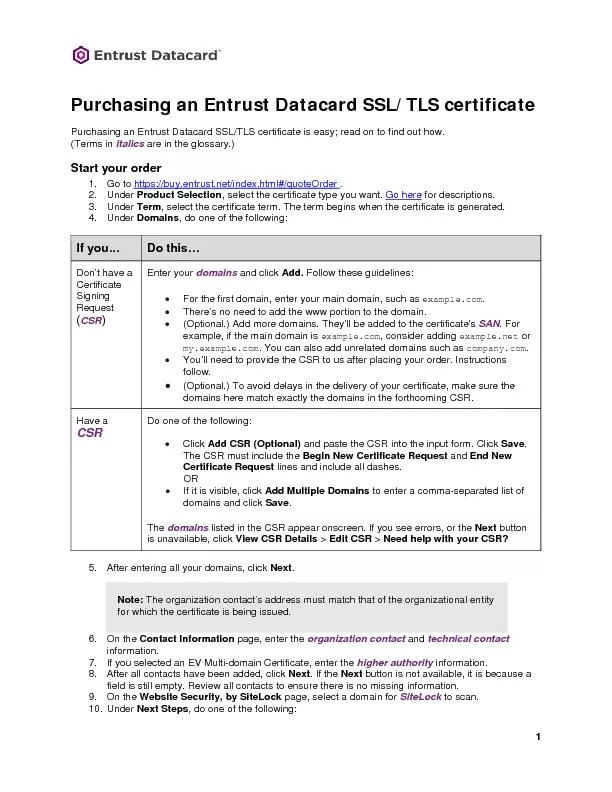
PDF-Purchasing an Entrust Datacard SSL/TLS certificatePurchasing anEntrust
1 for descriptions
Under Term select the certificate term The term begins when the certificategeneratUnder Domains do one of the following
If you133
Do this133
Don146t
Download Presentation
"Purchasing an Entrust Datacard SSL/TLS certificatePurchasing " is the property of its rightful owner. Permission is granted to download and print materials on this website for personal, non-commercial use only, provided you retain all copyright notices. By downloading content from our website, you accept the terms of this agreement.
Presentation Transcript
Transcript not available.