Search Results for 'Accepts Random'
Accepts Random published presentations and documents on DocSlides.
Numerical Methods for Empirical Covariance Matrix Analysis
Miriam Huntley. SEAS, Harvard University. May 15,...
Genetic Algorithms
Chapter 3. GA Quick Overview. Developed: USA in t...
Linear Cryptanalysis of DES
M. Matsui.. Linear Cryptanalysis Method for DES C...
Secrets & Lies, Knowledge & Trust.
(Modern Cryptography). COS 116, Spring . 2012. Ad...
Cryptography
Lecture 1. Arpita. . Patra. Welcome to the secon...
Cryptology
Passwords . and Authentication. Prof. David . Sin...
PHA Bioplastics
Synthesis and Material Properties. University of ...
Commensal
Cuckoo. : Secure Group Partitioning for Large-Sc...
How many daisies?
Aims. To understand how scientists count . organi...
Better Pseudorandom Generators from Milder Pseudorandom Res
Raghu Meka (IAS). Parikshit Gopalan, Omer Reingol...
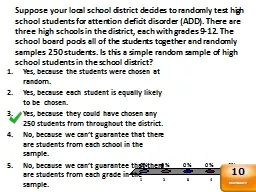
Suppose your local school district decides to randomly test
Yes, because the students were chosen at random.....
Session 4
Asymmetric ciphers. Contents. Definition of asymm...
Decoupling with random quantum circuits
Omar Fawzi (ETH Zürich). Joint work with Winton ...
Symmetric-key algorithms
Symmetric-key algorithms. use the same cryptograp...
Authentication
Authentication with symmetric key. Server sends r...
Explaining
Matlab’s. Axis Alignment. When it deems it pra...
Anatomy of Attack: Code Red
Dan Fleck. CS 469: Security Engineering. These sl...
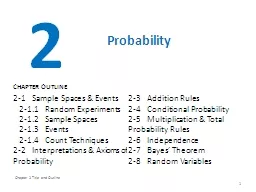
Chapter 2 Title and Outline
1. 2. Probability. 2-1 Sample Spaces & Even...
In addition, the IOC will conduct further random and unannounced tests
). As with previous editions of the Games, sample...
Data Destruction
How to Erase your Hard Drive’s so that there is...
Zipf’s
monkeys. Observations from real and random genom...
DeepFont
: Large-Scale Real-World Font Recognition from Im...
Evolutionary Mechanisms
Genetic Drift (and Inbreeding). DEVIATION. . fro...
1 Econometrics
Advanced . Panel Data Techniques. 2. Advanced Pan...
Secure Storage
1. Lost Laptops. Lost and stolen laptops are a co...
Chapter 4 Title and Outline
1. 4. Continuous Random Variables and Probability...
CS b553
: A. lgorithms . for Optimization and Learning. M...
Probability Density Functions
Jake Blanchard. Spring 2010. Uncertainty Analysis...
Uncertainties
Problem Solving class 1 for Physics 1A and Higher...
FUNDAMENTALS of ENGINEERING SEISMOLOGY
GROUND MOTIONS FROM SIMULATIONS. 1. Observed data...
Odds and ends
Key Derivation. Online Cryptography Course ...
Statistics and Data Analysis
Professor William Greene. Stern School of Busines...
Although much attention has been given in recent years to tracing the
shocks and random fluctuations than those based on...
General Database
Statistics . Using . Maximum Entropy. Raghav. Ka...
Packed Column Internals
Packed Column. Factors Favoring . P. acked . C. o...
Piloting and Sizing Sequential Multiple Assignment
Randomized Trials in Dynamic Treatment Regime Dev...
CRICOS No. 00213J
Deterring Drug Drivers: A Study into the Initial ...
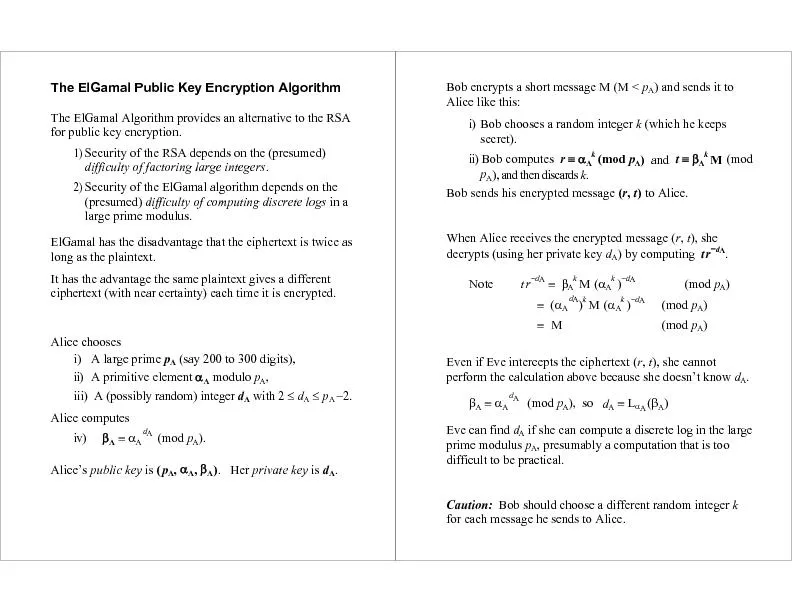
Security of the RSA depends on the (presumed) 2) large prime modulus.
i) Bob chooses a random integer ii) Bob computes ...
DieHard
: Probabilistic Memory Safety for Unsafe Language...
DieHard
: Probabilistic Memory Safety for Unsafe Language...