Search Results for '(employee User'
(employee User published presentations and documents on DocSlides.
Place indicators in the areas of the pack or load least accessible to
HiMedia Laboratories Technical Data User must ensu...
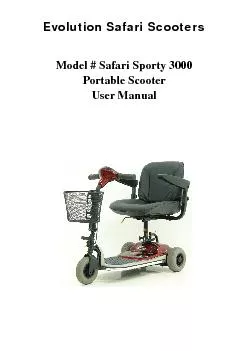
volutionSafariScooters 1 Model#SafariSporty3000 PortableScooter User
volutionSafariScooters 2 INTRODUCTION 3 FEATUREG...
Protecting Your Data
with Containers . without Boxing Yourself In. Yog...
Spry Menu Bar allows you to add very user-friendly dynamic menus that
Image Rollovers Form Validation Open new browser w...
2011 Vaddio - All Rights Reserved. Squiggle - Video Whiteboard Kit -
Installation and User Guide VADDDDIIOO
Squiggles Seating System User Instructions
designed to offer a high level of postural positio...
DOT Urine Collection and Breath Alcohol Testing Procedures
Mock Demonstrations and Review of Recent Applicab...
breeze-online.com
Inspections on an iPad, iPhone, iPod Touch, Andro...
Financial Data User Group Meeting
Terrace Room, Claudia Cohen Hall – October 21, ...
prove employee health by implementing a StairWELL initiative within th
also provides options for businesses that do not h...
Online Identity Authentication and Data Broker
SNAP Director’s Conference . September 23, 2013...
Innovation is at hand.Continual improvement throughinnovation. The ful
The user-friendly design of 3Mstaples which allow ...
User’s Guide
Localization system StarGazer TM for Intelligent ...
SWIFT & TARGET2
Event Name. Name. Date. Presentation title – d...
Web Browsers
And Mobile Web Browsers. Guiding Questions. What ...
CC3100SimpleLink
GettingStartedGuide User'sGuide LiteratureNumber:S...
Security
and . Privacy-preserving . Applicatio...
Facilities Pilot Buddy Program
2020 Goals:. Attract, Retain & Reward Top Peo...
Simple Buffer
Overflow Example. Dan Fleck. CS469 Security Engin...
Software Security
Chapter. 15 : . Attacking. . Compiled. Applica...
July 2013 Microsoft Security Bulletins
Jonathan Ness. Security Development Manager. Dust...
October 2013 Microsoft Security Bulletins
Jonathan Ness. Security Development Manager . Dus...
Bureaucracy – a large, complex organization composed of a
United States has three aspects of constitutional...
e.g .
Click & Collect penetration variation. Some c...
BUSINESS ADMINISTRATION
- . Prof. Sonam Bhayani (B.com/. Mba. ). BUSINESS...
DEALING WITH DIFFICULT PEOPLE
or. DON’T YOU JUST LOVE THIS JOB???. Karen B. ....
HR & Finance Issues in a declining economy
Ebonee Davis, Michelle Chapekis, Lianne Young, Je...
Expert Briefing Session
Employee Buyouts - Ewan Hall, . Baxendale. 4 Febr...
Drug User Peace InitiativeStigmatising People who Use DrugsIntroductio
1 ‘Drug use’ should be taken to refer t...
“ The benefits of paid sick leave extend far beyond the p
- Mayor Bill de Blasio. What we will cover. Ove...
Tall Oaks Tree House Campsite
Andrea Lawson . Introduction . Located in Frederi...
Smart Cane – P14043
Systems Design Review. Lauren Bell, Jessica Davil...
Smart Cane – P14043
Sub-Systems . Design Review. Lauren Bell, Jessica...
Smart Cane – P14043
Lauren Bell, Jessica Davila, Jake Luckman, Willia...
After the Canvass
ePledge. A . tutorial. for canvassers: . Assisti...
By Toby Reed
. E-Mail. What is E-Mail?. Email stands for ‘e...
Ryan hickling. What is an email. An email message...
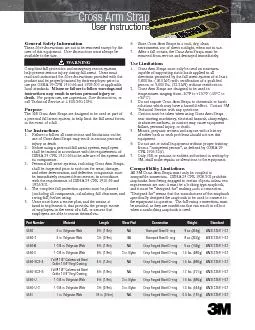
Cross Arm Strap
User Instructions Part NumberMaterialLengthWear Pa...
Information Security
4. Identify the . five . factors that contribute ...
7 Information Security
Introduction to Information Security. Unintention...