Search Results for 'Attack Retreat'
Attack Retreat published presentations and documents on DocSlides.
Intrusion Tolerance and Cloud
C. Edward Chow . Department of Computer Science. ...
Intrusion Tolerance and Cloud
C. Edward Chow . Department of Computer Science. ...
The Battle of Loos
Aim. To understand what happened at the Battle of...
Data Center
Security Overview. Dr. . Natheer. . Khasawneh. Z...
Cyber Resilient Energy Delivery Consortium
CREDC in a nutshell. identify and perform cuttin...
September 11 and Al Qaeda
Afghanistan: History. The September 11, 2001 terr...
Coastal preservation and climate change adaptation
Entry . Into Climate . Change Adaption . Surfride...
President Lauren Hawks
Vice-President David Jaffe. . Dress for Success: ...
Your DDoS Opportunity
Underestimating the Impact of DDoS. Jim Benanti �...
Check Point
DDoS Protector. June 2012. Cybercrime Trends for ...
An Assessment of the Social, Cultural and Institutional
Factors that Contribute to the Sexual Abuse of. P...
Volleyball Portfolio
Alyssa Chambers. Coaching Philosophy: High School...
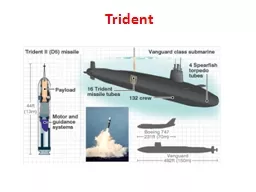
Trident
Trident. Trident. Warhead design. Some facts abou...
EN.600.424
Spring 2015. Lecture Notes. Introduction to Netwo...
Melanie A. Stegman, Ph.D.
Director, Learning Technologies Program. Federati...
Achieving Excellence in the Project and Priority Setting Pr
The Golden Circle Concept. ssssssssssssssssssssss...
SSUSH19
The student will identify the origins, major deve...
Malicious Code and Application Attacks
Unit - . 2. Outline. Malicious code. Password att...
HEART ATTACK!!
Did you know..?!. Heart disease is the leading ca...
Which are you?
Controller or Facilitator. Controller. One that e...
PUBLIC POLICY UNDER ATTACK – London 2011
A different look at teams:. Conflict, Metrics and...
APTShield
: A Real-Time Situation-Aware Detection System fo...
Protect Your DNS Services Against Security
Threats. Efficient IP Company Overview. Americas ...
Candid : Preventing SQL Injection Attacks Using Dynamic Can
2008. 09. 25. Presented by . Jeong-hoon. , Park. ...
Ramayama
Rama. . vs. . . Ravana. Good. . vs.. . Evil. B...
What was the impact of the Battle of the Little Bighorn?
The Battle of Little Bighorn. 25. th. June 1876....
INSTALLING THE 3-3-5 DEFENSE AT THE HIGH SCHOOL LEVEL
DAVID BROWN. HEAD FOOTBALL COACH. NOTRE DAME HIGH...
Chemical Warfare Agents: from 1915 to the present day
. Dr D J Baker. H. ôpital Necker – Enfants M...
European History
History of Northern Europe. Scandinavian Countrie...
Detecting the Undetectable
Roger A. Grimes, Principal Security . Archtect. ,...
BLITZKRIEG
Lesson Objectives . To understand what Blitzkrieg...
Evading Anomarly Detection through Variance Injection Attac
Benjamin I.P. Rubinstein, Blaine Nelson, Anthony ...
INF526:
Secure Systems Administration. Policy Driven Admi...
1. No Criticism---attack or accuse
2. No Contempt---insulting, mocking, eye-rolling....
Controls for Information Security
Chapter 8. 8-. 1. Learning Objectives. Explain ho...
Part 1 - A basic
overview & drill. FETI Drill . 15-1. January,...
Project in Computer Security - 236349
IS-IS Routing Attacks. Supervisor. Gabi Nakibly, ...
EE5900: Cyber-Physical
Systems. Hardware and . IoT. Security. Lin Liu a...
Defending against Sybil Devices in Crowdsourced Mapping Ser
Gang Wang, . Bolun Wang. , . Tianyi. Wang, Ana ....
Security of Message Digests
CSCI 5857: Encoding and Encryption. Outline. Atta...