Search Results for 'Attack Retreat'
Attack Retreat published presentations and documents on DocSlides.
Rob Pollock, Sr. Channel Sales Manager
Data Connectors November 9, 2016. Misconceptions...
Program Executive Officer (PEO)
Review and . Outlook. Brig Gen Shaun Q. Morris. A...
The Longbow and the Gunpowder Revolution:
A Study in Military Innovation. With reference to...
Table of
contents. Aneurysm. Dissection. Heart. . A. rrhy...
The Dark Menace:
Characterizing . Network-based . Attacks in . the...
Public Wi-Fi Badness
Presented by:. General Overview of Provider Wi-Fi...
Blenheim
. August 13, 1704. Strategic Context. England, a...
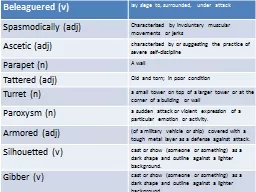
Beleaguered (v)
lay siege to, surrounded,. under attack. Spasmod...
All Your Queries Are Belong to Us:
The Power of File-Injection Attacks . on Searchab...
[Restricted] ONLY for designated groups and individuals
Latest threats….. Rolando Panez | Security Engi...
Chrono
Shift. By: . chamu. R., Christian f., . shirley...
Major Battles/ End of the War
Allies / Axis. Blitzkrieg technique. Battle of Br...
The Early Battles in the Pacific
Semester 2. Week . 4. The Japanese Attack the Phi...
Hastings
October 14, 1066. Strategic Context. King Edward ...
Coastal Management
G3.4 . Key terms. Hold the line: Maintaining the ...
Network Security
Chapter 3. Panko. and . Panko. Business Data Net...
Events and Ideas #4
Eisenhower and the Cold War. U.S. History – Uni...
Reasoning About the Knowledge of Multiple Agents
Ashker Ibne Mujib. Andrew Reinders. 1. The Classi...
Weekend Yoga Retreat – Summary of Themes
Earth. Air. Fire. Water. Intention. I am groundin...
Aim The
battlefield strategies & methodologies define...
Adrianople
. August 9, 378. Strategic Context. Under pressu...
Revision Checklist:
1. What do I need to revise; . Revised once. Revi...
Intrusion Detection Research
Stephen Huang. Sept. 20, 2013. News. 2. http://ar...
CSE 30341
Operating System Principles. Security. Security. ...
Clash of Clans
Price. : . Free. Category. : . Games. Size. :. ....
Coastal retreat
Key Idea 2.8 . Lesson 1 of 2. Coastal Retreat. Le...
Passport To Manhood Retreat 2015
Passport to Manhood Retreat. 2015. Good morning t...
Royalist Army Formations
Assistance . with Animation of Power Points kindl...
Touching Spirit Bear
Study Guide. . Review Correct Answers . Who . ...
Confirmation
Decision point- The Holy Spirit . Orientation 20...
A conspiracy theory
explains an event as being the result of an all...
By: Rachel Moore, Astika Joshi, Noah Wong, Selena Ando, Aar
Battle of Verdun . “Bleed the French white”. ...
Sea Hunter
PLAY. DON’T PLAY. PLAY. You must play this. PLA...
Cryptanalysis
Kyle Johnson. Cryptology. Comprised of both Crypt...
Practical Aspects of Modern Cryptography
Josh Benaloh. Tolga Acar. Fall 2016. October 25, ...
Network Layer Security
1. Outline. IPsec. Security in Routing. DDoS at N...
Military Robots
James C. . Blackmon. ‘Ethics, War, and Robots�...
CYBER TERRORISM
Submitted by:. Abhashree. . Pradhan. 0501227096....
Defending against Sybil Devices in Crowdsourced Mapping Ser
Gang Wang, . Bolun Wang. , . Tianyi. Wang, Ana ....
1 SENSS
Security Service for the Internet. Jelena Mirkovi...




![[Restricted] ONLY for designated groups and individuals](https://thumbs.docslides.com/528549/restricted-only-for-designated-groups-and-individuals.jpg)