Search Results for 'Attacks Hackers'
Attacks Hackers published presentations and documents on DocSlides.
Microsoft Advanced Threat Analytics
Tõnis Tikerpäe. Primend Service Manager. Micros...
Dell & Trend Micro
Boost VM Density with AV Designed for VDI. TJ Lam...
This Material Will Not be
In Final Exam. Cross-Site Scripting (XSS). What i...
CSE 592
Internet censorship . (FALL 2015). Lecture . 16. ...
Detecting and Blocking
SiteScraping Attacks Protecting Valuable Data and ...
IDS & IPS
Team Members. - Sudeera . - Ramitha. - Ni...
Secure communication through
ssh. tunneling. By Chris . Zachor. CS 650. Outli...
Atlas Activity (pages 92-93)
American Troops Fight the Korean War. Time and Ch...
Fight back at ATM card skimming attacks
Protect your ATM network from the risk and associa...
While individual technologies can identify many attacks, only a connec
Technical Brief 2 The implementation of sandboxing...
Vulnerability Analysis of Web-Based Applications
Part 2. Authors: Marco . Cova. , . et al.. Presen...
Numbers 16-21
Exodus & Wandering in the Wilderness. Wanderi...
Use Cases for I2RS
I2RS Interim Meeting. Nicolai Leymann, Deutsche T...
1 Constraint-Based Watermarking Techniques for Design IP Pr
Presented by : Yaniv Sabo. 2. Introduction. The a...
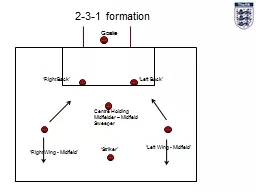
Goalie
2-3-1 formation. ‘Right Back’. ‘Left Back�...
Social-Engineering & Low-Tech Attacks
CSH6 Chapter 19. “Social Engineering & . Lo...
Population Geography
Managing Population Growth. A WebQuest for . Grad...
Security Report
Security Empowers Business THE VISIBILITY VOID Att...
Speakers:
Yanyan . Ni, . Yeze. Li. Outline. Introduction. ...
Beagles
By Helen Kerfoot 9. Teacher Mrs.Butzin . Topic ho...
Increasing Anonymity via Dummy
Jondos . in . a. Crowd. Author: Benjamin Winning...
Celebrities
With. . Mental Health Issues. Adam Wall. Student...
Data Breach Prevention and Response: Front-End Detection an
Today’s Moderator. Bruce MacDougall . Senior Vi...
Group 9
Exploiting Software. Exploiting Software . The ex...
House Foreign Affairs Committee
“ Assa d ’ s Abhorrent Chemical Weap...
Welcome to the MOB!
Merry Christmas! . Christmas Eve Services: . 5, 7...
Attacks and Counter Defense Mechanisms for Cyber-Physical S
1. Taha Hassan. Lulu Wang. CS 5214 Fall 2015. Ove...
1 Lect. 10 :
Cryptanalysis . 2. Block Cipher – Attack Scenar...
Malwares, Worms, and Web Issues
IT443 – Network Security Administration. Instru...
Denial of Service
Denial of Service Attacks. Unlike other forms of ...
Information Security – Theory vs. Reality
0368-4474, Winter 2015-2016. Lecture 5:. Side . ...
Penetrating Computer Systems & Networks
CSH6 Chapter 15. “Penetrating Computer Systems ...
Embedded systems Security
Graciela Saunders. overview. Introduction / Revie...
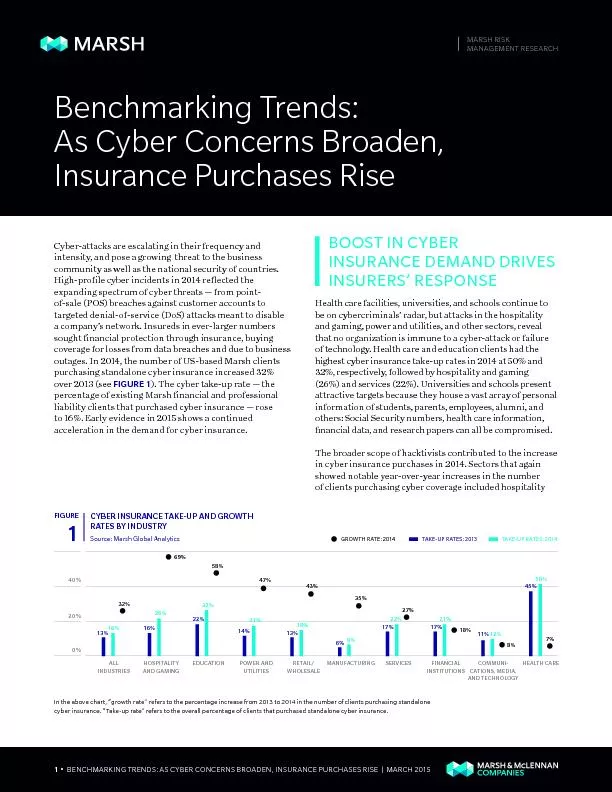
• BENCHMARKING TRENDS: AS CYBER CONCERNS BROADEN, INSURANCE PURC
Cyber-attacks are escalating in their frequency an...
Authentication
IT443 – Network Security Administration. Instru...
Eliminating Fine Grained Timers in
Xen. Bhanu Vattikonda. with . Sambit. Das and . ...
008: 6) to label the attacks as
Afrophobic (Matsinhe, 2011) nature of much of Sout...
Cryptosystems Provably Secure against Chosen Ciphertext Attacks ...
Naor IBM Research, Almaden Research Center 650 Har...
Social-Engineering & Low-Tech Attacks
CSH6 Chapter 19. “Social Engineering & . Lo...
Tackling the Insider Security Threat
b. y. Ahmad Muhammad. What is an Insider Security...