Search Results for 'Attack Threat'
Attack Threat published presentations and documents on DocSlides.
E-Commerce Technology Risk and Security
Brian Trevey and Randy Romes. Presenter Contact I...
2011 Infrastructure Security Report
7. th. Annual Edition. CE . Latinamerica. Carlo...
BGP FLOWSPEC OVERVIEW
DISTRIBUTED DENIAL OF SERVICE (DDOS) ATTACKS. IPS...
Assisting Students in Distress
Khalila Fordham, Psy.D.. Raquel Contreras, . Ph.D...
The Dark Menace:
Characterizing . Network-based . Attacks in . the...
Sample Research
Defenses. Pushback. Traceback. SOS. Proof-of-wor...
Ground Delivery of Fire Chemicals
Wildland Fire Chemical Systems (WFCS). Missoula T...
Competitive Off-season
3. rd. . Session – February 25. U11/U12 – In...
Increasing Protection
Last class we discussed the increase of intellect...
Hezbollah
Beirut, Lebanon. Patrixia. . Lansangan. Ben Schu...
Santa Anna is planning his
attack!. Alamo Journal- . Make . sure your first ...
All Quiet on the Western Front
By Erich Maria Remarque. All Quiet on the Western...
Data Breach Prevention and Response: Front-End Detection an
Today’s Moderator. Bruce MacDougall . Senior Vi...
Should You Stop Allopurinol During Acute Gout Attack
stopping allopurinol during acute gout attack. al...
Use of Cosmic-Ray Neutron Data in Nuclear Threat Detection
and Other . Applications. Neutron Monitor Com...
Airfoils
Airfoil. Any surface that provides aerodynamic fo...
The 1-hour Guide
to . Stuxnet. Carey . Nachenberg. Vice President...
Competitive Strategy
.. Outline. Introduction. Sustainable competitive...
Reclaim
An alien race . has . attacked earth and . driven...
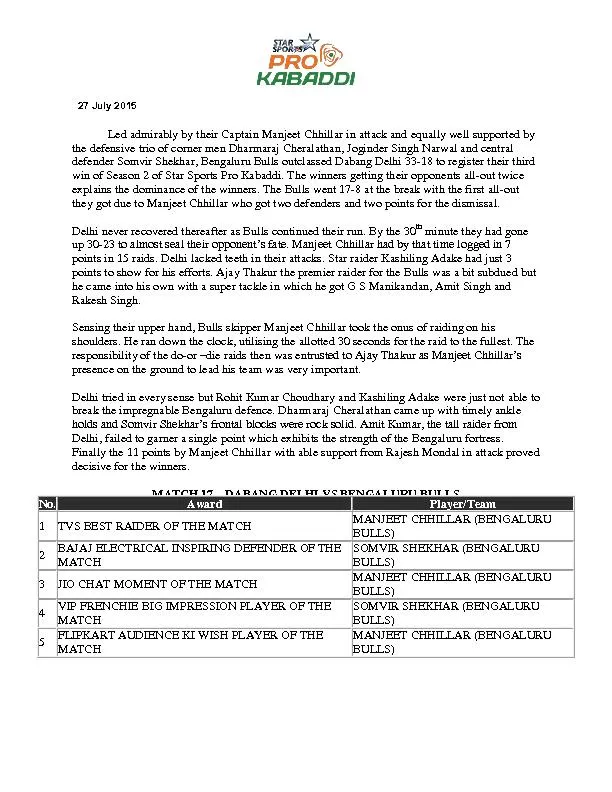
Led admirably by their Captain Manjeet Chhillar in attack and equally
the defensive trio of corner men Dharmaraj Cherala...
Operation Citadel: THE BATTLE OF TANKS
By: Mitchell S, Hari M, Avi R, Mark M, Ben R. THE...
Insider Threats
Challenges of Implementing an Insider Threat Prog...
Why SIEM – Why Security Intelligence??
. Sponsored by:. Presented by:. Curtis Johnson....
Diffie
-Hellman Key Exchange. CSCI 5857: Encoding and En...
3.4 Concavity and the Second Derivative Test
We will learn about:. Concavity -Points of Inflec...
The Mediterranean and the Eastern Front
(More notes from 32.1). Axis Forces Attack . Nort...
Valerie Heil
August 12, 2014. . UNCLASSIFIED. UNCLASSIFIED. N...
Pearl Harbour Attack
… and the Christian Connection.. Mitsuo. . Fuc...
1 Lect. 10 :
Cryptanalysis . 2. Block Cipher – Attack Scenar...
DES Analysis and Attacks
CSCI 5857: Encoding and Encryption. Outline. Conf...
in Emotionally Focused Work (pp. 1-8). Annandale: Institute for Emotio
This unexpected attack left Wendy with strong feel...
June 6, 1944
D-Day. General Eisenhower’s Message sent just p...
Planning Operation Overlord (D-Day)
If you were going to attack, where do you think w...
Key Features and BenefitsSurgical MitigationAutomatically remove only
Peakflow Threat Customer/Data CenterPeakflow Colle...
Denial of Service
Denial of Service Attacks. Unlike other forms of ...
At Least 12 Dead in Attack on French Newspaper
A local resident distributes coffee to reporters ...
The Genetic Fallacy
Beth . herold. What is it?. The Genetic fallacy o...
Application Usage and
Threat Report – Global Findings. February 2013....
Information Security – Theory vs. Reality
0368-4474, Winter 2015-2016. Lecture 5:. Side . ...
Side channel attacks
Computer Security 2014. Background. An algorithm ...