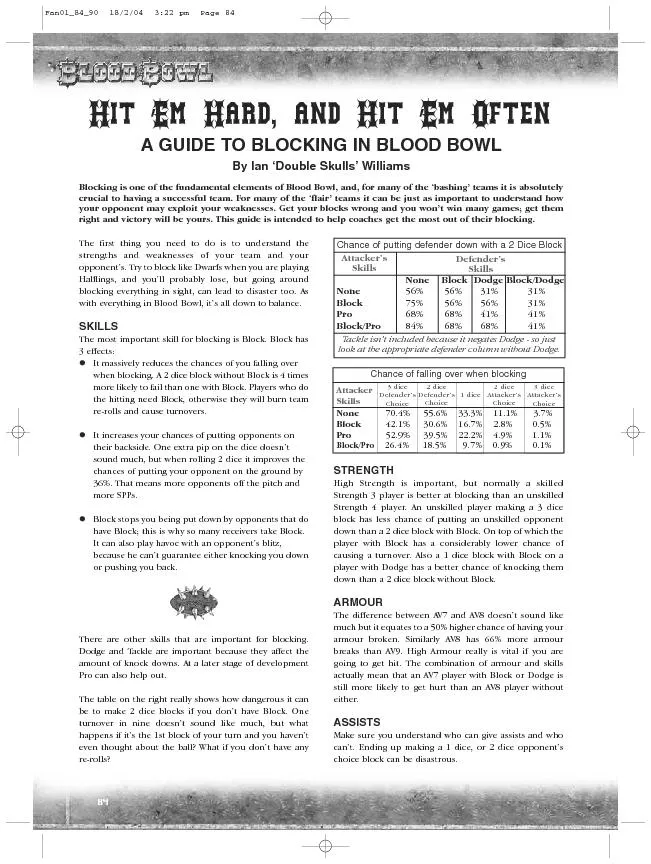
70.4%55.6% 33.3%11.1% 3.7%42.1% 30.6%16.7% 2.8%0.5%Pro5
Attacker Chanceoffallingover whenblocking Defender
Quantification
of Integrity. Michael Clarkson and Fred B. Schnei...
Finding Vulnerable Network Gadgets in the Internet Topology
Author: Nir Amar. Supervisor: Dr. Gabi Nakibly. B...
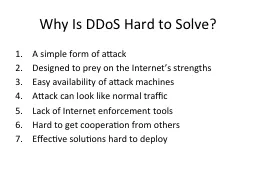
Why Is DDoS Hard to Solve?
A simple form of attack. Designed to prey on the ...
Cryptography
Lecture 1. Arpita. . Patra. Welcome to the secon...